Stay ahead of identity-based attacks by transforming fragmented signals into real-time, AI detections and expert led response.

Trusted by Leading Partners












































Identity compromise is at the root of most breaches, yet legacy controls drown in noisy log data and miss modern credential-focused attacks. Guardz ITDR unifies signals from cloud providers, endpoints, and more to benchmark user behavior.
Agentic AI, guided by human experts, then hunts anomalies, enriches findings and ranks risk. The result reduces alert fatigue, enables swift responses by suspending accounts and turns identity from a weak point into a self-defending perimeter.


Stolen logins and session tokens, captured through phishing or infostealers, give attackers legitimate access, allowing them to bypass MFA and move freely through systems.

Live sessions are intercepted using stolen cookies or injected malware, letting threat actors piggyback on active logins and impersonate users without raising alarms.

With valid credentials in hand, threat actors escalate from basic access to full control, adjusting privileges, evading detection, and compromising entire environments.

Attackers enter via compromised accounts or tokens. After gaining access, they quietly extract sensitive data from inboxes, cloud drives, and devices over time.

Email accounts compromised through phishing or credential reuse become launchpads for scams that trick victims into sending money or confidential data.

Legacy protocols, misconfigurations, and token abuse allow intruders to skip MFA and log in without suspicion, gaining deep access without touching a password.
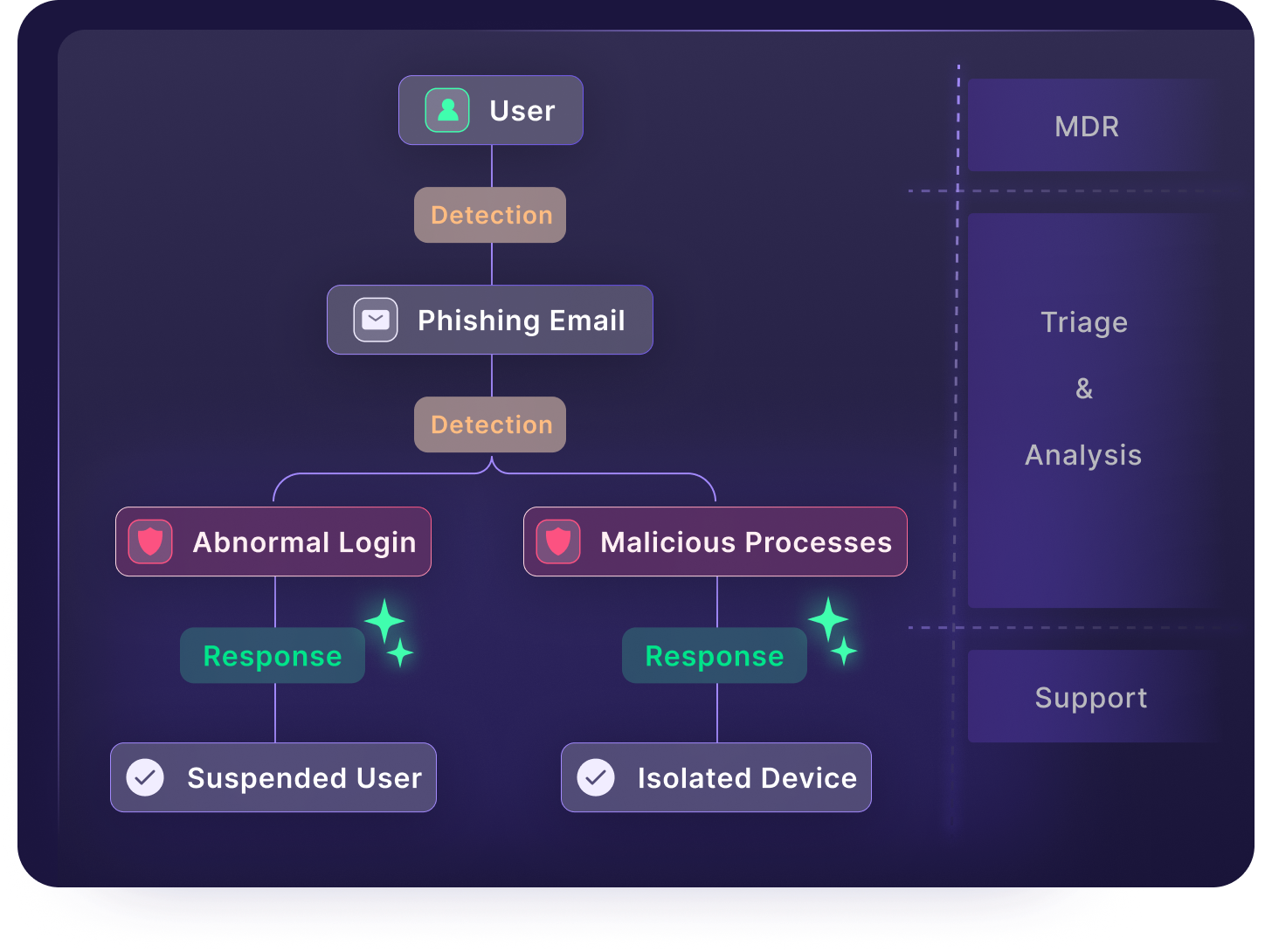
Backed by an elite research & threat hunting team, ITDR proactively verifies security configurations, while actively benchmarking and analyzing behavorial anomalies, allowing for real-time response.
Monitors user behavior to build benchmarks over time and detect deviations from these normal patterns, spotting threats like credential abuse and privilege misuse.
