Inspiration
Cybersecurity—and especially the niche of Digital Forensics—has long been associated with notoriously unapproachable user interfaces, difficult user experiences, and confusing application flows. From bloated, messy logs to outdated design trends, there are plenty of reasons for this reputation. As we discussed problems we were passionate about solving, a common thread emerged from our diverse professional and technical backgrounds. Many mission-critical tools in Digital Forensics are nearly impossible for amateur or untrained users to navigate, too intimidating to encourage broader adoption, and simply unenjoyable to use. By combining our team’s strengths in graphical design, user experience, and cybersecurity engineering, we created Forens.tech—an application designed to change that narrative.
What it does
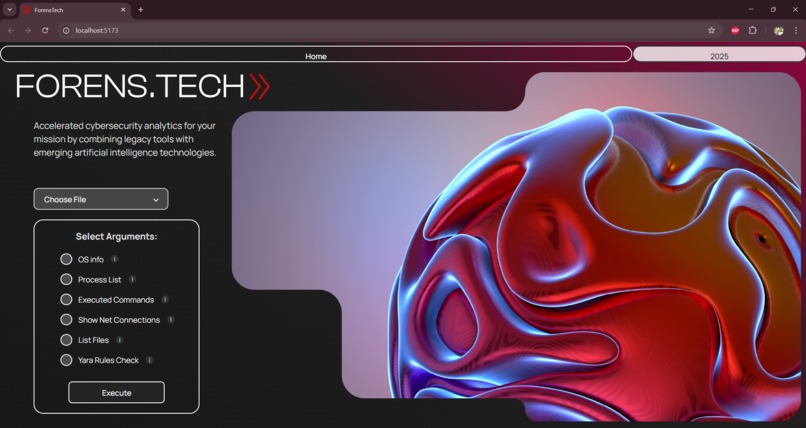
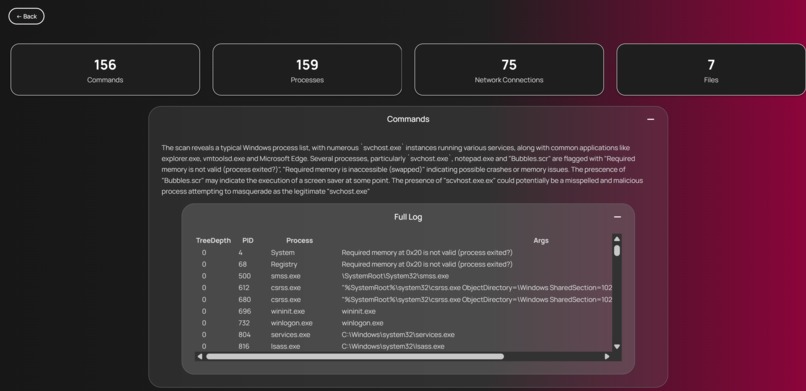
Forens.tech takes an innovative approach to common digital forensics techniques—combining a fresh, well-planned, and deliberate user experience with reliable methods to quickly parse and display memory dump data. Forens.tech is a web application that runs locally on a customer’s system, alongside any memory dump files they wish to analyze. It offers a straightforward, easy-to-follow selection process for choosing the types of scans to run on the selected file, using those inputs to execute Volatility3 for analysis. The application outputs a consistently clean and structured JSON result, which is then passed to a Gemini-powered LLM agent for summarization and deeper insight. This includes both objective data and a cleaned-up version of the command output, all presented clearly to the end user. Using Volatility3, Forens.tech can offer options for analysis on a system’s running processes, conducting a file scan of the computer, getting OS information, viewing network connections, and returning a list of executed system commands. The goal is to simplify memory dump analysis, making it more accessible to a wider audience of law enforcement and blue team specialists. Along with this focus, utilizing tools like Volatility3, Forens.tech can offer a wide range of expanding options to analyze data from the position of beginners to experienced professionals.
