Doubloons Defense
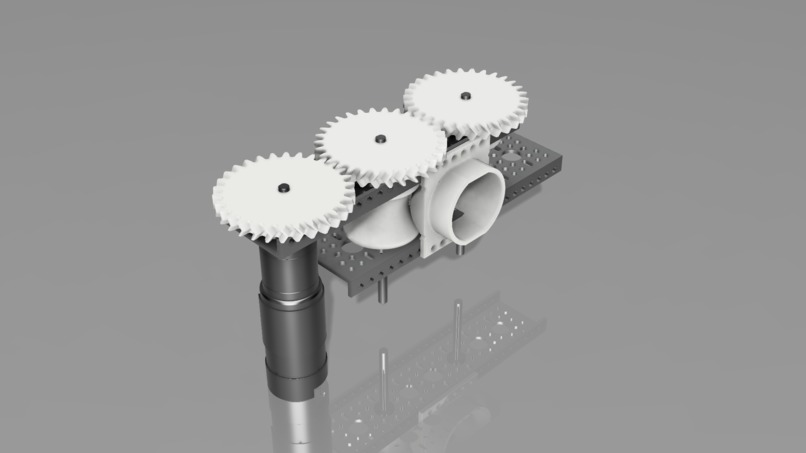
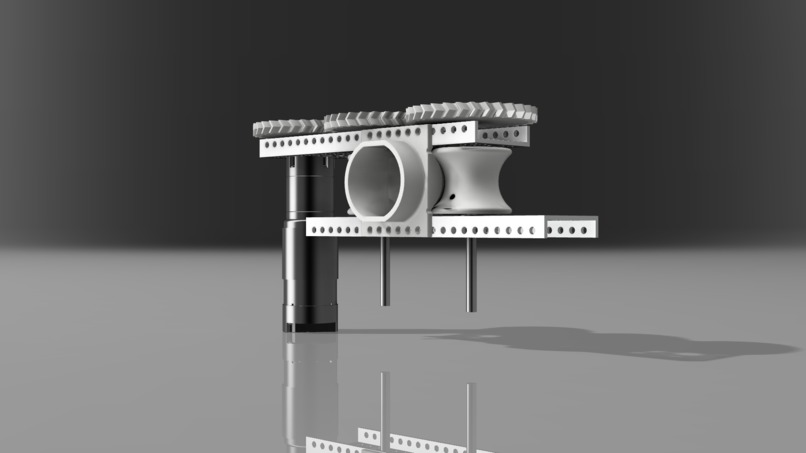
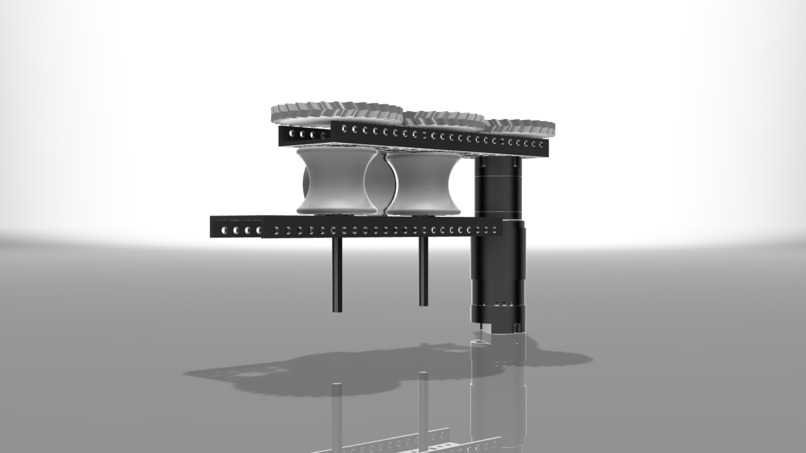
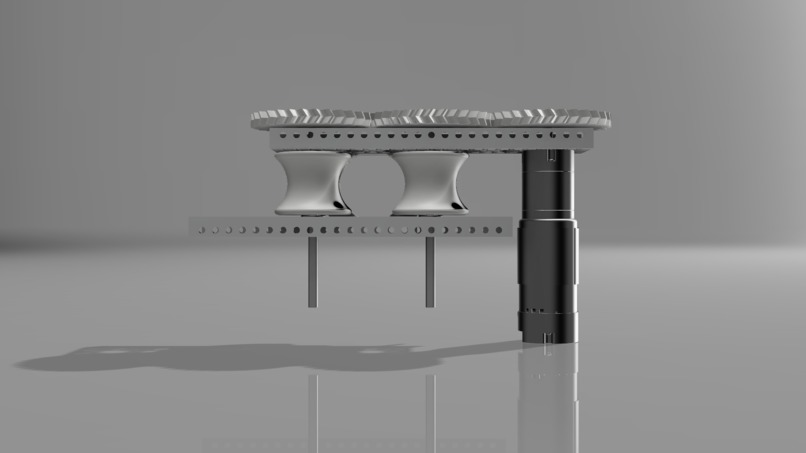
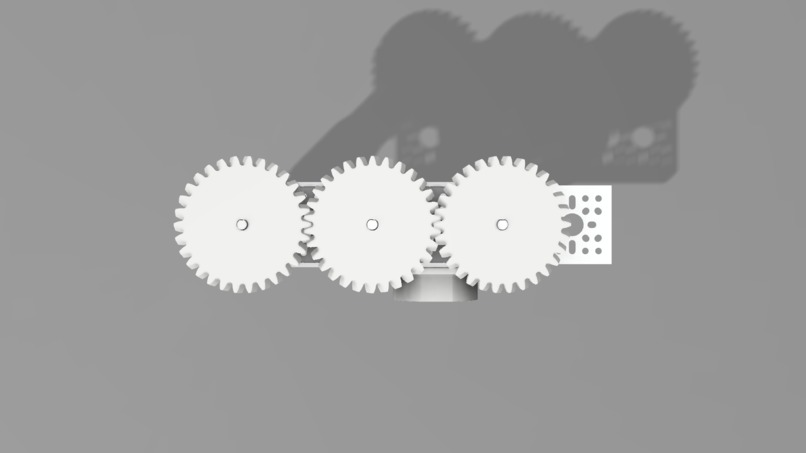
And a Quantum Secure Pirate Cannon (AKA Ping Pong Cannon - Our custom example of real-life scenarios - like the military - where this type of encryption would be extremely useful and necessary). The cannon also fits the pirate theme and shows how it's important to protect dangerous weapons from being hacked into!
Inspiration
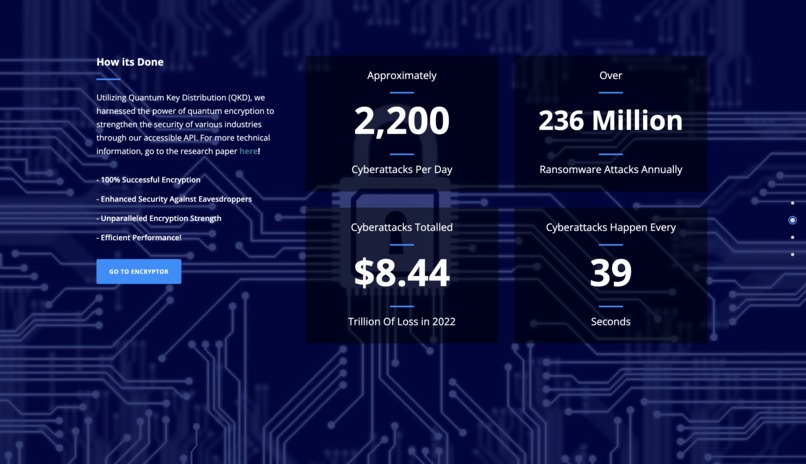
