Connect the dots across identities, endpoints, email, cloud, and data, unifying security into an AI-native platform built for MSPs



Trusted by Leading Partners




































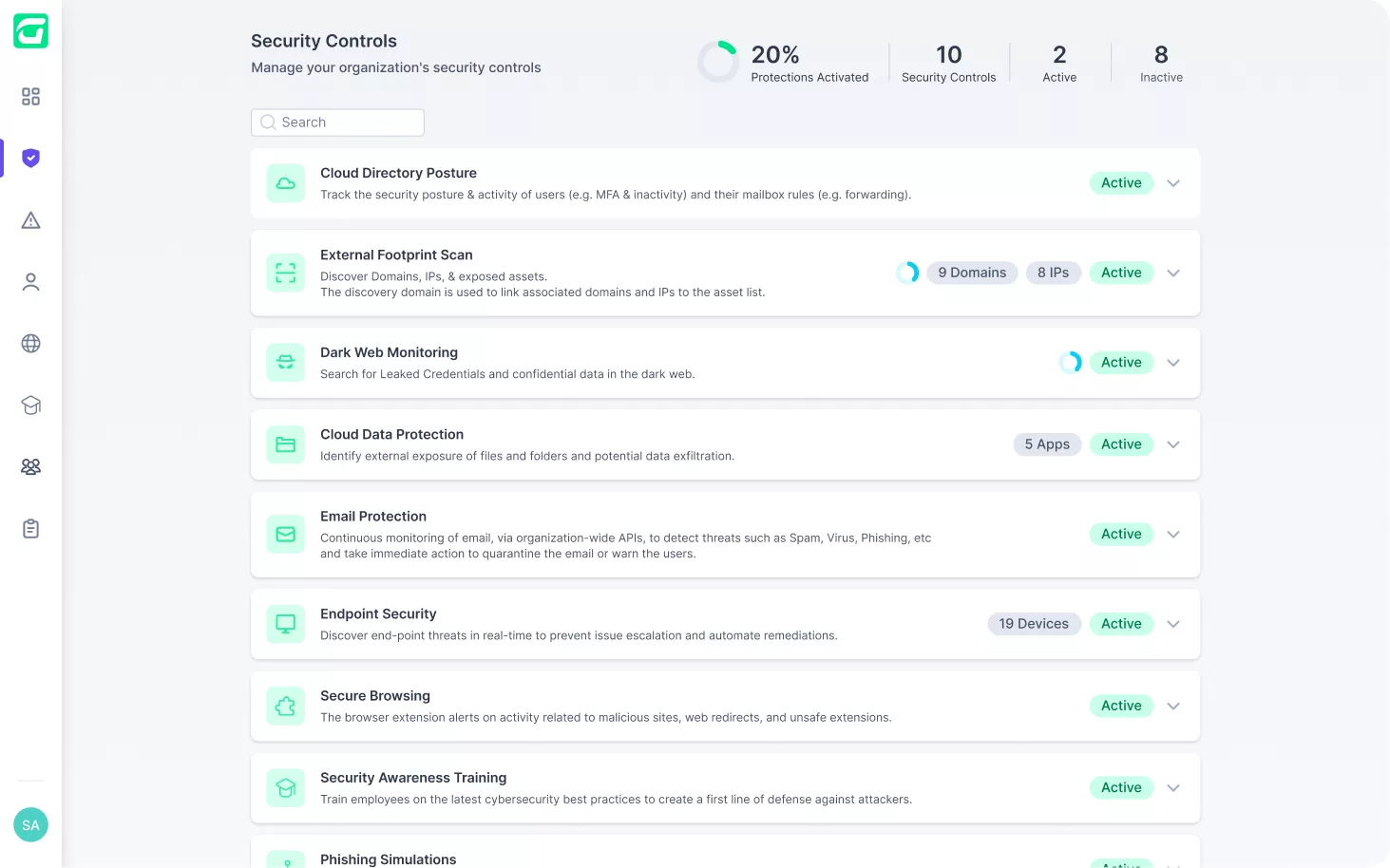
Identity Threat Detection and Response, backed by an elite research and threat hunting team, proactively verifies security settings, while actively benchmarking and analyzing user behavior to flag suspicious activity.

