You haven't signed in yet, you can have a better experience after signing in
 Themida Professional Software Protection and Encryption Tool System Software
Themida Professional Software Protection and Encryption Tool System Software
Activity Rules
1、Activity time:{{ info.groupon.start_at }} ~ {{ info.groupon.end_at }}。
1、Activity time:cease when sold out。
2、Validity period of the Group Buying:{{ info.groupon.expire_days * 24 }} hours。
3、Number of Group Buying:{{ info.groupon.need_count }}x。
Please Pay Attention
1、Teamwork process: Join/initiate a Group Buying and make a successful payment - Within the validity period, the number of team members meets the activity requirements - Group Buying succeeded!
2、If the number of participants cannot be met within the valid period, the group will fail, and the paid amount will be refunded in the original way.
3、The number of people required and the time of the event may vary among different products. Please pay attention to the rules of the event.
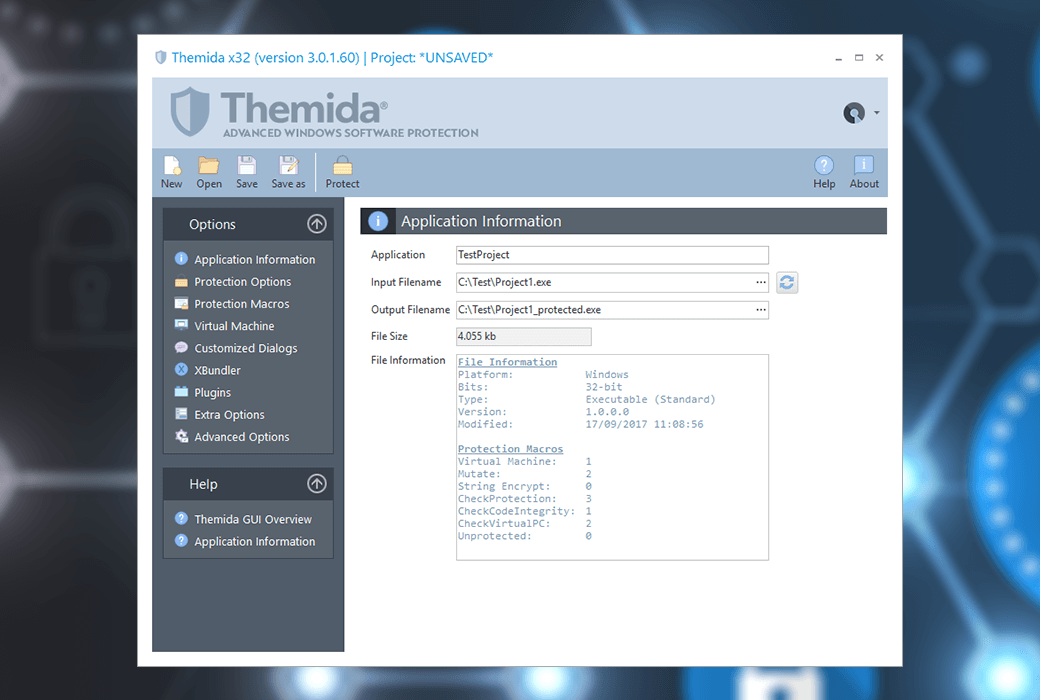
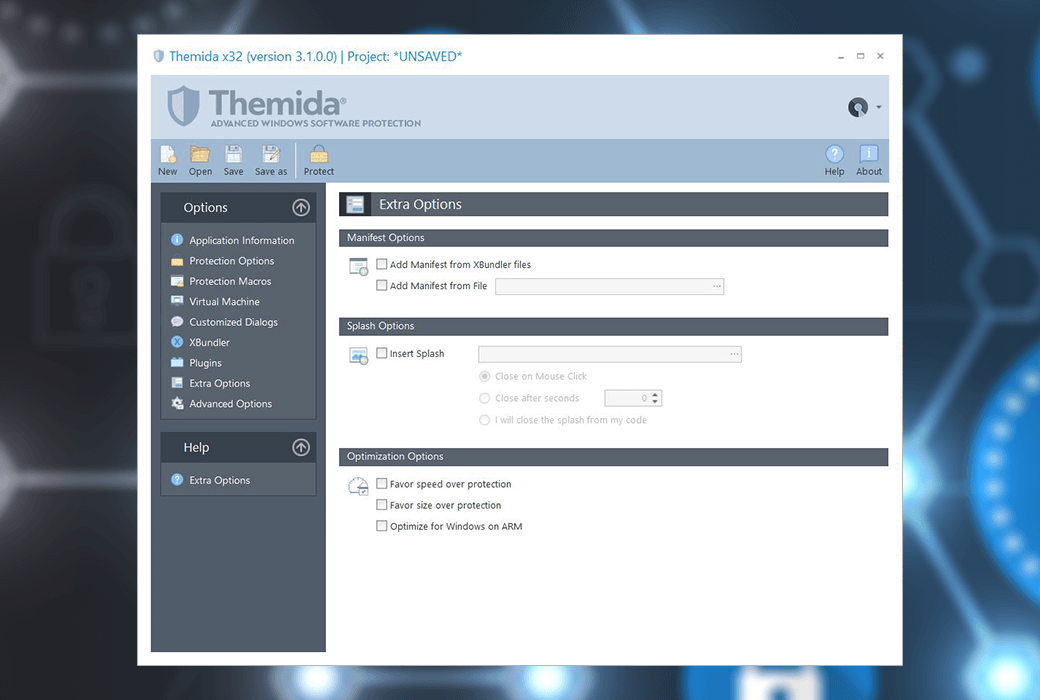
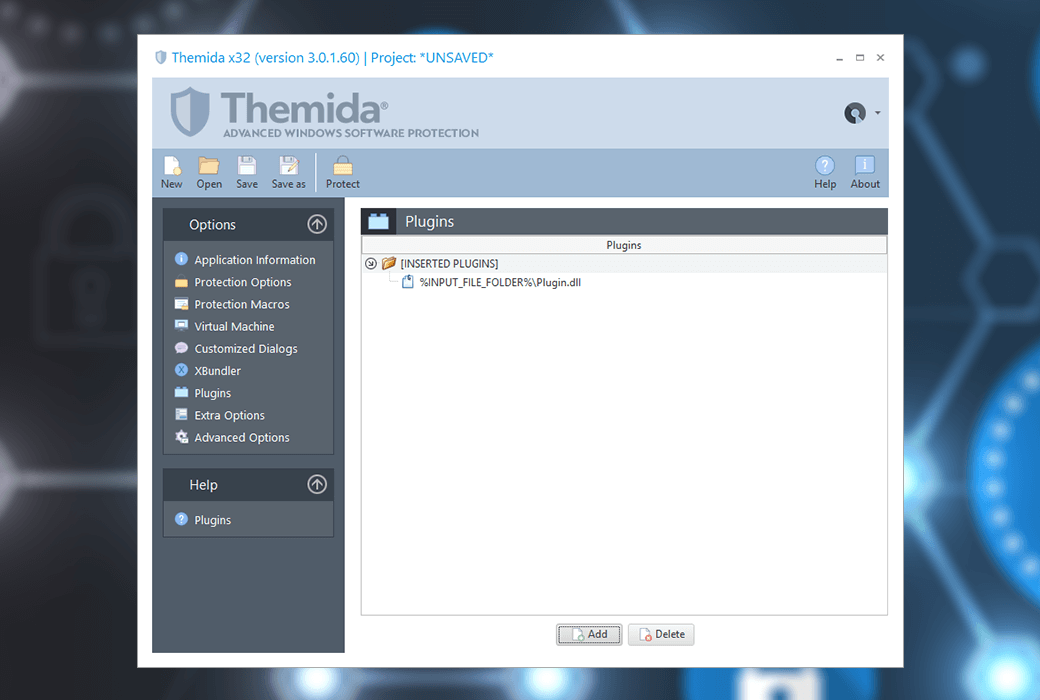
Themida Advanced Windows Software Protection System
Understand the risks
When developing an application, the compiler compiles the application's source code into multiple object files composed of machine language code. Subsequently, these target files will be linked together to form the final executable file.