Our inspiration for the Doubloons Defense project stemmed from our education on cyberattacks and cybersecurity during our time in school. We learned about the increasing threats posed by hackers and the critical need for robust security measures in various industries. Motivated to extend our knowledge and contribute to real-life solutions, we embarked on developing a system to address these challenges.
What it does
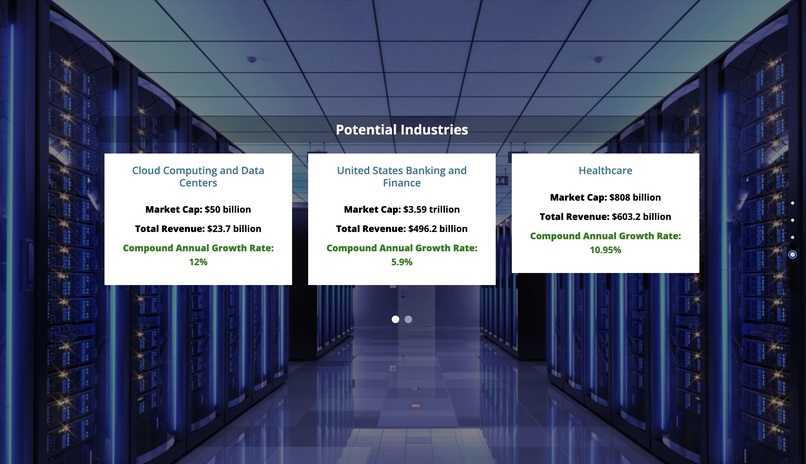
Doubloons Defense utilizes SimulaQron's quantum internet SDK and leverages Quantum Key Distribution (QKD) encryption to transmit virtually uncrackable messages. Our solution achieves a remarkable success rate of 94% in secure message transmission.
