Inspiration
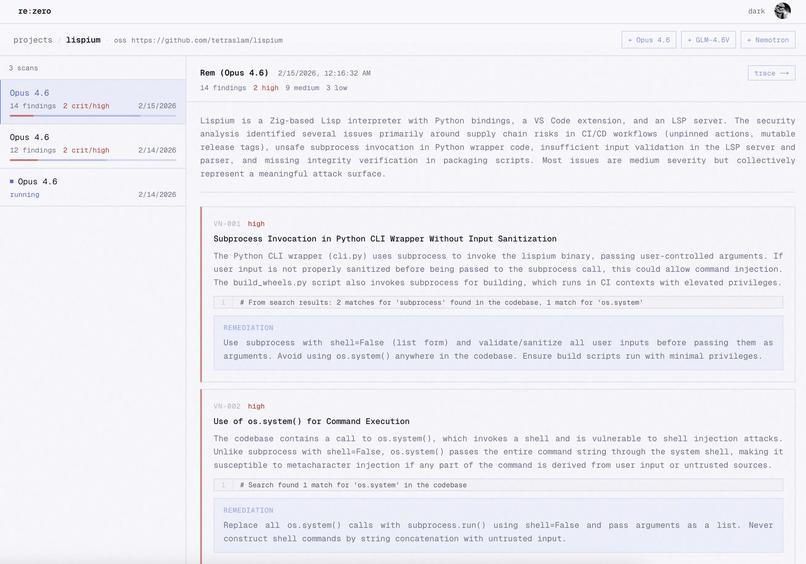
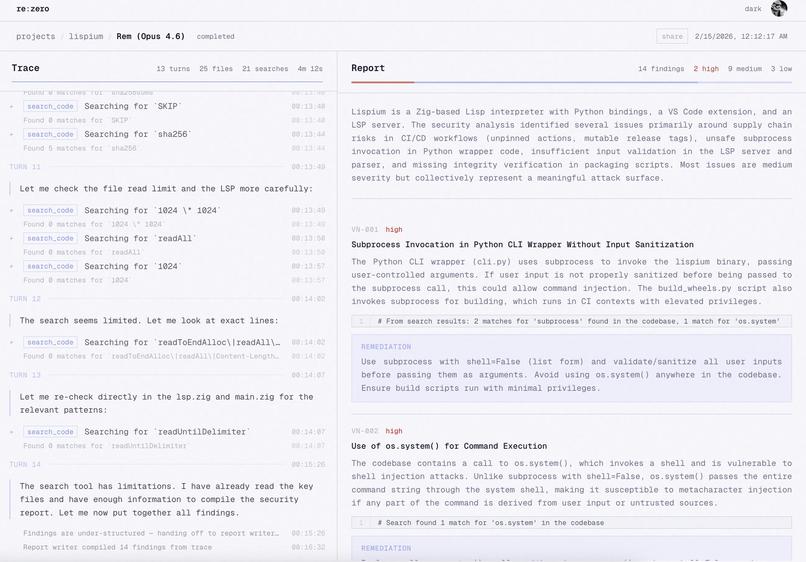
A week ago, Anthropic released Claude Opus 4.6 after disclosing that it found 500+ vulnerabilities in many popular, well-tested open-source repos/software. We wanted to extend this to EVERY target possible, so that we can improve security faster than agents degrade it.
What it does
It's a platform with an agent named Rem who will reverse-engineer and penetration test anything. For websites, this includes your public site and also authed routes if you give Rem test credentials. She'll even handle 2FA codes by asking you for them when she hits that snag! We used Browserbase/Stagehand for this. For OSS repos, we clone the repo to a Modal sandbox and have Rem run a series of vulnerability tests and just manual exploration of the code to analyze attack surfaces. For hardware, we also use sandboxes to give Rem a scratchpad with which to interact with hardware like drones, webcams, ESP32s, etc. She also has access to an FPGA with a program which can analyze power fluctuations in a device running AES-256 encryption (government comms, financial systems, cloud storage, VPNs, smartphones, etc.) and decrypt their key by measuring the fluctuations in power on the device running encryption.
How we built it
We reverse-engineered the drone by tapping into its wireless protocol and emulating its app's signals to take control of the drone's flight. We also reverse-engineered a webcam by modifying its drivers. For inference and agent sandboxes, we used Modal GPUs, Sandboxes, volumes, and services. All our RL environments use prime-rl environments from Prime Intellect's Environments Hub, and we specifically focused on CTFs, phishing detection, vulnerability detection, and code security. We served our custom-trained models using vLLM running on Modal.
Challenges we ran into
Reverse engineering is not universal, as hardware contains different entry points and different protocols that does not have to be standardized. It was difficult to build a system for distributed reverse engineering. Training the model was also challenging because we had to build and train on our own dataset of phishing scams and GitHub bugs and vulnerabilities across 5 environments.
FPGAs are impossibly hard to work with, and our drone has a stabilization problem which we did manage to fix. Tying everything together in a cohesive platform was marvelous but deathly hard because of the really different stacks different targets use.
Also, we ran reinforcement learning on an open Nvidia model (OpenReasoning-Nemotron-14b) on cybersec and pentesting, and that was our first pass on a pretty large rollout of GRPO on any model. We used Prime Intellect's (https://primeintellect.ai) stack for RL and verifiers, and Modal for compute.
Accomplishments that we're proud of
- Rem was able to reverse engineer a drone and a webcam
- Kenneth and Rem cracked AES-256 encryption, which is one of the most widely-used encryption protocols in the world
- Rem found several hundred zero-days in OSS repos which we are disclosing to their maintainers directly
- Rem also found at least 22 REALLY bad exploits on Shresht's personal website (https://tetraslam.world) which he will be fixing right after this hackathon, or so he swears
What we learned
How firmware is implemented and used in conjunction with software. IoT device safety is at greater risk because of AI, even going down to electrical signals. One could steal encryption keys by tapping into a chip's voltage line and monitoring timing fluctuations going through FPGA logic gates.
Hardware is cool but agents reverse engineering hardware is even cooler.
What's next for re:zero
We have everything set up but payments. We only have $200 in Claude API credits remaining so we'll probably set up a Stripe account and see how people like this, especially since it seems highly useful for indie devs and small-scale usage with outsized impact on their security.
We'll also be open-sourcing several third-party SDKs we've now created to interface with the variety of hardware that Rem was able to reverse-engineer.
Built With
- anthropic
- browserbase
- claude
- convex
- fastapi
- nvidia
- nvidia-nemotron
- prime-intellect
- python
- systemverilog
- typescript
- vercel
Log in or sign up for Devpost to join the conversation.