Just as the source code of an application is converted into machine code during compilation, there are also tools that can convert compiled applications into assembly language or higher-level programming languages. These tools are called disassemblers and decompilers.
Attackers can use disassemblers or decompilers to study the working principles of specific applications and the functionality of specific routines. Once the attacker has a thorough understanding of the target application, they can modify the compiled application to alter its behavior. For example, attackers can bypass the routine that checks the trial period of an application, making it run permanently, or even worse, making the application appear as if it is already registered.
Software Protector
The emergence of software protectors aims to prevent attackers from directly inspecting or modifying compiled applications. Software protectors are like shields, encrypting and protecting applications from potential attacks. When a protected application is to be run by the operating system, the software protector will first control the CPU and check if any possible cracking tools (disassemblers or decompilers) are running on the system. If everything is safe, the software protector will start decrypting the protected application and hand over control to the CPU to make it run as normal.
The advantages of using software protectors include:
- Protect applications from piracy infringement.
- Prevent attackers from researching the implementation methods of applications.
- Attackers are not allowed to modify the application to alter its behavior.
weakness
Since the birth of software protectors, many attackers have focused most of their efforts on attacking the software protector itself rather than the application. Many tools have been developed to assist in attacking software protectors. These attacks typically result in attackers obtaining the decrypted and unprotected original application.
The main issue with software protectors is that the protection techniques they use are well-known to crackers, so they can be easily bypassed using traditional cracking tools. Another important issue with software protectors is that they are restricted by the operating system to run with normal application privileges. Therefore, attackers can use cracking tools that run at the same priority as the operating system to fully monitor the behavior of software protectors at specific times and launch attacks at specific locations.
Revolutionary solution
With Themida ®, We focus on the main weaknesses of software protectors, providing a comprehensive solution to overcome these issues. Themida ® Using SecureEngine ® Protection technology, implementing unprecedented protection measures at the highest priority to protect applications from advanced software cracking.
SecureEngine ® Defeated all current cracking tools available for attacking protected applications and ensured that protected applications only run in a secure environment.
The current protector claims to be professional!
Software protection programming is not a very familiar field for most programmers. Software protection technology cannot be seen and compared like "visible" features. Therefore, most software protection authors will talk about the impressive techniques contained deep within the protection scheme, but many times, these techniques are almost non-existent or much simpler than they seem. Most software protectors repeatedly emphasize the use of very powerful encryption algorithms such as RSA, elliptic curves, and AES, hoping that end users will believe that these protectors and encryption algorithms are unbreakable. However, this is far from the truth, as software protection is very different from data protection. Even if software protectors use the most powerful encryption algorithms to encrypt protected applications, sooner or later they will need to decrypt the protected applications in order for the CPU to run them. It is at this stage that most attackers will start working, dumping decrypted applications from memory to disk, thus eliminating the need to process encryption algorithms and rebuild the original application.
mission
In Themida ®, We hope to take a realistic view of the weaknesses that attackers can exploit, as well as the content that we truly need to pay attention to when protecting applications, in order to provide the highest level of security protection and prevent software cracking.