How we built it
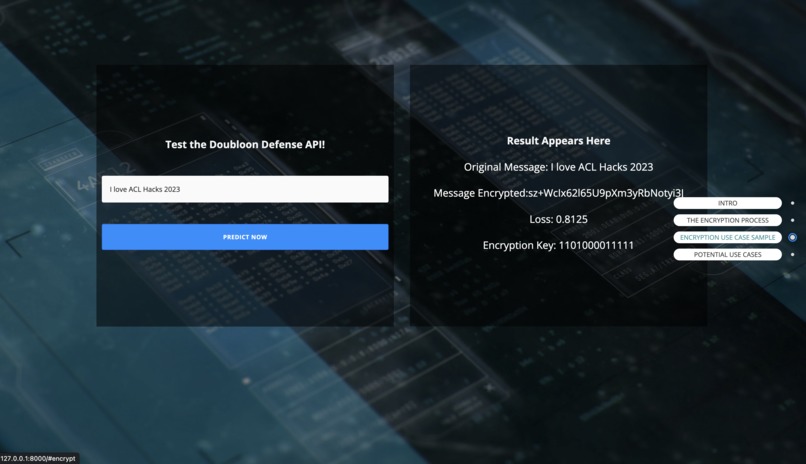
We employed SimulaQron's SDK and Qiskit to implement the quantum computing aspect. These powerful tools enabled us to harness the potential of quantum computing in securing our communication system.
For the website and backend, we utilized Django and Python. These technologies facilitated the creation of an intuitive and user-friendly interface, ensuring seamless integration with the rest of our solution.
In addition, we employed computer-aided design software (Fusion 360) to help us quickly model and simulate our design and 3D printing to develop a visually appealing and functional prototype 3D model of our Quantum Secure Pirate Cannon to showcase a potential use case of QKD.
Challenges we ran into
During the development process, we encountered several challenges that tested our problem-solving skills. One significant hurdle was the time-consuming nature of actual quantum computing using quantum computers. As it often takes hours to perform quantum computations, we needed a quick and efficient solution to simulate the process for the sake of demonstration.
Another challenge arose when we encountered repeated failures in 3D printing. Despite our efforts, the printer consistently faced issues that hindered the successful completion of the 3D model.
Accomplishments that we're proud of
Despite the challenges we faced, we are proud to announce that we successfully completed the Doubloons Defense project. We have achieved a deployable and production-ready solution that addresses the critical need for enhanced cybersecurity. Our solution provides industry professionals with a reliable and highly secure method of transmitting sensitive information, ensuring protection against cyberattacks.
What's Next for Doubloon Defense
The future of Doubloons Defense is filled with exciting developments aimed at further strengthening information security. We have a roadmap of innovative projects in the pipeline, including:
Quantum Algorithm Research: Our team is actively engaged in researching and developing advanced quantum algorithms tailored specifically for encryption and secure communication. These algorithms will leverage the power of quantum computing to enhance the unbreakable encryption provided by Doubloons Defense.
Integration with IoT Devices: We are working on expanding the compatibility of Doubloons Defense with a wide range of Internet of Things (IoT) devices. This integration will enable seamless and secure communication between IoT devices, providing a robust shield against potential cyber threats in smart homes, industrial automation, and beyond.
Enhanced User Experience: Our focus is not only on security but also on providing a seamless and user-friendly experience. We are dedicated to refining the Doubloons Defense interface, streamlining processes, and incorporating user feedback to ensure a smooth and intuitive experience for individuals and industries relying on our solution.
Partnerships and Collaborations: We are actively seeking partnerships with industry leaders, research institutions, and quantum computing experts. These collaborations will foster knowledge exchange, accelerate advancements in information security, and enable us to leverage state-of-the-art technologies for continuous improvement.
Built With
- 3d-printing
- autodesk-fusion-360
- django
- python
- qiskit
- quantum



Log in or sign up for Devpost to join the conversation.