Security News
curl Shuts Down Bug Bounty Program After Flood of AI Slop Reports
A surge of AI-generated vulnerability reports has pushed open source maintainers to rethink bug bounties and tighten security disclosure processes.
Quickly evaluate the security and health of any open source package.
meutils
2025.3.7.22.47.3
Live on PyPI
Blocked by Socket
The code sends sensitive credentials from environment variables over an unencrypted HTTP connection to an external API service at api[.]sqhyw[.]net:90. It authenticates using username/password from the YEZI_USER environment variable, retrieves access tokens, and automates the process of obtaining mobile phone numbers and SMS verification codes. This behavior poses significant supply chain security risks through: (1) leakage of environment variable credentials over unencrypted HTTP, (2) interaction with a suspicious external domain on a non-standard port, (3) logging of potentially sensitive API responses including tokens and SMS codes, and (4) facilitation of SMS verification bypass which could enable fraudulent account creation or spam activities. The code continuously polls the external API for up to 120 seconds to retrieve SMS codes, creating additional operational risks. While not containing traditional malware payloads, the credential exfiltration and suspicious external communication patterns justify classification as malware due to the significant security risks posed to systems that deploy this code.
spherica
0.3.8
Live on PyPI
Blocked by Socket
This packaging/publish script contains multiple high-risk patterns: eval() on file contents (arbitrary code execution), hard-coded absolute token file path, passing secrets on the command line, and executing an assembled shell command via os.system. These make it unsuitable for use in untrusted or automated environments without remediation. Practical recommendations: replace eval() with safe parsing (json, toml, or ast.literal_eval), stop passing tokens on the command line (use environment variables or keyrings), use subprocess.run with argument lists (no shell) or twine APIs, remove absolute credential paths, audit and review nestpython.nsp.files.nbuild, and avoid destructive flags (erase_dir=True) unless explicitly intended. While the code does not show explicit obfuscated malware payloads, the insecure patterns provide straightforward vectors for supply-chain compromise if supporting files are modified.
n2225692000351
1.0.73
Removed from npm
Blocked by Socket
The code is heavily obfuscated, which raises suspicion about its intent. Without deobfuscation, it is impossible to determine if the code contains malware or poses a security risk. The obfuscation itself is a significant anomaly and should be addressed before using this code in any capacity.
Live on npm for 16 days, 5 hours and 48 minutes before removal. Socket users were protected even while the package was live.
test-hach
71.32.2
by hach-bug-bounty
Removed from npm
Blocked by Socket
The script appears to perform a DNS lookup using the 'host' command, with the hostname and username encoded in base64. This behavior could potentially be used for malicious purposes, such as exfiltrating data or establishing command and control communication.
Live on npm for 28 days, 9 hours and 49 minutes before removal. Socket users were protected even while the package was live.
mtmai
0.3.987
Live on PyPI
Blocked by Socket
This fragment intends to install and start KasmVNC by running many shell commands that create certs, write VNC password files, adjust group membership, and launch a VNC server. The primary security issues are unsafe shell interpolation (command injection risk), programmatic persistence of a possibly predictable password, execution with sudo based on unvalidated env vars, starting a VNC server exposed on 0.0.0.0 with disabled/basic auth, and multiple unsafe filesystem operations performed via shell. There is no clear evidence of obfuscated or direct exfiltration malware, but the behavior can provide an unauthorized remote access vector (backdoor-like) if used maliciously. Do not run this code without fixing shell usage, validating inputs, using secure randomly generated passwords, enforcing proper file permissions, and not disabling authentication.
genflow-lib
0.1.8
Live on PyPI
Blocked by Socket
This module contains functionality that intentionally executes Python config files and uses yaml.unsafe_load, and it patches the import mechanism to support relative importing of such config files. Those behaviors are high-risk for code execution if the config files or override strings are untrusted, but there is no evidence in this fragment of an intentional malicious backdoor, exfiltration, or obfuscation. The biggest security concern is the use of exec/unsafe_load/eval which are legitimate for this tool but should be considered dangerous in supply-chain or untrusted-file scenarios.
browsercmdhbt2
0.91
Live on PyPI
Blocked by Socket
This module automates account login via Selenium and handles session cookies and orchestration hooks. The presence of a hardcoded external HTTP address (http://178.128.211.227) passed to utils.save_cookie combined with deletion of local cookie artifacts and orchestration calls is highly suspicious for credential/session harvesting and exfiltration. Treat the code as high risk: do not run with real credentials until utils.* implementations are audited and the remote host is validated. If using this package in a benign automation environment, replace or inspect utils.save_cookie and remove any hardcoded remote endpoints and destructive cleanup commands.