function
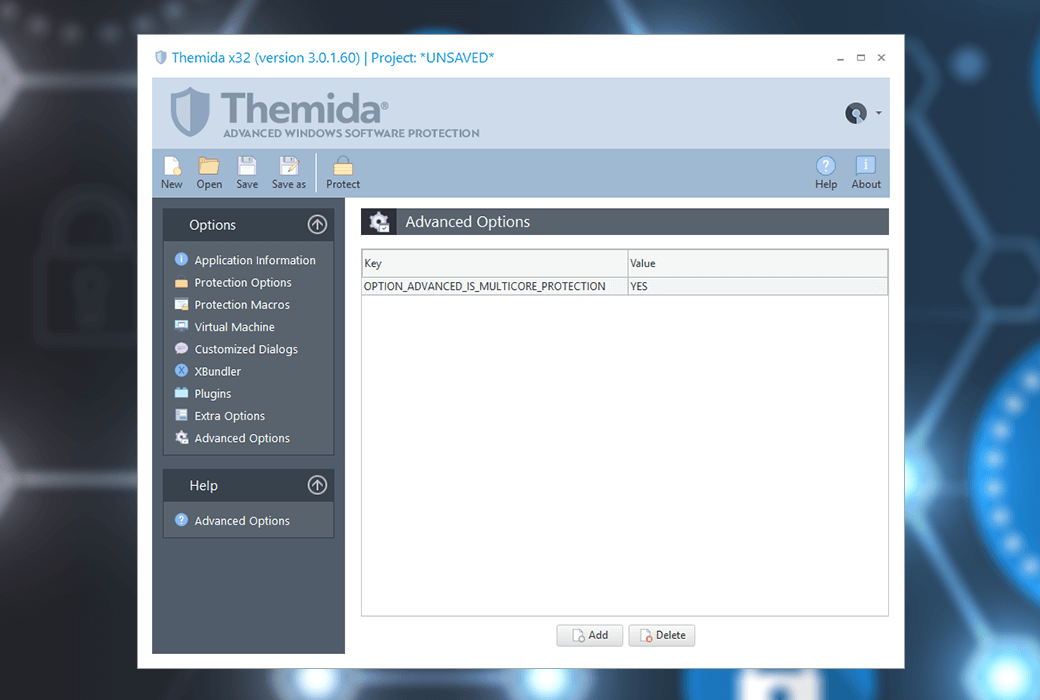
Here is Themida ® Key functions:
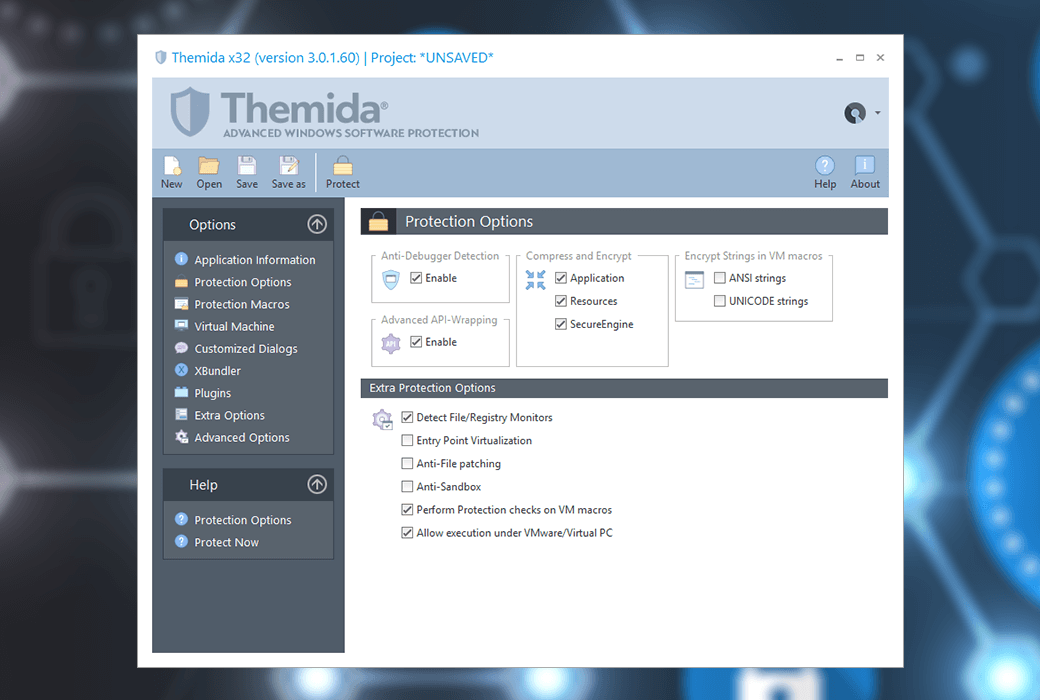
- Anti debugging technology that can detect/deceive various debuggers
- Each protected application uses different encryption algorithms and keys
- Anti API scanning technology to prevent the reconstruction of the original import table
- Technologies for automatic decompilation and obfuscation of target applications
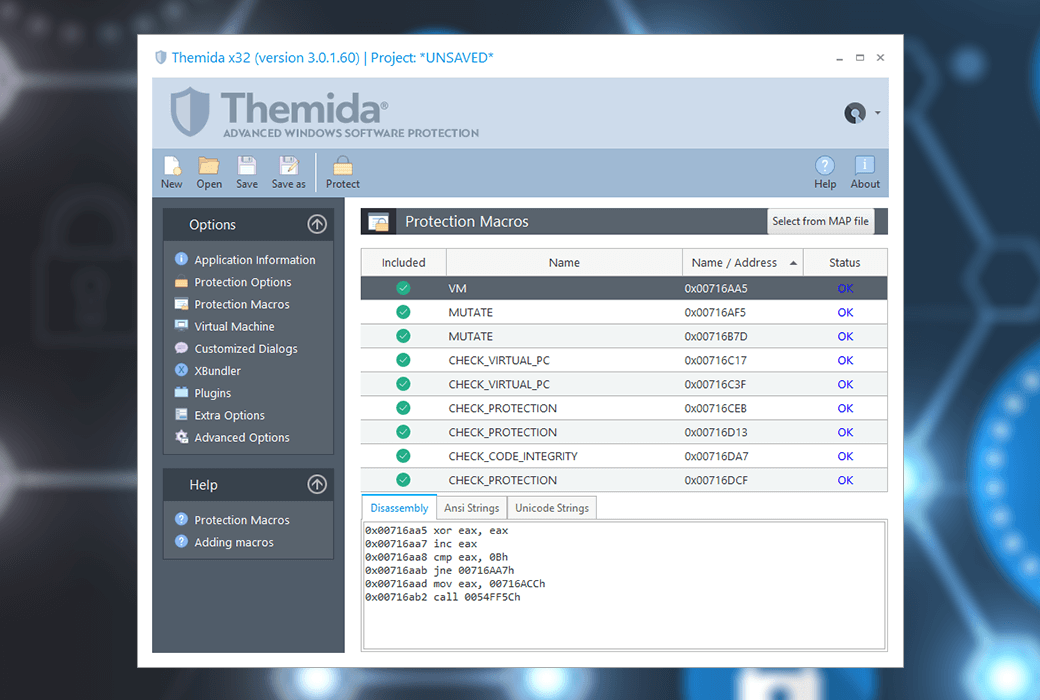
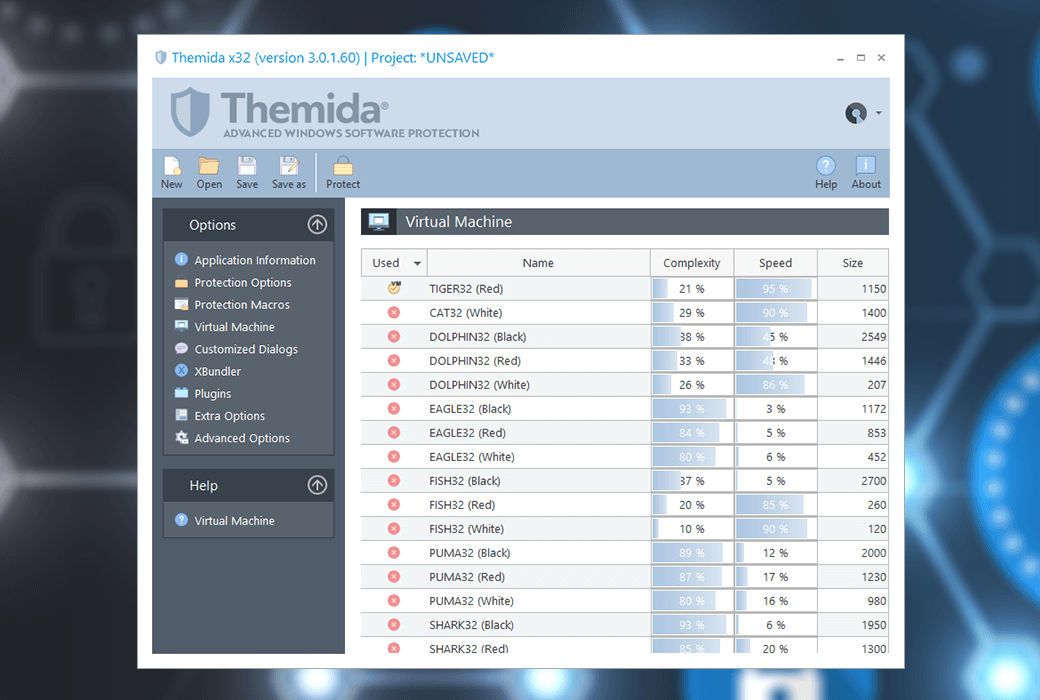
- Perform virtual machine simulation in specific code blocks
