Prevent the most dangerous email-based attacks through continuous monitoring, contextual analysis, and automated response.

Trusted by Leading Partners












































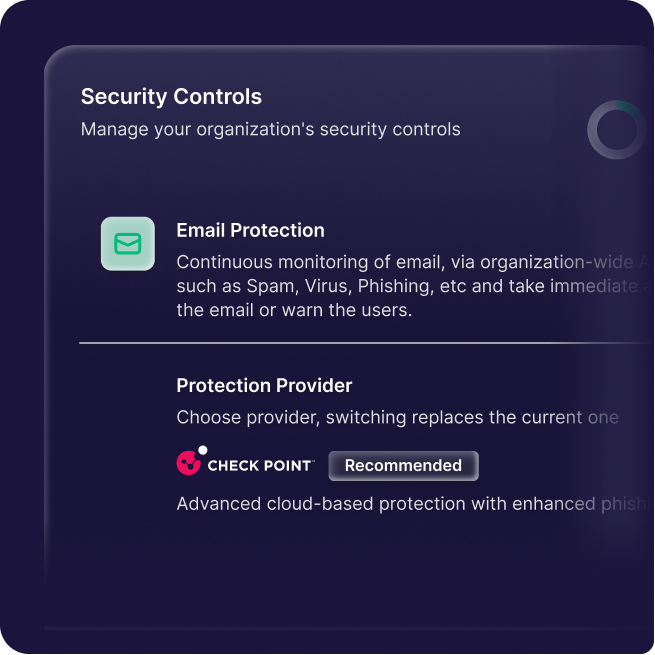
While Check Point Harmony (formerly Avanan) delivers best-in-class email security, Guardz connects the dots, transforming fragmented signals into coordinated protection that contains incidents and closes gaps fast.
With API-based integration for instant setup, MSPs get powerful phishing and BEC protection that works seamlessly across their entire security stack for complete, connected defense.


Fake login pages or forms used to steal usernames and passwords, often bypassing filters using trusted-looking domains and lures.

Forged sender identities used to mimic executives, vendors, or brands, tricking users into clicking, replying, or sending data.

Compromised or impersonated accounts used to manipulate users into transferring funds or sharing sensitive business information.

Malicious attachments or links deliver malware or ransomware, exploiting user trust to gain system access or encrypt files.

Targeted attacks tailored to specific users or roles, using personal or organizational context to increase credibility and impact.