ajaxdb-core
1.1.2
by ajax-16
Removed from npm
Blocked by Socket
This code fragment implements file-based DB operations but contains a critical filesystem path handling bug in dropDb: using path.join with a leading '/' in the second argument allows creation of an absolute path which can lead to deletion of arbitrary files the process can write. There is no validation of dbName anywhere, increasing risk of path traversal, unintended file creation/deletion, or directory pollution. There is no indication of network exfiltration, obfuscation, or explicit backdoor functionality; the primary security risk is unsafe filesystem handling that can lead to data loss or privilege escalation within the filesystem scope.
Live on npm for 1 hour and 33 minutes before removal. Socket users were protected even while the package was live.
meshcentral
0.7.18
by ysainthilaire
Live on npm
Blocked by Socket
This code implements a remote administration/tunneling agent with full remote shell and file system control. Functionality includes spawning shells, reading and writing arbitrary files, renaming/moving/deleting files (including recursive deletes), and opening network tunnels/upgrades to a controller URL. While this may be legitimate MeshAgent agent code, the features constitute high-risk capabilities if included as an unexpected dependency or executed without proper trust and authorization. Treat this module as potentially dangerous in a supply-chain context: it can be used for remote command execution and data access/exfiltration by whoever controls the MeshAgent controller.
org.jam4s:jam4s-codec-cli_3
0.0.3
Live on Maven Central
Blocked by Socket
This file exhibits multiple suspicious characteristics including a randomly generated class name and a future timestamp. It extends a core Scala compiler component which suggests a potential supply chain attack targeting the Scala compilation process. Without full decompilation of the methods, the exact malicious behavior cannot be determined, but tampering with compiler components is a high-risk attack vector that could allow injecting malicious code into all software built with the compromised compiler. Immediate isolation and thorough investigation is recommended.
journey-diadem-gqq095
1.0.0
by afifaljafari112
Removed from npm
Blocked by Socket
The code imports and calls functions from several external modules with unusual and non-descriptive names, without any apparent input or output. The naming conventions of the modules and functions are suspicious, and the purpose of the code is unclear. While the code does not directly indicate malicious behavior, the potential for it exists due to the lack of transparency and context for these external dependencies.
Live on npm for 57 days, 9 hours and 17 minutes before removal. Socket users were protected even while the package was live.
@image-process-library/blob-to-base64
5.789.0
by hshne
Live on npm
Blocked by Socket
The code collects environment variables and sends them to a potentially malicious remote server under certain conditions. This behavior is highly suspicious and could lead to data leakage or credential theft.
ailever
0.2.817
Live on PyPI
Blocked by Socket
The fragment contains a high-risk pattern: it downloads a Python script from a remote source and immediately executes it without integrity verification or sandboxing. This creates a critical supply-chain and remote-code-execution risk, as the remote payload could perform any action on the host, including data exfiltration, credential access, or system compromise. Even though defaults use placeholders, the mechanism itself is unsafe and should be disallowed or hardened (e.g., verify hashes, use signed modules, avoid executing remote code).
pinokiod
3.194.0
by cocktailpeanut
Live on npm
Blocked by Socket
The SweetAlert2 library code is mostly benign and serves as a UI modal dialog tool. However, it contains a suspicious and potentially malicious snippet that targets Russian users on certain domains to play an unsolicited audio prank, disabling pointer events and potentially disrupting user interaction. This behavior is unexpected and should be considered a moderate security risk and potential malware. The rest of the code shows no signs of malicious intent. The provided reports were invalid and unhelpful. Users should be cautious about this version of the library due to the embedded prank behavior.
pagination-controls
7.99.99
by takeiteasy567
Removed from npm
Blocked by Socket
The code uses the exec function to run shell commands, which poses a significant security risk. It could potentially execute malicious code if the input to exec is manipulated. Redirecting output to /dev/null to hide execution details is suspicious.
Live on npm for 1 hour and 4 minutes before removal. Socket users were protected even while the package was live.
github.com/milvus-io/milvus
v0.10.3-0.20220105130520-64a5db66e9ef
Live on Go Modules
Blocked by Socket
This code implements an insecure, unauthenticated RPC mechanism that allows remote clients to cause arbitrary code execution and exfiltrate files/system information. Using pickle over an untrusted network and invoking methods by client-supplied names are severe supply-chain/backdoor risks. Do not deploy or reuse this code in production; it should be treated as a backdoor/untrusted remote-execution component unless wrapped with strong authentication, authorization, sandboxing, and safe serialization.
