Maximize Security Stack Efficiency

Tool Sprawl Created Visibility – But
Destroyed Context
The average enterprise deploys 83 security tools across 29 vendors. Each tool solves a real problem. Each dashboard shows valuable data.
But your stack can’t answer the question that matters: which exposures create viable attack paths to Crown Jewels?
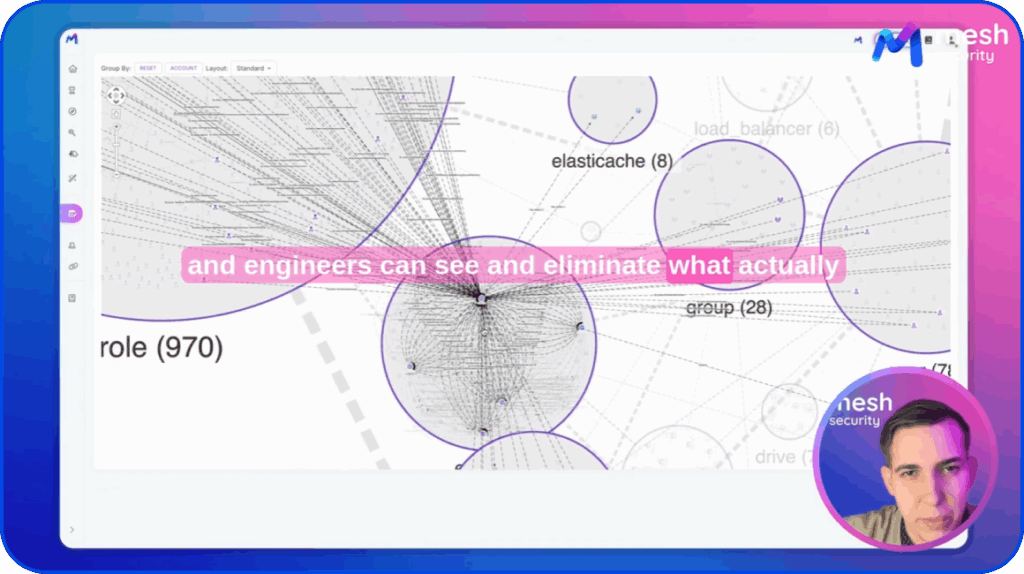
Fragmented visibility without unified context
Your tools show risks in isolation. None of them show how these exposures chain together across domains to threaten critical assets.
Alert fatigue drowning security teams
10,000 CSPM alerts. 5,000 CIEM findings. 8,000 vulnerabilities. 50,000 SIEM events daily. Your team can't distinguish signal from noise—and can't prioritize based on real business risk.
Manual correlation burning resources
Security analysts spend hours stitching signals together across dashboards, trying to understand if isolated findings create actual attack paths. By the time they piece it together manually, new exposures have already emerged.
Mesh CSMA: Your Stack, Unified
Mesh transforms tool sprawl into a unified execution model – without replacing a single tool.
How Mesh works:
Connect and Unify Your Entire Stack in Minutes
Surface What Actually Threatens the Business
Drive Remediation Through the Tools You Already Have
Stop Managing Tools. Start Eliminating Attack Paths.
One view instead of dozens of dashboards

Context that connects the dots automatically

Signal instead of noise

Make your stack work as one system

Autonomous orchestration across domains

ROI from tools you already own
Customers Who
Love Mesh:
a clear way to understand where their security program stands, identify the real gaps, and actually close them.
Resources
Ready to see Mesh in action?
See your real security exposure
across identity, cloud, SaaS, and endpoints –
and eliminate it in minutes.