Emails with malicious or hidden links that evade detection and lead users to phishing sites or malware-hosting infrastructure.
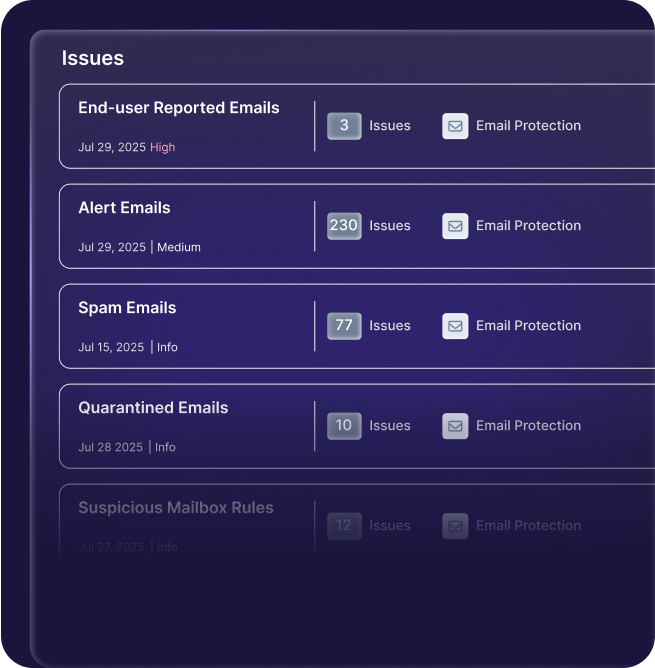
Guardz detects and responds to modern email threats in real time by quarantining, alerting, educating, and correlating risk.
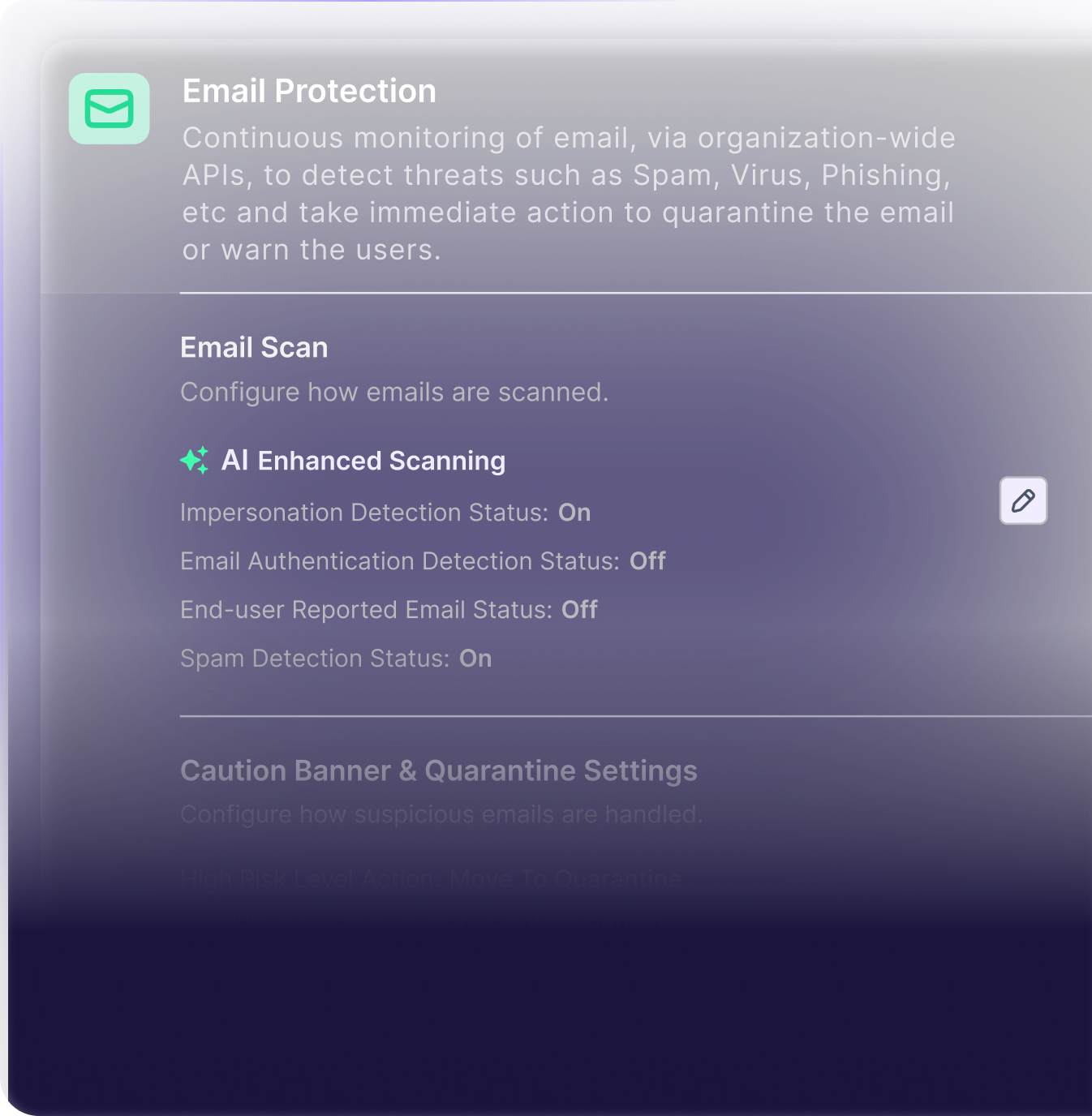
Email & phishing analysis using fine-tuned LLM models across a large volume of metadata and authentication signals.
Detects alias mismatches and impersonation via user patterns and historical sender behavior to flag anomalies and suspicious mail.
Admin assigned responses (quarantine, banners, spam) per risk level, managed globally and tailored per organization.
Seamless deployment via Microsoft and Google APIs, without agents or MX record changes, for instant mailbox scanning on delivery.
End user reporting of email for investigation, cross remediation, and continuous tuning of models, to adapt with evolving threats.
Deep inspection of embedded links and attachments using AI and threat intelligence, including file scans to detect hidden malware.