bit-pipe-publish
0.0.24
by liviu.maftuleac
Live on npm
Blocked by Socket
The code fragment demonstrates a workflow that reads deployment-related inputs and mutates Kubernetes manifests to change container images and related fields, followed by persisting updates to disk. While this could be legitimate automation (CI/CD tooling or cluster-hardening utilities), the heavy obfuscation, sizeable data-driven mutation logic, and direct writes to critical deployment files constitute a significant supply-chain and runtime-risk. Treat as suspicious; require source-of-truth validation for all input data, remove obfuscation, and run in a sandbox with strict runtime controls and auditing to confirm intended behavior and prevent unauthorized deployments.
ailever
0.2.349
Live on PyPI
Blocked by Socket
The code exhibits a dangerous remote code execution pattern: it downloads and immediately runs a remote Python payload without integrity checks, sandboxing, or input validation. This creates a severe supply-chain and runtime security risk. Recommended mitigations include removing dynamic downloads, validating payloads with cryptographic hashes or signatures, using safe subprocess invocations with argument lists, and implementing strict input sanitization. If remote functionality must remain, switch to a trusted-internal mechanism (e.g., plugin architecture with signed components, offline verification) and add robust error handling and logging.
github.com/bishopfox/sliver
v1.5.40-0.20231110210156-f944d24dc3f0
Live on Go Modules
Blocked by Socket
This file implements an encrypted DNS command-and-control client (Sliver implant DNS transport). It intentionally serializes, encrypts and transports arbitrary protobuf envelopes over DNS queries and reads responses — behavior consistent with a backdoor/C2 implant. There are no hardcoded credentials or obfuscation techniques in this module; however, the module enables covert data exfiltration and remote command delivery when provided a parent domain and resolvers. From a supply-chain/security standpoint, including this package in software will provide C2 capabilities and is high risk unless explicitly desired for red-team/offensive use.
meutils
2025.3.7.22.47.3
Live on PyPI
Blocked by Socket
The code sends sensitive credentials from environment variables over an unencrypted HTTP connection to an external API service at api[.]sqhyw[.]net:90. It authenticates using username/password from the YEZI_USER environment variable, retrieves access tokens, and automates the process of obtaining mobile phone numbers and SMS verification codes. This behavior poses significant supply chain security risks through: (1) leakage of environment variable credentials over unencrypted HTTP, (2) interaction with a suspicious external domain on a non-standard port, (3) logging of potentially sensitive API responses including tokens and SMS codes, and (4) facilitation of SMS verification bypass which could enable fraudulent account creation or spam activities. The code continuously polls the external API for up to 120 seconds to retrieve SMS codes, creating additional operational risks. While not containing traditional malware payloads, the credential exfiltration and suspicious external communication patterns justify classification as malware due to the significant security risks posed to systems that deploy this code.
spherica
0.3.8
Live on PyPI
Blocked by Socket
This packaging/publish script contains multiple high-risk patterns: eval() on file contents (arbitrary code execution), hard-coded absolute token file path, passing secrets on the command line, and executing an assembled shell command via os.system. These make it unsuitable for use in untrusted or automated environments without remediation. Practical recommendations: replace eval() with safe parsing (json, toml, or ast.literal_eval), stop passing tokens on the command line (use environment variables or keyrings), use subprocess.run with argument lists (no shell) or twine APIs, remove absolute credential paths, audit and review nestpython.nsp.files.nbuild, and avoid destructive flags (erase_dir=True) unless explicitly intended. While the code does not show explicit obfuscated malware payloads, the insecure patterns provide straightforward vectors for supply-chain compromise if supporting files are modified.
n2225692000351
1.0.73
Removed from npm
Blocked by Socket
The code is heavily obfuscated, which raises suspicion about its intent. Without deobfuscation, it is impossible to determine if the code contains malware or poses a security risk. The obfuscation itself is a significant anomaly and should be addressed before using this code in any capacity.
Live on npm for 16 days, 5 hours and 48 minutes before removal. Socket users were protected even while the package was live.
test-hach
71.32.2
by hach-bug-bounty
Removed from npm
Blocked by Socket
The script appears to perform a DNS lookup using the 'host' command, with the hostname and username encoded in base64. This behavior could potentially be used for malicious purposes, such as exfiltrating data or establishing command and control communication.
Live on npm for 28 days, 9 hours and 49 minutes before removal. Socket users were protected even while the package was live.
mtmai
0.3.987
Live on PyPI
Blocked by Socket