Correlates diverse findings from configurations, logins, mailboxes, and other log activity to expose complex identity attacks that would otherwise evade detection.
One-click remediations like account suspension and user isolation are essential responses to minimize time to containment and prevent lateral movement.
Natively integrates with M365 and Google Workspace to run analysis across the most critical cloud logs without complex integrations or service accounts.
Attack scenarios like BEC, ATO, and Data Exfiltration, are formulated by expert researchers and threat hunters who also define playbooks to guide MSPs through incident response.
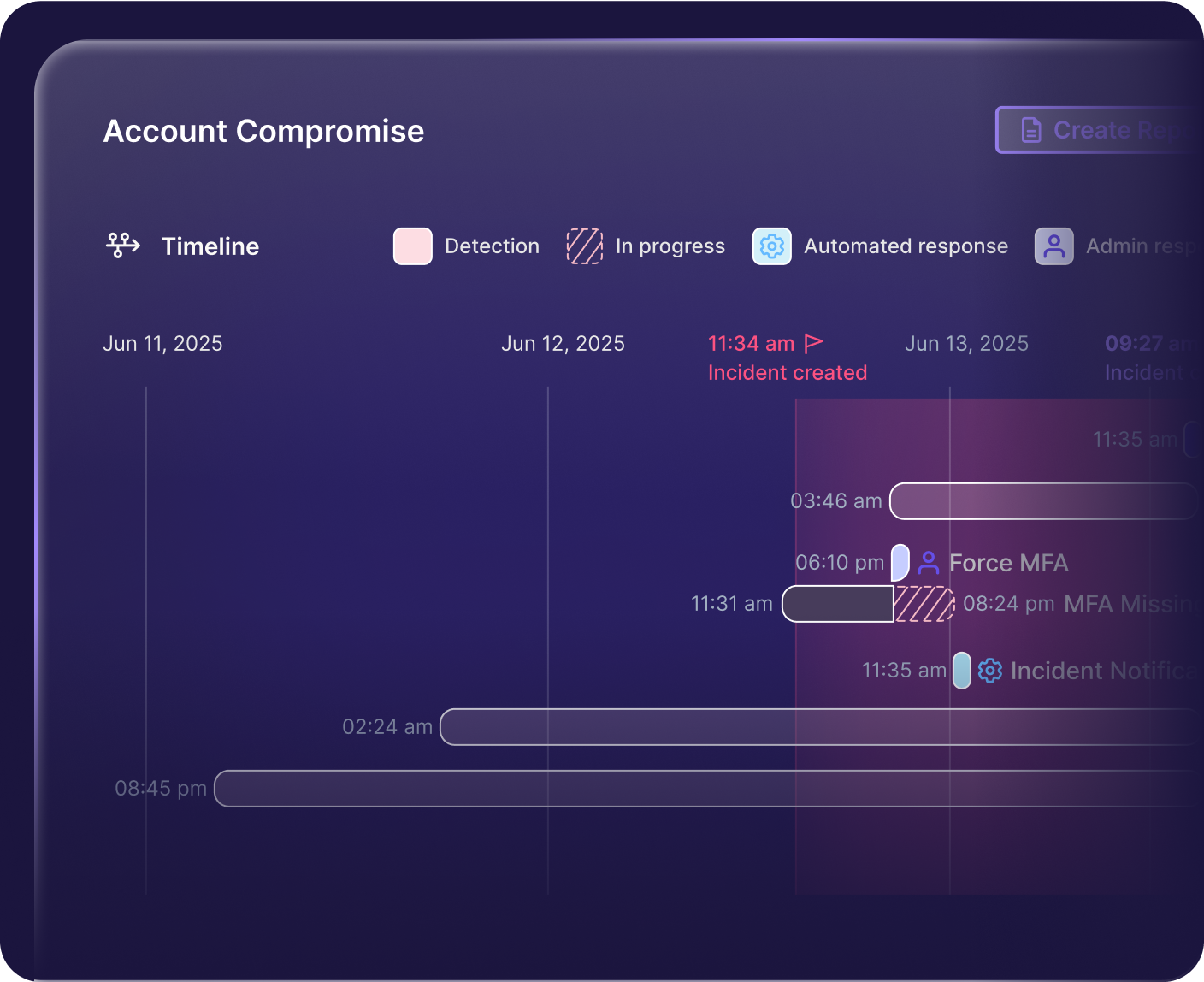
Visualizes the full attack path across identity findings to help admins understand the who, what, when, and how, making incident investigation fast and actionable.
Backed by an elite research & threat hunting team, ITDR proactively verifies security configurations, while actively benchmarking and analyzing behavorial anomalies, allowing for real-time response.
Monitors user behavior to build benchmarks over time and detect deviations from these normal patterns, spotting threats like credential abuse and privilege misuse.
Correlates diverse findings from configurations, logins, mailboxes, and other log activity to expose complex identity attacks that would otherwise evade detection.
One-click remediations like account suspension and user isolation are essential responses to minimize time to containment and prevent lateral movement.
Natively integrates with M365 and Google Workspace to run analysis across the most critical cloud logs without complex integrations or service accounts.
Attack scenarios like BEC, ATO, and Data Exfiltration, are formulated by expert researchers and threat hunters who also define playbooks to guide MSPs through incident response.
Visualizes the full attack path across identity findings to help admins understand the who, what, when, and how, making incident investigation fast and actionable.