- Advanced Mutation Engine
- Communicate with the SDK of the protection layer
- Disassembly techniques for any static and interactive disassembler
- Multi layer polymorphism technology with over 50000 permutations and combinations
- Advanced API Packaging Technology
- Anti monitoring technology, targeting file and registry monitors
- Insert random garbage code between real instructions
- Specialized thread protection
- Advanced Thread Network Communication
- Anti memory patching and CRC techniques for target applications
- A deformation engine used to obfuscate original instructions
- Advanced entry point protection
- Dynamic encryption in the target application
- Insert anti tracking code between real instructions
- Advanced anti breakpoint manager
- Real time protection in target applications
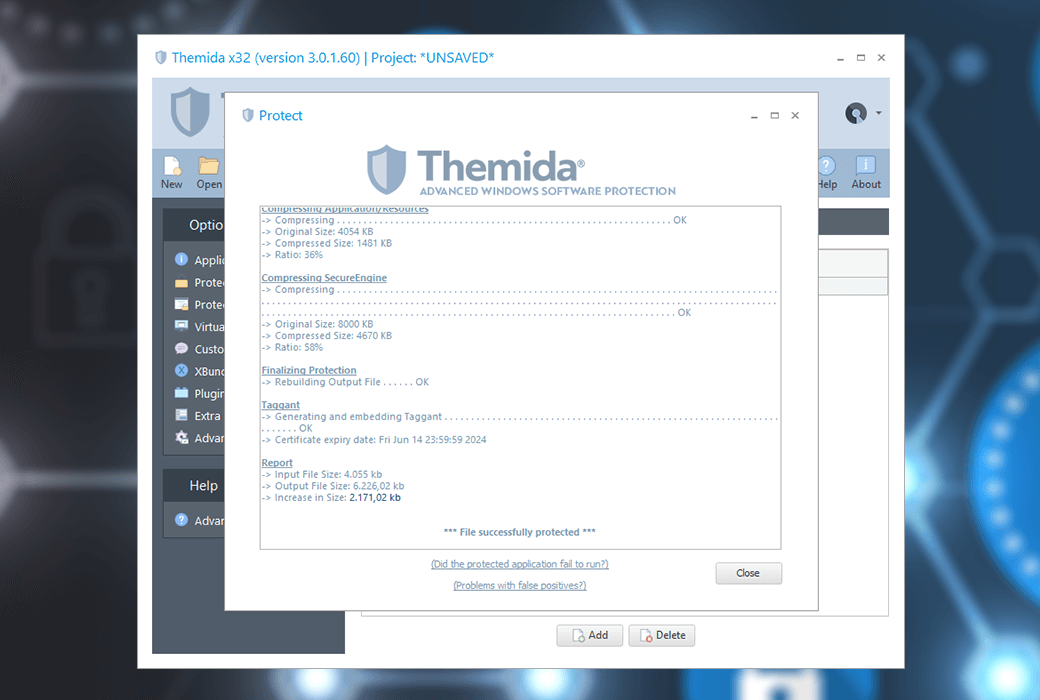
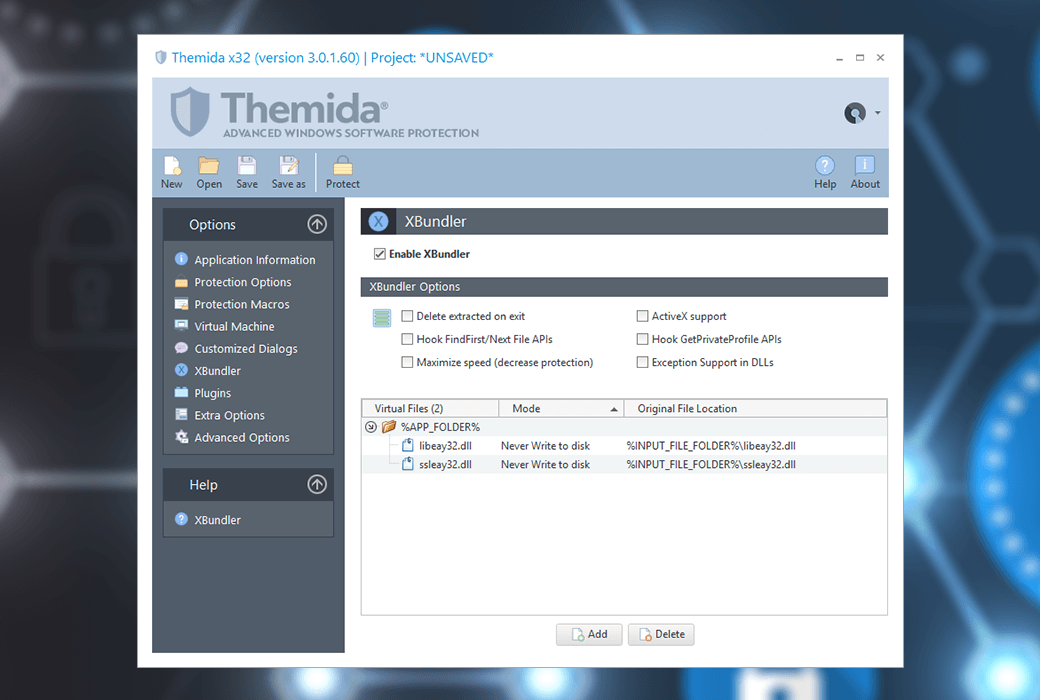
- Compress target applications, resources, and protected code
- Anti 'debugger hider' technology
- Protect code from comprehensive variation and avoid pattern recognition
- Real time simulation in the target application