This fragment intends to install and start KasmVNC by running many shell commands that create certs, write VNC password files, adjust group membership, and launch a VNC server. The primary security issues are unsafe shell interpolation (command injection risk), programmatic persistence of a possibly predictable password, execution with sudo based on unvalidated env vars, starting a VNC server exposed on 0.0.0.0 with disabled/basic auth, and multiple unsafe filesystem operations performed via shell. There is no clear evidence of obfuscated or direct exfiltration malware, but the behavior can provide an unauthorized remote access vector (backdoor-like) if used maliciously. Do not run this code without fixing shell usage, validating inputs, using secure randomly generated passwords, enforcing proper file permissions, and not disabling authentication.
genflow-lib
0.1.8
Live on PyPI
Blocked by Socket
This module contains functionality that intentionally executes Python config files and uses yaml.unsafe_load, and it patches the import mechanism to support relative importing of such config files. Those behaviors are high-risk for code execution if the config files or override strings are untrusted, but there is no evidence in this fragment of an intentional malicious backdoor, exfiltration, or obfuscation. The biggest security concern is the use of exec/unsafe_load/eval which are legitimate for this tool but should be considered dangerous in supply-chain or untrusted-file scenarios.
browsercmdhbt2
0.91
Live on PyPI
Blocked by Socket
This module automates account login via Selenium and handles session cookies and orchestration hooks. The presence of a hardcoded external HTTP address (http://178.128.211.227) passed to utils.save_cookie combined with deletion of local cookie artifacts and orchestration calls is highly suspicious for credential/session harvesting and exfiltration. Treat the code as high risk: do not run with real credentials until utils.* implementations are audited and the remote host is validated. If using this package in a benign automation environment, replace or inspect utils.save_cookie and remove any hardcoded remote endpoints and destructive cleanup commands.
ajaxdb-core
1.1.2
by ajax-16
Removed from npm
Blocked by Socket
This code fragment implements file-based DB operations but contains a critical filesystem path handling bug in dropDb: using path.join with a leading '/' in the second argument allows creation of an absolute path which can lead to deletion of arbitrary files the process can write. There is no validation of dbName anywhere, increasing risk of path traversal, unintended file creation/deletion, or directory pollution. There is no indication of network exfiltration, obfuscation, or explicit backdoor functionality; the primary security risk is unsafe filesystem handling that can lead to data loss or privilege escalation within the filesystem scope.
Live on npm for 1 hour and 33 minutes before removal. Socket users were protected even while the package was live.
meshcentral
0.7.18
by ysainthilaire
Live on npm
Blocked by Socket
This code implements a remote administration/tunneling agent with full remote shell and file system control. Functionality includes spawning shells, reading and writing arbitrary files, renaming/moving/deleting files (including recursive deletes), and opening network tunnels/upgrades to a controller URL. While this may be legitimate MeshAgent agent code, the features constitute high-risk capabilities if included as an unexpected dependency or executed without proper trust and authorization. Treat this module as potentially dangerous in a supply-chain context: it can be used for remote command execution and data access/exfiltration by whoever controls the MeshAgent controller.
org.jam4s:jam4s-codec-cli_3
0.0.3
Live on Maven Central
Blocked by Socket
This file exhibits multiple suspicious characteristics including a randomly generated class name and a future timestamp. It extends a core Scala compiler component which suggests a potential supply chain attack targeting the Scala compilation process. Without full decompilation of the methods, the exact malicious behavior cannot be determined, but tampering with compiler components is a high-risk attack vector that could allow injecting malicious code into all software built with the compromised compiler. Immediate isolation and thorough investigation is recommended.
journey-diadem-gqq095
1.0.0
by afifaljafari112
Removed from npm
Blocked by Socket
The code imports and calls functions from several external modules with unusual and non-descriptive names, without any apparent input or output. The naming conventions of the modules and functions are suspicious, and the purpose of the code is unclear. While the code does not directly indicate malicious behavior, the potential for it exists due to the lack of transparency and context for these external dependencies.
Live on npm for 57 days, 9 hours and 17 minutes before removal. Socket users were protected even while the package was live.
@image-process-library/blob-to-base64
5.789.0
by hshne
Live on npm
Blocked by Socket
The code collects environment variables and sends them to a potentially malicious remote server under certain conditions. This behavior is highly suspicious and could lead to data leakage or credential theft.
ailever
0.2.817
Live on PyPI
Blocked by Socket
