Do More With the
Team You Have

Security Teams Are Overwhelmed Because
Their Tools Work Against Them
Your analysts are skilled. Your stack is loaded. But every day, your team drowns in alerts, manually stitches together findings across dozens of dashboards, and still can’t confidently answer what’s actually at risk.
Thousands of alerts, zero context
Your tools generate more signals than any team can process. Without cross-domain context, analysts spend hours triaging noise instead of addressing real threats – and the exposures that matter stay buried.
Manual correlation eats every cycle
Vulnerability scanners, CSPMs, CIEMs, and identity tools each produce their own findings. Connecting the dots between them requires manual effort, specialized expertise across every tool, and slow, error-prone investigation.
Reactive cycles that never end
Teams chase incidents and patch individual findings without understanding the underlying exposure chains. The cycle repeats — more alerts, more scrambling, no systemic progress on actual risk reduction.
Mesh CSMA: Maximize the Impact of Every Analyst Hour
Mesh replaces manual correlation and alert triage with a unified intelligence layer that tells your team exactly where to focus – and why it matters.
How Mesh Works:
Replace Alert Noise with Prioritized Attack Paths
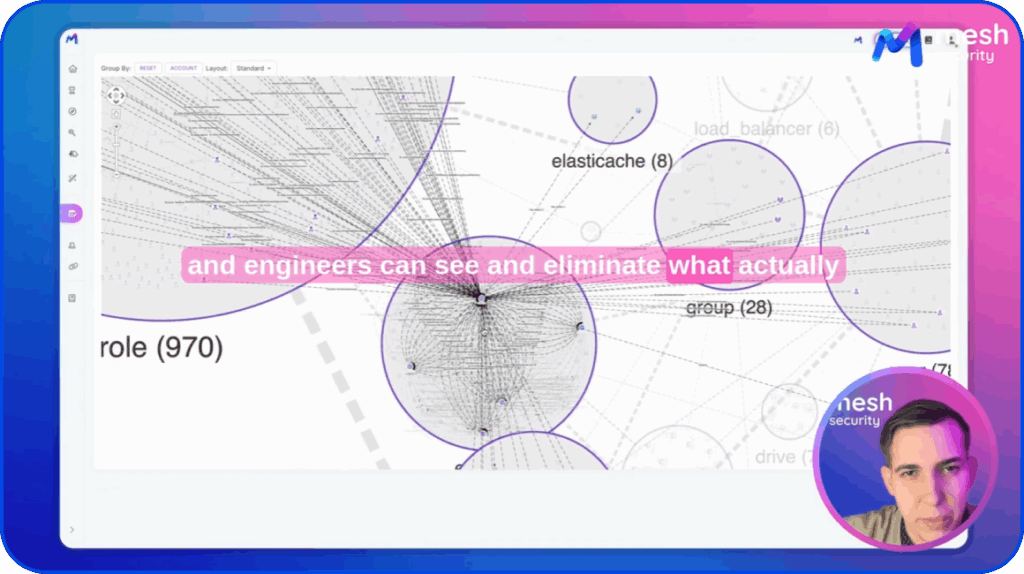
Eliminate Manual Correlation Across Domains
Drive Systematic Remediation, Not One-Off Fixes
Stop Triaging Noise. Start
Eliminating Exposure.
See and eliminate complete post-phishing attack paths before attackers find them
Spend analyst time on what actually threatens the business
Onboard faster, scale without headcount

Measure and report progress that matters
Make your entire stack work harder
Customers Who
Love Mesh:
a clear way to understand where their security program stands, identify the real gaps, and actually close them.
Resources
Ready to see Mesh
in action?
See your real security exposure
across identity, cloud, SaaS, and endpoints –
and eliminate it in minutes.