A Single Platform to Secure & Manage {animated_text}
DISCOVER
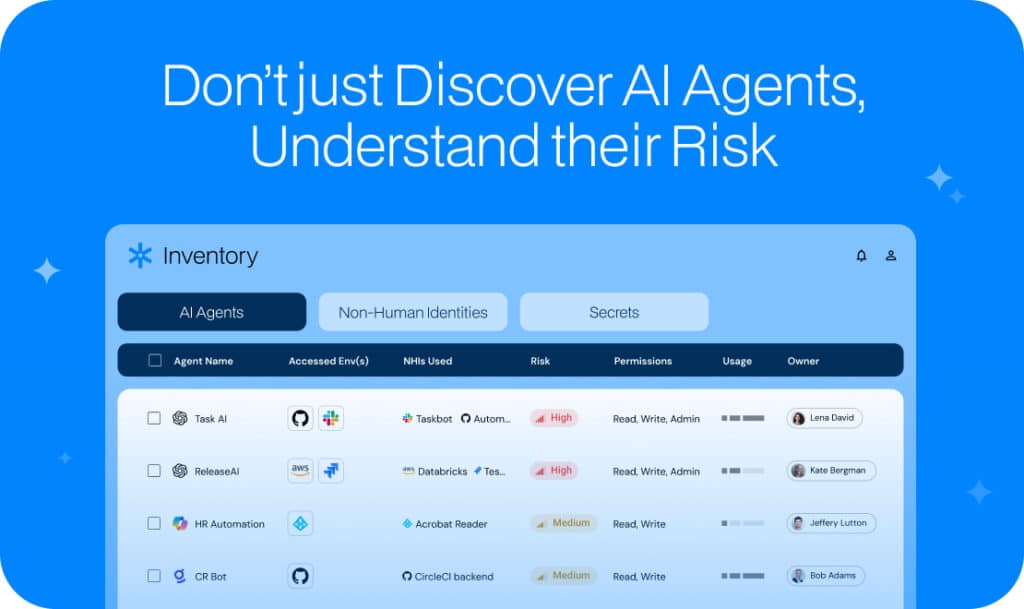
AI agent visibility and context
A single inventory
We connect to your environment in minutes and automatically discover:
- AI agents—custom, third-party, or home-grown. Managed and shadow agents.
- MCP servers.
- NHIs—service accounts, OAuth apps, API keys, SSH keys, IAM roles, and more.
- Secrets – inside and outside your vaults.
Deep context
Our Identity Graph shows which platforms and resources AI agents can access, who created them, their permissions and tokens, and who else can access them.
Risk prioritization
Prioritize remediation with automated risk scoring, with rich context on resources AI agents and NHIs can access, their permissions, usage, owners, and security findings (IOCs, anomalies, weak authentication, etc.)
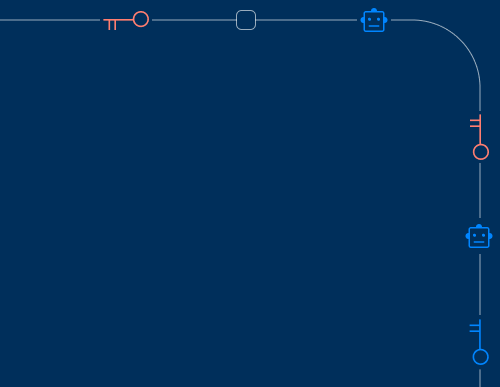
Connectivity map
We correlate data across cloud, SaaS, on-prem, databases, Vaults, CI/CD, and AI platforms to uncover shadow agents and their owners—including those hidden behind tokens, ephemeral sessions, and SaaS apps.
SECURE
Identify and remediate risky agents & NHIs
Posture management
Proactively strengthen your agent security by reducing excessive privileges, fixing configuration weaknesses, and automatically assigning human ownership for each agent.
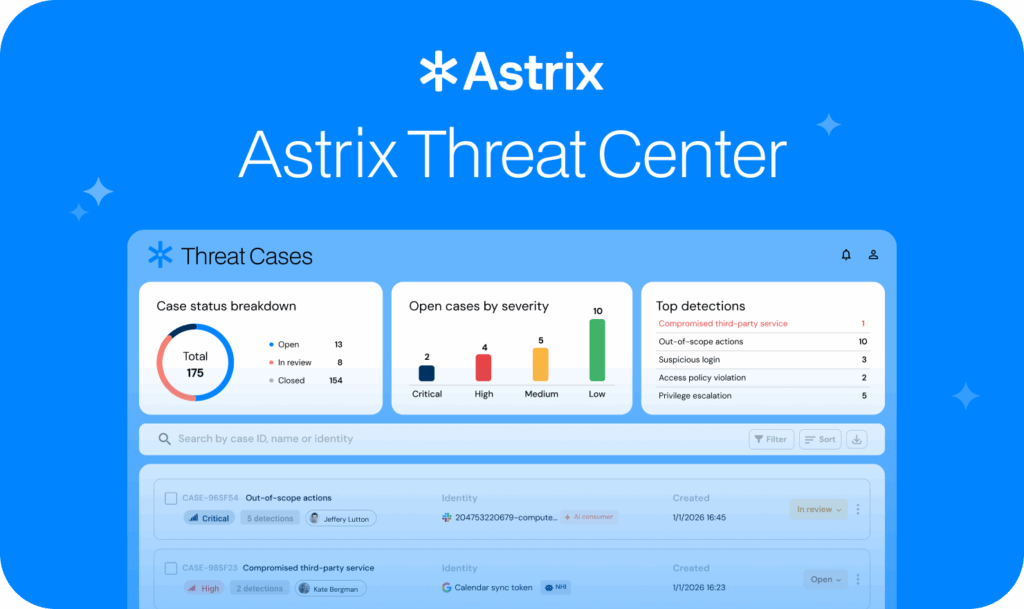
Threat detection
Rapidly identify suspicious activity involving AI agents and NHIs through unusual patterns, unauthorized actions, and compromised identities.
Remediation
Fully automate quick fixes, safe rotation workflows, and owner-aware processes without breaking functionality. Integrate seamlessly with your ITSM, SIEM, and SOAR tools.
DEPLOY
Deploy secure-by-design AI agents
Astrix’s Agent Control Plane enables secure-by-design AI agents by applying Zero Trust policy at creation, allowing you to enforce the use of short-lived credentials and maintain a complete audit trail for every agent’s access. Each agent operates with least-privilege, precisely scoped access to only what is required.
ONBOARDING
Onboarding takes 5 minutes
Agentless
We are a non-proxy API-based solution.
Metadata only
We respect your privacy by reading metadata only and asking for minimal permissions.
Easy to deploy
Connect us to your environments in minutes with a few clicks.
Use Cases
Discovery & governance for AI agents
Uncover shadow agents, maintain inventory, and enforce policies to resolve hygiene issues, reduce attack surfaces, and prevent compliance violations.
Access & lifecycle management for AI agents
Manage AI agents from provisioning to decommissioning. Enforce least-privilege access policies and maintain a full audit trail per agent.
Agentic threat detection & response (ATDR)
Detect & respond to agentic threats such as compromised credentials, abnormal access patterns, and out-of scope agent actions.
NHI security & management
Maintain a continuous inventory of service accounts, OAuth apps, IAM roles, API keys, and more. Automatically identify and remediate stale, overprivileged, or unused NHIs, and rotate or remove them safely without disrupting operations.