The fragment contains a high-risk pattern: it downloads a Python script from a remote source and immediately executes it without integrity verification or sandboxing. This creates a critical supply-chain and remote-code-execution risk, as the remote payload could perform any action on the host, including data exfiltration, credential access, or system compromise. Even though defaults use placeholders, the mechanism itself is unsafe and should be disallowed or hardened (e.g., verify hashes, use signed modules, avoid executing remote code).
pinokiod
3.194.0
by cocktailpeanut
Live on npm
Blocked by Socket
The SweetAlert2 library code is mostly benign and serves as a UI modal dialog tool. However, it contains a suspicious and potentially malicious snippet that targets Russian users on certain domains to play an unsolicited audio prank, disabling pointer events and potentially disrupting user interaction. This behavior is unexpected and should be considered a moderate security risk and potential malware. The rest of the code shows no signs of malicious intent. The provided reports were invalid and unhelpful. Users should be cautious about this version of the library due to the embedded prank behavior.
pagination-controls
7.99.99
by takeiteasy567
Removed from npm
Blocked by Socket
The code uses the exec function to run shell commands, which poses a significant security risk. It could potentially execute malicious code if the input to exec is manipulated. Redirecting output to /dev/null to hide execution details is suspicious.
Live on npm for 1 hour and 4 minutes before removal. Socket users were protected even while the package was live.
github.com/milvus-io/milvus
v0.10.3-0.20220105130520-64a5db66e9ef
Live on Go Modules
Blocked by Socket
This code implements an insecure, unauthenticated RPC mechanism that allows remote clients to cause arbitrary code execution and exfiltrate files/system information. Using pickle over an untrusted network and invoking methods by client-supplied names are severe supply-chain/backdoor risks. Do not deploy or reuse this code in production; it should be treated as a backdoor/untrusted remote-execution component unless wrapped with strong authentication, authorization, sandboxing, and safe serialization.
bit-pipe-publish
0.0.24
by liviu.maftuleac
Live on npm
Blocked by Socket
The code fragment demonstrates a workflow that reads deployment-related inputs and mutates Kubernetes manifests to change container images and related fields, followed by persisting updates to disk. While this could be legitimate automation (CI/CD tooling or cluster-hardening utilities), the heavy obfuscation, sizeable data-driven mutation logic, and direct writes to critical deployment files constitute a significant supply-chain and runtime-risk. Treat as suspicious; require source-of-truth validation for all input data, remove obfuscation, and run in a sandbox with strict runtime controls and auditing to confirm intended behavior and prevent unauthorized deployments.
ailever
0.2.349
Live on PyPI
Blocked by Socket
The code exhibits a dangerous remote code execution pattern: it downloads and immediately runs a remote Python payload without integrity checks, sandboxing, or input validation. This creates a severe supply-chain and runtime security risk. Recommended mitigations include removing dynamic downloads, validating payloads with cryptographic hashes or signatures, using safe subprocess invocations with argument lists, and implementing strict input sanitization. If remote functionality must remain, switch to a trusted-internal mechanism (e.g., plugin architecture with signed components, offline verification) and add robust error handling and logging.
github.com/bishopfox/sliver
v1.5.40-0.20231110210156-f944d24dc3f0
Live on Go Modules
Blocked by Socket
This file implements an encrypted DNS command-and-control client (Sliver implant DNS transport). It intentionally serializes, encrypts and transports arbitrary protobuf envelopes over DNS queries and reads responses — behavior consistent with a backdoor/C2 implant. There are no hardcoded credentials or obfuscation techniques in this module; however, the module enables covert data exfiltration and remote command delivery when provided a parent domain and resolvers. From a supply-chain/security standpoint, including this package in software will provide C2 capabilities and is high risk unless explicitly desired for red-team/offensive use.
Socket detects traditional vulnerabilities (CVEs) but goes beyond that to scan the actual code of dependencies for malicious behavior. It proactively detects and blocks 70+ signals of supply chain risk in open source code, for comprehensive protection.
Possible typosquat attack
Known malware
Git dependency
GitHub dependency
AI-detected potential malware
HTTP dependency
Obfuscated code
Suspicious Stars on GitHub
Telemetry
Protestware or potentially unwanted behavior
Critical CVE
High CVE
Medium CVE
Low CVE
Unpopular package
Minified code
Bad dependency semver
Wildcard dependency
Socket optimized override available
Deprecated
Unmaintained
Explicitly Unlicensed Item
License Policy Violation
Misc. License Issues
No License Found
Non-permissive License
License exception
Unidentified License
Ambiguous License Classifier
Copyleft License
Socket detects and blocks malicious dependencies, often within just minutes of them being published to public registries, making it the most effective tool for blocking zero-day supply chain attacks.
Socket is built by a team of prolific open source maintainers whose software is downloaded over 1 billion times per month. We understand how to build tools that developers love. But don’t take our word for it.