- Intelligent protection code inserted into the target application
- Random internal data relocation
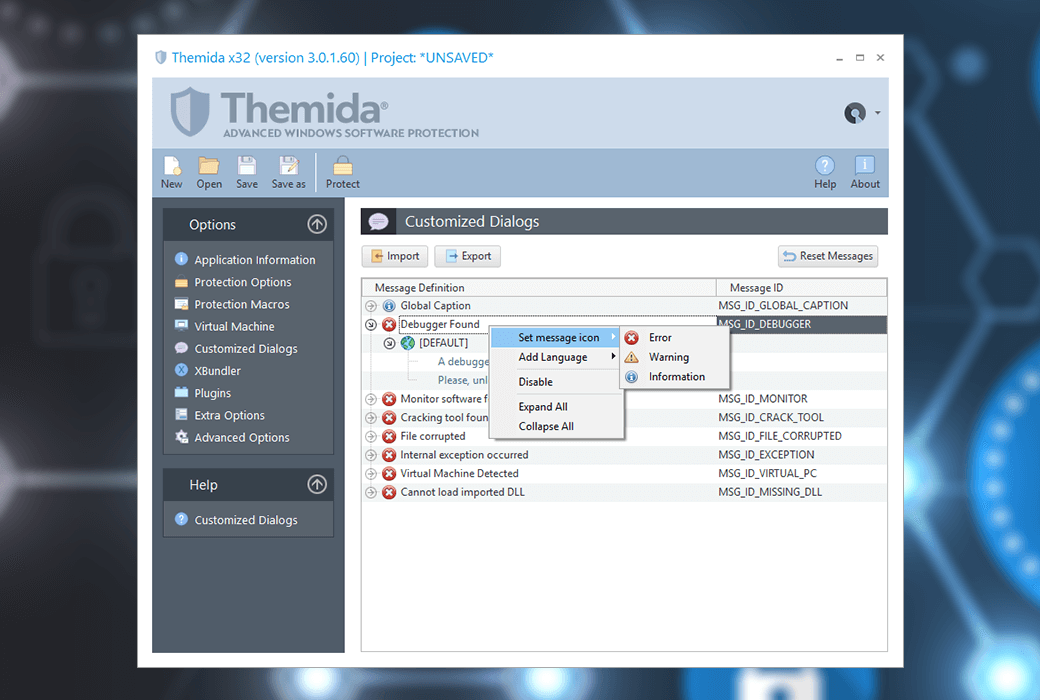
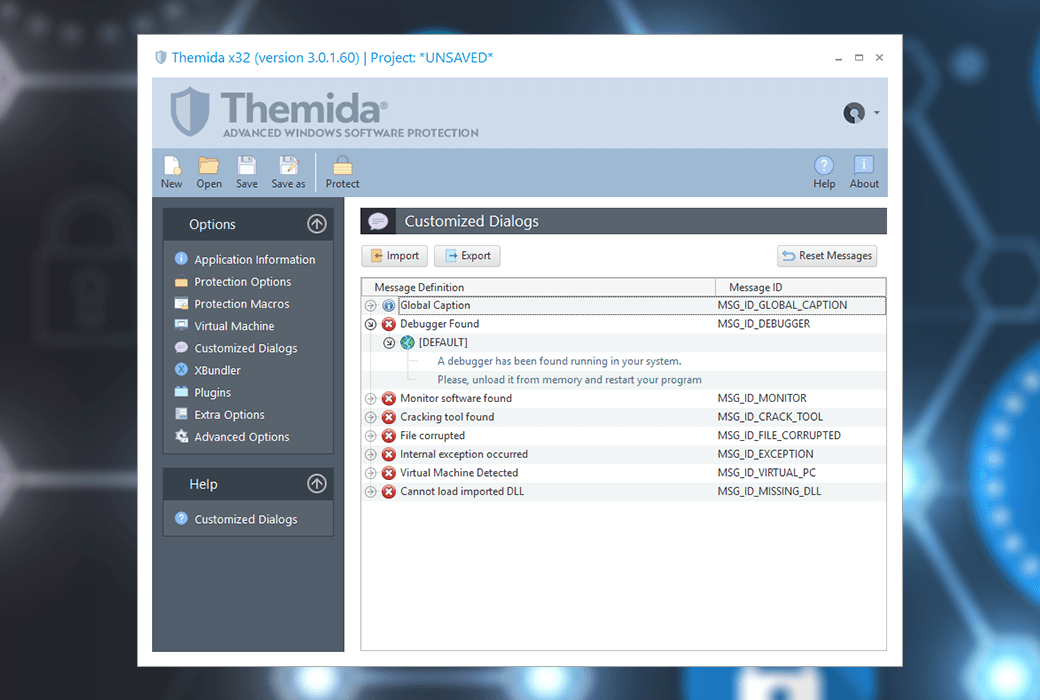
- Customizable dialog boxes in protected applications
- Support command line
- There are many more functions
Official website:https://www.oreans.com/Themida.php
Download Center:https://themida.apsgo.cn
Delivery time:manual processing
Operating Platform:Windows
Interface language:Support English interface display.
Update Description:Support 1-year maintenance and updates after purchase.
Trial before purchase:Free trial is available before purchase.
How to receive goods:After purchase, the activation information will be sent to the email address at the time of placing the order, and the corresponding product activation code can be viewed in the personal center, My Orders.
Number of devices:Can install one computer.
Replace computer:Uninstall the original computer and activate the new computer.
Activation guidance:To be added.
Special note:To be added.
reference material:https://www.oreans.com/help/tm/

Any question
{{ app.qa.openQa.Q.title }}