Stop malware, ransomware, and advanced threats at the source. AI-native EDR (with SentinelOne embedded) and Managed AV (with Windows Defender) ensure real-time protection across devices.

Strengthen your cybersecurity with best-in-class email protection seamlessly integrated into the Guardz platform. Powered by Check Point, delivering real-time defense against phishing, ransomware, and more.

Lock down sensitive business data with seamless cloud protection, without the need for complex policies, ensuring secure file collaboration while preventing unauthorized access and data leaks.

Transform employees into a strong line of defense against cyber threats with pre-scheduled security awareness training that alters behavior and limits human-driven cyber risks before they escalate.

Identify security weaknesses before attackers do by using generative AI and branded templates to automate phishing simulations to measure employee resilience and reinforce cybersecurity awareness.

Scan the digital footprint of businesses to discover exposures and eliminate vulnerabilities across domains, IPs, and cloud assets; closing security gaps before they’re exploited.

Knowledge of the dark corners of the internet can be exposed by scraping, analyzing and continuously monitoring the dark web for malicious activity targeting businesses and user credentials.

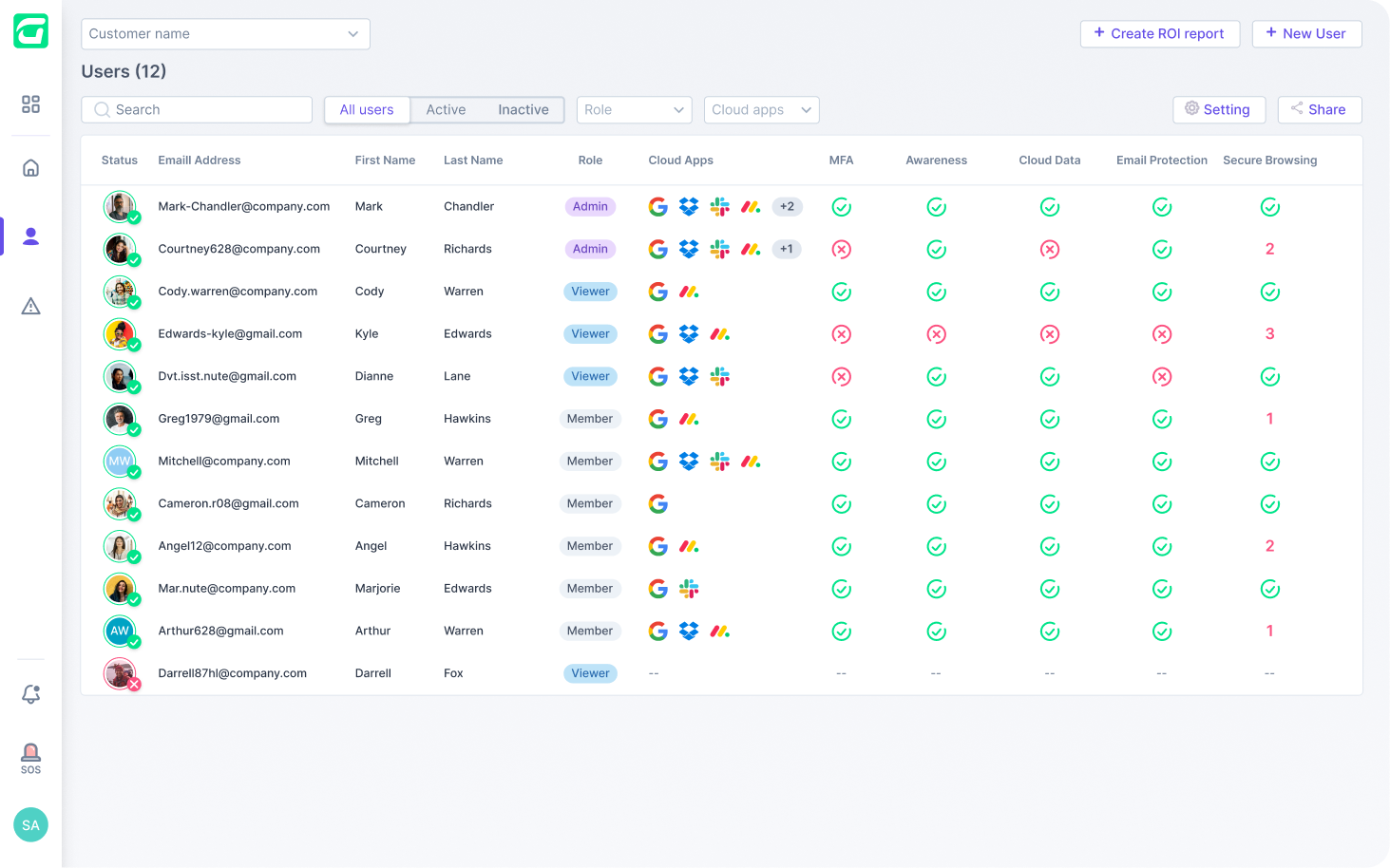
Identity Threat Detection & Response (ITDR) proactively verifies MFA and security settings, while actively benchmarking and analyzing user behavior to flag suspicious activity.
Stop malware, ransomware, and advanced threats at the source. AI-native EDR (with SentinelOne embedded) and Managed AV (with Windows Defender) ensure real-time protection across devices.
Block sophisticated phishing and email-based attacks before they reach users with an API-based and AI-native engine to prevent credential theft, ransomware, and impersonation threats in real time.
Lock down sensitive business data with seamless cloud protection, without the need for complex policies, ensuring secure file collaboration while preventing unauthorized access and data leaks.
Transform employees into a strong line of defense against cyber threats with pre-scheduled security awareness training that alters behavior and limits human-driven cyber risks before they escalate.