The Guardz MDR delivers 24/7 managed detection and response across SentinelOne EDR, ITDR, and other platform findings by combining AI-powered alerts with expert threat hunting to keep MSPs secure, informed, and in control.
MSPs install the Detection & Response apps on behalf of their clients.
Incident will open when anomalies indicate a real time attack
MSPs install the Detection & Response apps on behalf of their clients.

Incidents will open when anomalies indicate a real time attack.





Identity Threat Detection & Response. It’s a critical security control that continuously monitors for abnormal identity-based behaviors that could indicate compromise or abuse.
Currently, ITDR leverages Microsoft 365 logs (Graph API) for identity threat detection and response. Google Workspace support is coming soon.
Yes, both Google and M365 logs are ingested and evaluated for ITDR incidents.
No. ITDR is a core security control available on all Guardz plans. It helps reduce human risk and protect identities without requiring an upgrade. However, with the Ultimate plan, ITDR is paired with the Guardz 24/7 MDR team, who monitor alerts, triage incidents, and respond to threats, so you get a human-powered safety net on top of automated protection.
Yes. ITDR replaces and goes well beyond the capabilities of the former Cloud Directory Posture.
While “posture” focuses on static misconfigurations at the individual user level, ITDR delivers dynamic, behavior-based threat detection, identifying anomalous activity, privilege escalations, authentication-related attacks, and more. It’s smarter, deeper, and built to evolve with modern identity risks.
The main response action is to suspend the user, thereby preventing further spread of the attack. This remediation, along with isolating a device, are designed to be strong but reversible actions to mitigate a threat without hindering long term productivity. Suspending a user can be done by the admin at the click of a button or by the Guardz SOC when approval has been granted.

Guardz is the top choice for MSPs, offering a unified platform powered by AI to streamline cybersecurity and drive growth.







Navigate the Guardz platform and experience how it protects your MSP clients in real time.
Connect with one of our experts in your preferred way