How we built it
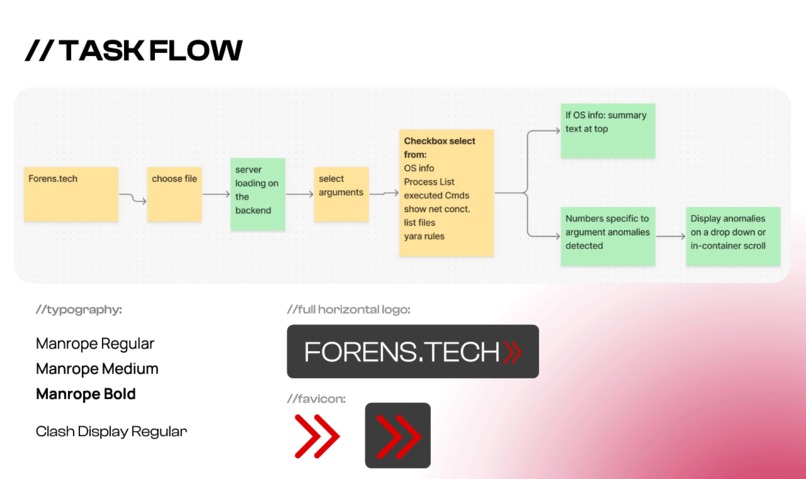
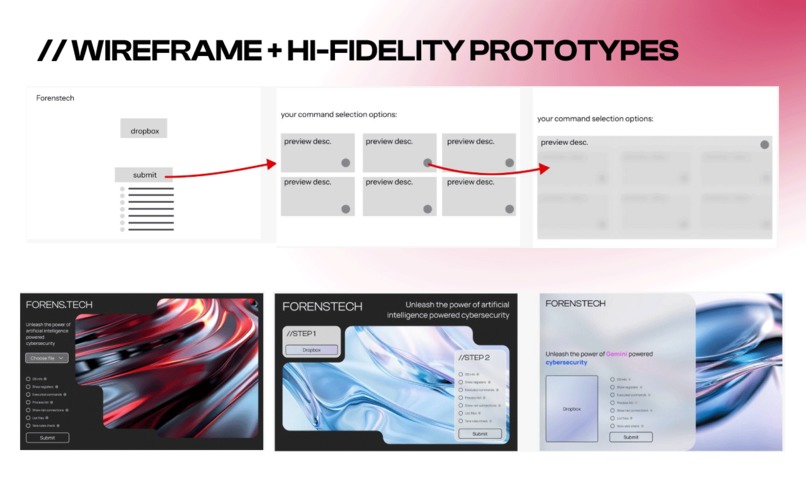
Forens.tech’s front end was built using ReactJS and custom CSS after analyzing multiple design features with prototypes using Figma. As a team, we had to think about who the intended end-use_r was and their unique descriptors, such as location, age, mental states, and hobbies. To be on the same page of things, we collectively created the _task flow in FigJam. Following that, we created the wireframe, this helped us figure out what was capable on both sides of the front-end development and back-end development. Then, we took into account typography, contrast checking, coloring, and style guides to then land on the high fidelity prototypes. We made sure that these prototypes were user-friendly and accessible to the intended user personas. For back-end, Volatility3 is called through a Python script, which pushes output through fastapi to serve mission-critical information to the end user.
Challenges we ran into
One major challenge was using Volatility and learning to work with memory dumps, both of which are things none of our team members had prior experience with. Luckily, both the documentation and usage are relatively straightforward and well-maintained, allowing for the creation of our automated scripts to come after a few hours of initial research.
Accomplishments that we're proud of
Our team is incredibly proud of how well the interface came out for Forens.tech. Although it was difficult at times, ensuring to build with a focus on the user interface and being deliberate with our design decisions helped us to create a good-looking and good-performing web application..
What we learned
In addition to deepening our understanding of memory dumps and how tools like Volatility3 support cyber professionals in incident response, we also gained valuable insight into the importance of planning and preparation—and the significant impact they have on the quality of an application’s visual design, cognitive psychology, and user interface.
What's next for Forens.tech
Expanding support for further and more advanced Volatillity commands as well as support for other digital forensics tools and combine this extra information with even cleaner data logging methods.

Log in or sign up for Devpost to join the conversation.