Identify security weaknesses before attackers do by using generative AI and branded templates to automate phishing simulations to measure employee resilience and reinforce cybersecurity awareness.
Web security through a browser extension that escalates risk around employees exposed to malicious sites, web redirects, unsafe extensions, and more during their day-to-day internet activity.
Scan the digital footprint of businesses to discover exposures and eliminate vulnerabilities across domains, IPs, and cloud assets; closing security gaps before they’re exploited.
Knowledge of the dark corners of the internet can be exposed by scraping, analyzing and continuously monitoring the dark web for malicious activity targeting businesses and user credentials.
Identity Threat Detection and Response, backed by an elite research and threat hunting team, proactively verifies security settings, while actively benchmarking and analyzing user behavior to flag suspicious activity.
Stop malware, ransomware, and advanced threats at the source. AI-native EDR (with SentinelOne embedded) and Managed AV (with Windows Defender) ensure real-time protection across devices.
Strengthen your cybersecurity with best-in-class email protection seamlessly integrated into the Guardz platform. Powered by Check Point, delivering real-time defense against phishing, ransomware, and more.
Lock down sensitive business data with seamless cloud protection, without the need for complex policies, ensuring secure file collaboration while preventing unauthorized access and data leaks.
Transform employees into a strong line of defense against cyber threats with pre-scheduled security awareness training that alters behavior and limits human-driven cyber risks before they escalate.
Identify security weaknesses before attackers do by using generative AI and branded templates to automate phishing simulations to measure employee resilience and reinforce cybersecurity awareness.
Scan the digital footprint of businesses to discover exposures and eliminate vulnerabilities across domains, IPs, and cloud assets; closing security gaps before they’re exploited.
Knowledge of the dark corners of the internet can be exposed by scraping, analyzing and continuously monitoring the dark web for malicious activity targeting businesses and user credentials.