Nat Friedman
CEO at GitHub

Suz Hinton
Senior Software Engineer at Stripe
heck yes this is awesome!!! Congrats team 🎉👏

Matteo Collina
Node.js maintainer, Fastify lead maintainer
So awesome to see @SocketSecurity launch with a fresh approach! Excited to have supported the team from the early days.

DC Posch
Director of Technology at AppFolio, CTO at Dynasty
This is going to be super important, especially for crypto projects where a compromised dependency results in stolen user assets.

Luis Naranjo
Software Engineer at Microsoft
If software supply chain attacks through npm don't scare the shit out of you, you're not paying close enough attention.
@SocketSecurity sounds like an awesome product. I'll be using socket.dev instead of npmjs.org to browse npm packages going forward

Elena Nadolinski
Founder and CEO at Iron Fish
Huge congrats to @SocketSecurity! 🙌
Literally the only product that proactively detects signs of JS compromised packages.

Joe Previte
Engineering Team Lead at Coder
Congrats to @feross and the @SocketSecurity team on their seed funding! 🚀 It's been a big help for us at @CoderHQ and we appreciate what y'all are doing!

Josh Goldberg
Staff Developer at Codecademy
This is such a great idea & looks fantastic, congrats & good luck @feross + team!
The best security teams in the world use Socket to get visibility into supply chain risk, and to build a security feedback loop into the development process.

Scott Roberts
CISO at UiPath
As a happy Socket customer, I've been impressed with how quickly they are adding value to the product, this move is a great step!

Yan Zhu
Head of Security at Brave, DEFCON, EFF, W3C
glad to hear some of the smartest people i know are working on (npm, etc.) supply chain security finally :). @SocketSecurity

Andrew Peterson
CEO and Co-Founder at Signal Sciences (acq. Fastly)
How do you track the validity of open source software libraries as they get updated? You're prob not. Check out @SocketSecurity and the updated tooling they launched.
Supply chain is a cluster in security as we all know and the tools from Socket are "duh" type tools to be implementing. Check them out and follow Feross Aboukhadijeh to see more updates coming from them in the future.

Zbyszek Tenerowicz
Senior Security Engineer at ConsenSys
socket.dev is getting more appealing by the hour

Devdatta Akhawe
Head of Security at Figma
The @SocketSecurity team is on fire! Amazing progress and I am exciting to see where they go next.

