Turn Any Security Stack into One System
You’re still exposed
Many Tools ≠ Secured.
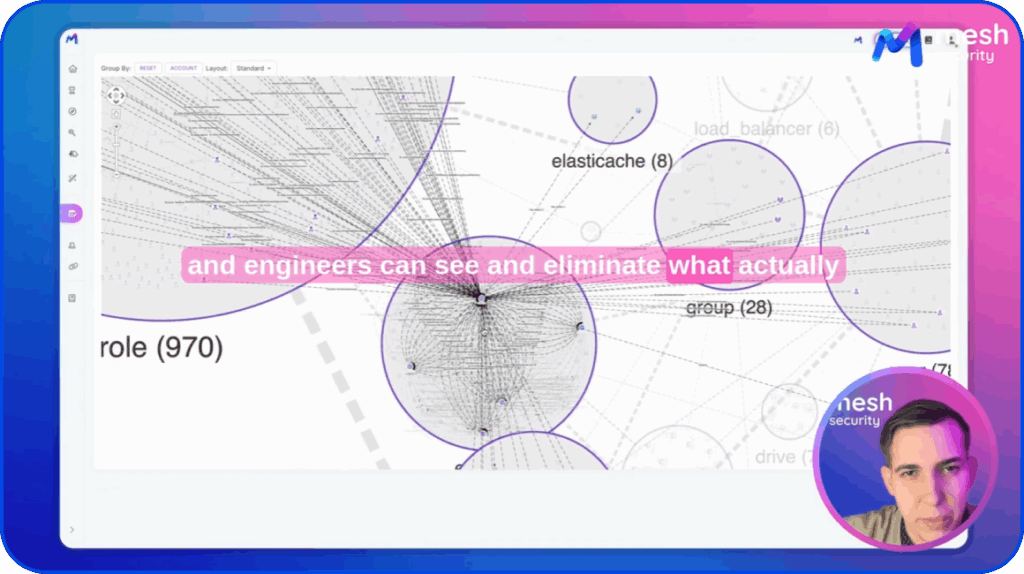
Mesh reveals and eliminates exposure across the enterprise.
Now, and tomorrow.
Companies that trust Mesh Security







You are Accountable for
What You Can’t Control
Security tools keep multiplying, but security risk remains hidden. Bringing
all the context into one place is cost-prohibitive.
Dozens of Dashboards
Security visibility is fragmented across too many tools. Understanding real exposure requires jumping between consoles and manually connecting the dots.
Disjointed Security Data
Logs, alerts, and findings keep growing, but clarity doesn't. Without shared context, signal is indistinguishable from noise. More data doesn't mean better security.
Manual Correlation
Security teams parse through thousands of findings trying to connect the dots to identify viable attack paths, instead of stopping real threats.
Assume Breach, Eliminate Exposures
Are our Crown Jewels exposed?
Mesh continuously assesses and fixes posture risks, detection gaps, and real-world attack paths, before attackers find them.
Connect
Set up in 3 min. Agentless. No rip & replace.
See
Discover Crown Jewels, unveil attack paths.
Assess
Continuously surface gaps and assess maturity.
Eliminate
Break business-critical exposures first.
Defend
Keep all Crown Jewels secured. Stay threat-ready.
How Does It Work?
Threat resilience
using the tools you already have
Outcomes your
board cares about
- Quantify and reduce financial risk
- Measure and improve Zero Trust posture
- Reduce exposure across domains
- Clearer, faster, more confident reporting

seamlessly with
Security leaders say:
a clear way to understand where their security program stands, identify the real gaps, and actually close them.
Meet Mesh Agents
Eliminate posture exposures.
Detect, investigate, and thwart real-time threats.
Get full context, no limits.
From Assuming to Сontinuous Сontrol
One view of the enterprise that CISOs can finally trust.
Get a Zero Trust Posture Assessment now.
A unified intelligence layer that connects your existing security tools, data lakes, and infrastructure to reveal how everything in your environment relates – enabling complete visibility, context, and control.
CSMA unifies SIEM with your other tools to provide the cross-domain context, attack path visibility, and posture maturity assessment that SIEM alone can’t deliver. While some companies use CSMA instead of a SIEM, that’s not the primary use case.
Agentless API-based deployment connects to your existing security stack in minutes – no rip and replace. All telemetry flows into one unified enterprise context graph automatically.
CSMA continuously assesses your posture against all 6 Zero Trust pillars, performs gap analysis, and validates security controls across your entire environment.
Blog
Ready to see Mesh
in action?
See your real security exposure
across identity, cloud, SaaS, and endpoints –
and eliminate it in minutes.