Providing security that MSPs trust, packaged with the operational ease and client-focused tools needed to drive growth and show value.

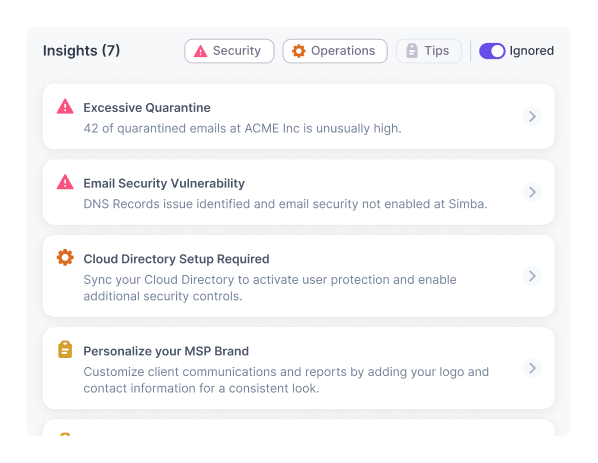
Detect threats faster by connecting the dots across security controls in a unified platform. Guardz normalizes detections into a single view, to cut through the noise, and take preventative action.
Guardz ties every detection to real users, making responses fast & precise. Armed with behavioral intelligence and identity threat analytics, MSPs can pinpoint attacks, stop breaches, and educate users.
Gain 24/7 protection with Guardz MDR on top of the security controls. Detect and respond to endpoint and identity threats in real time, with machine-speed precision and expert support
Evidence mapping streamlines compliance preparation by reporting how Guardz security controls align with frameworks like SOC 2, ISO 27001, HIPAA, and GDPR, making the audit process faster and easier.



Centrally navigate security of multiple clients, either aggregated or with their unique individual environments; ensuring efficiency, visibility, and consistency when protecting their users and assets.
Security is only as good as the ability to manage it, so global configurations, customizations and automations are used to programmatically identify threats and remediate them before they can spread.
With one-click remediations, machine learning systems, AI workflows and powerful integrations, even non-security experts can swiftly respond to cyber events and ensure optimal security outcomes.
The use of LLMs makes it simple to summarize large volumes of detections, gain insights into risky assets, explain detection reasons to end users, and even spin up custom phishing simulations on the fly.

Use Prospecting Reports to instantly scan a clients public-facing assets to uncover security gaps, drive conversation with real insights, prove your expertise, and win business with data that hits home.
Leverage tools and resources to enhance client engagement and drive overall business growth in one centralized hub that includes marketing assets, tailored reports, branding customization and more.
Demonstrate your impact by giving clients a data-backed look at their security posture. Delivered monthly, quarterly, or on-demand, the report highlights threats, risk, and mitigation activity.
Give clients visibility and control with configurable admin roles. They can manage detections, response and policies, while you retain oversight; building trust, boosting hygiene, and proving your value.


Guardz is the top choice for MSPs, offering a unified platform powered by AI to streamline cybersecurity and drive growth.







Link your Google Workspace or Microsoft 365 business account, deploy endpoint agents, and configure the system for real time threat analysis.
Continuous monitoring of digital assets promptly alerts on critical issues, escalates incidents to the MDR team, all the while guiding resolution through automated remediations, playbooks and reporting.
Get started by linking your Google Workspace or Microsoft 365 business account, grant the necessary permissions for real time threat analysis, and enable remediation plans.
Get started by linking your Google Workspace or Microsoft 365 business account, grant the necessary permissions for real time threat analysis, and enable remediation plans.
Continuous monitoring of digital assets promptly alerts on critical issues, escalates incidents to the MDR team, all the while guiding resolution through automated remediations, playbooks and reporting.
Guardz continuously monitors internal and external digital assets and promptly alerts on critical issues while guiding resolution through automated and manual remediations
Guardz continuously monitors internal and external digital assets and promptly alerts on critical issues while guiding resolution through automated and manual remediations
Guardz continuously monitors internal and external digital assets and promptly alerts on critical issues while guiding resolution through automated and manual remediations

Guardz integrations and apps help you work seamlessly, enhance security, and boost efficiency.