Sebastian Bensusan
Engineer Manager at Stripe
I find it surprising that we don't have _more_ supply chain attacks in software:
Imagine your airplane (the code running) was assembled (deployed) daily, with parts (dependencies) from internet strangers. How long until you get a bad part?
Excited for Socket to prevent this

Adam Baldwin
VP of Security at npm, Red Team at Auth0/Okta
Congrats to everyone at @SocketSecurity ❤️🤘🏻

Nico Waisman
CISO at Lyft
This is an area that I have personally been very focused on. As Nat Friedman said in the 2019 GitHub Universe keynote, Open Source won, and every time you add a new open source project you rely on someone else code and you rely on the people that build it.
This is both exciting and problematic. You are bringing real risk into your organization, and I'm excited to see progress in the industry from OpenSSF scorecards and package analyzers to the company that Feross Aboukhadijeh is building!
Depend on Socket to prevent malicious open source dependencies from infiltrating your app.
Install the Socket GitHub App in just 2 clicks and get protected today.
Block 70+ issues in open source code, including malware, typo-squatting, hidden code, misleading packages, permission creep, and more.
Reduce work by surfacing actionable security information directly in GitHub. Empower developers to make better decisions.
Attackers have taken notice of the opportunity to attack organizations through open source dependencies. Supply chain attacks rose a whopping 700% in the past year, with over 15,000 recorded attacks.
Nov 23, 2025
Shai Hulud v2
Shai Hulud v2 campaign: preinstall script (setup_bun.js) and loader (setup_bin.js) that installs/locates Bun and executes an obfuscated bundled malicious script (bun_environment.js) with suppressed output.
Nov 05, 2025
Elves on npm
A surge of auto-generated "elf-stats" npm packages is being published every two minutes from new accounts. These packages contain simple malware variants and are being rapidly removed by npm. At least 420 unique packages have been identified, often described as being generated every two minutes, with some mentioning a capture the flag challenge or test.
Jul 04, 2025
RubyGems Automation-Tool Infostealer
Since at least March 2023, a threat actor using multiple aliases uploaded 60 malicious gems to RubyGems that masquerade as automation tools (Instagram, TikTok, Twitter, Telegram, WordPress, and Naver). The gems display a Korean Glimmer-DSL-LibUI login window, then exfiltrate the entered username/password and the host's MAC address via HTTP POST to threat actor-controlled infrastructure.
Mar 13, 2025
North Korea's Contagious Interview Campaign
Since late 2024, we have tracked hundreds of malicious npm packages and supporting infrastructure tied to North Korea's Contagious Interview operation, with tens of thousands of downloads targeting developers and tech job seekers. The threat actors run a factory-style playbook: recruiter lures and fake coding tests, polished GitHub templates, and typosquatted or deceptive dependencies that install or import into real projects.
Jul 23, 2024
Network Reconnaissance Campaign
A malicious npm supply chain attack that leveraged 60 packages across three disposable npm accounts to fingerprint developer workstations and CI/CD servers during installation. Each package embedded a compact postinstall script that collected hostnames, internal and external IP addresses, DNS resolvers, usernames, home and working directories, and package metadata, then exfiltrated this data as a JSON blob to a hardcoded Discord webhook.
Get our latest security research, open source insights, and product updates.
Security News
A surge of AI-generated vulnerability reports has pushed open source maintainers to rethink bug bounties and tighten security disclosure processes.
Product
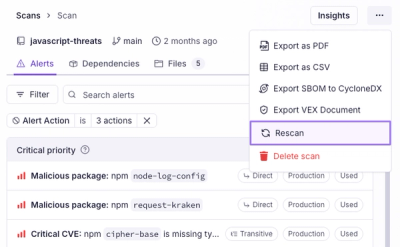
Scan results now load faster and remain consistent over time, with stable URLs and on-demand rescans for fresh security data.
Product
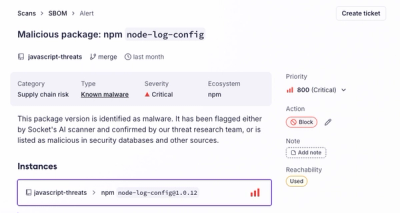
Socket's new Alert Details page is designed to surface more context, with a clearer layout, reachability dependency chains, and structured review.