Guardz detects and responds to modern email threats in real time by quarantining, alerting, educating, and correlating risk.
Email & phishing analysis using fine-tuned LLM models across a large volume of metadata and authentication signals.
Detects alias mismatches and impersonation
via user patterns and historical sender behavior to flag anomalies and suspicious mail.
Admin assigned responses (quarantine, banners, spam) per risk level, managed globally and tailored per organization.
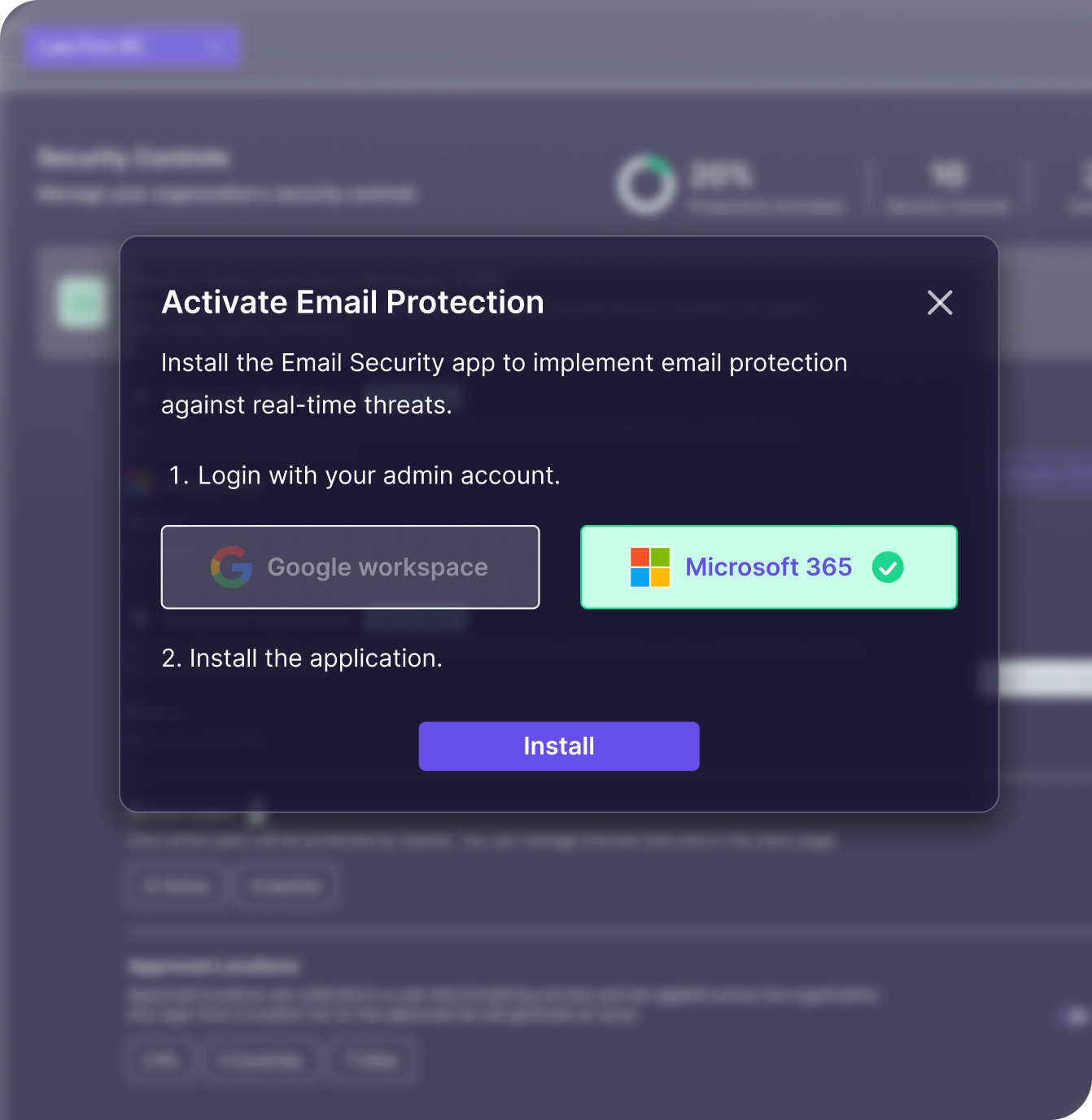
Seamless deployment via Microsoft and Google APIs, without agents or MX record changes, for instant mailbox scanning on delivery.
End user reporting of email for investigation, cross remediation, and continuous tuning of models, to adapt with evolving threats.
Deep inspection of embedded links and attachments using AI and threat intelligence, including file scans to detect hidden malware.
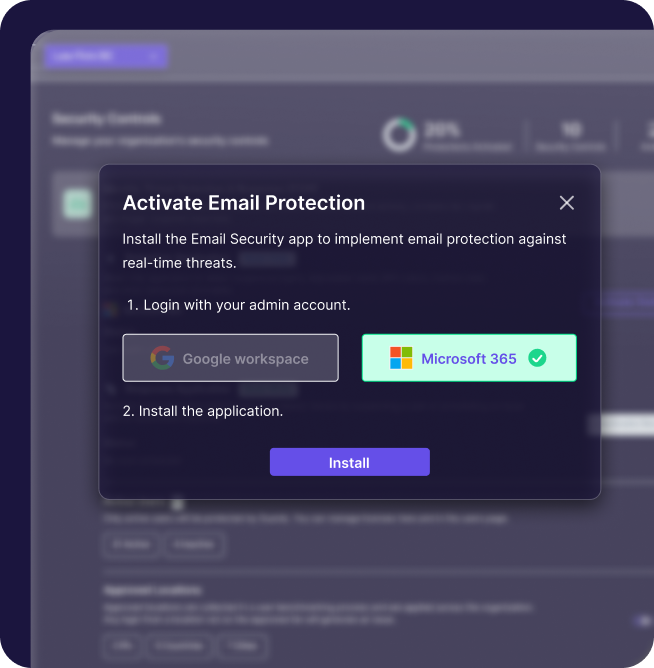
Connect via Microsoft 365 or Google Workspace APIs.
Scan emails instantly and alert users and admins to threats.