More MSPs are turning to Guardz to streamline security and outpace cyber threats.







Before you go, grab our free guide highlighting underutilized security settings and best practices every MSP should know about identity posture.
Download the Guide
Before you go, grab our free guide highlighting underutilized security settings and best practices every MSP should know about identity posture.
Download the Guide
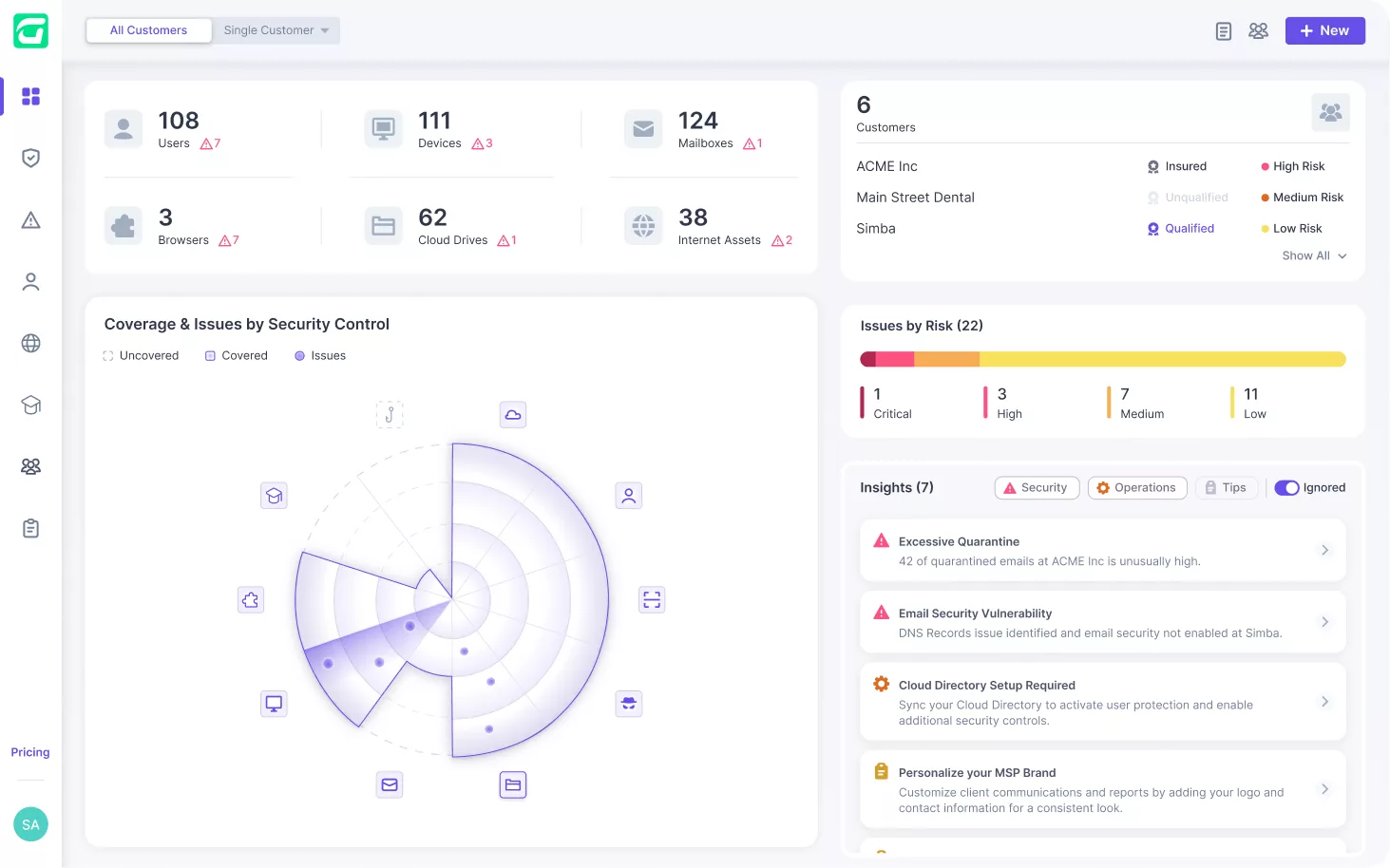
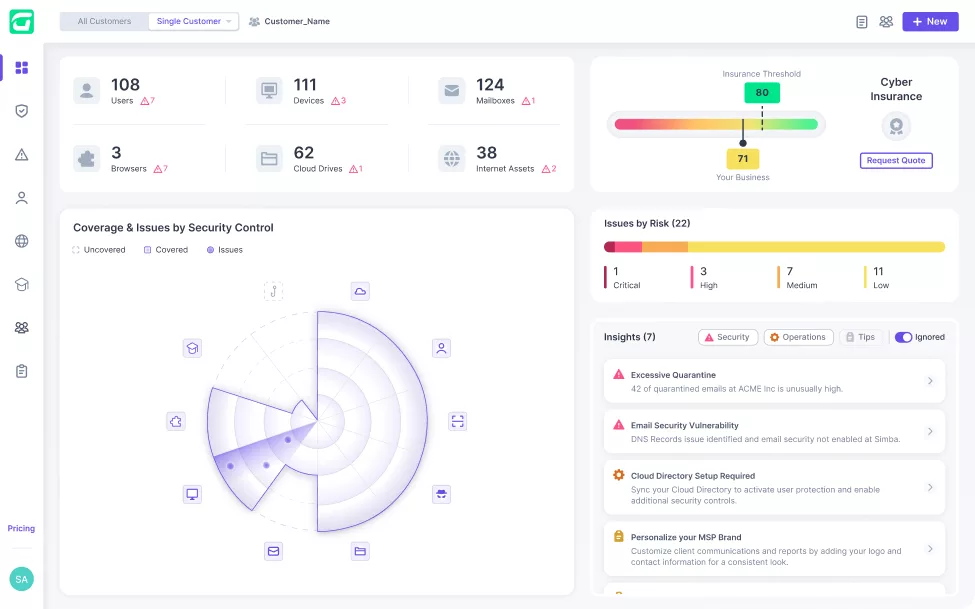

Guardz automatically discovers and monitors all your customers’ digital assets. Drill down to see more details and discover related issues.
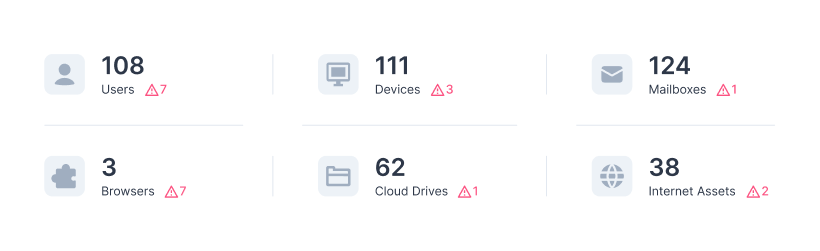
Guardz provides the security controls and coverage across your customers and detects issues in real-time.

Get all the security controls needed to fortify your client’s cyber posture.
Real-time protection of all business employees across all applications, devices, and communication channels.
Connect the dots across detections and swiftly remediate, regardless of the attack vector.
Real-time cybersecurity posture score that reflects the cyber risk and remediation progress.
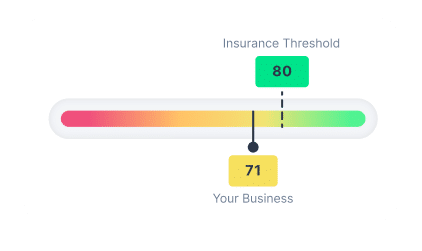
Get the coverage you need at the right price based on your client’s posture.
Connect with one of our experts in your preferred way