User reports train the system and trigger threat removal.



Email security is the process of protecting email accounts, content, and communications from threats such as phishing, malware, spoofing, and unauthorized access. For MSPs, it means providing customers with layered protection, real-time threat detection, and quick remediation to prevent business disruption.
Because it’s the easiest way for attackers to trick users into clicking a link, opening a malicious file, or revealing sensitive information. SMBs are often targeted because they lack dedicated security teams, making MSP-provided email protection critical.
Unfamiliar sent items, password reset notifications you didn’t request, unusual login activity, or complaints from contacts about suspicious emails from you are strong indicators.
Guardz is a unified cybersecurity platform, not a point solution. It connects email threat data with other critical signals, enabling MSPs to stop attacks across multiple vectors without juggling separate tools or losing visibility.
If an attack starts in email but also triggers suspicious identity logins, endpoint alerts, or unusual cloud activity, Guardz automatically links these events so MSPs can take coordinated action across all affected systems.
Reusing passwords, disabling multi-factor authentication, ignoring warning banners or alerts, and failing to report suspicious emails are top risks. Many SMBs also skip regular phishing simulations and cyber awareness training, leaving employees unprepared for real-world attacks

Guardz is the top choice for MSPs, offering a unified platform powered by AI to streamline cybersecurity and drive growth.







Navigate the Guardz platform and experience how it protects your MSP clients in real time.
Connect with one of our experts in your preferred way