Agentic Security where it matters.
At the action.
Your agents are performing actions with APIs and MCP servers you don't know exist. Salt secures all of it, from code to runtime.
AI agent anatomy
An AI Agent is like a digital employee.
And like any employee, what matters isn't what they think.
It's what they do.
Agentic Security
Most AI Security stops at the model. Attackers don't.
The model security said everything was fine.
Everything was not fine.
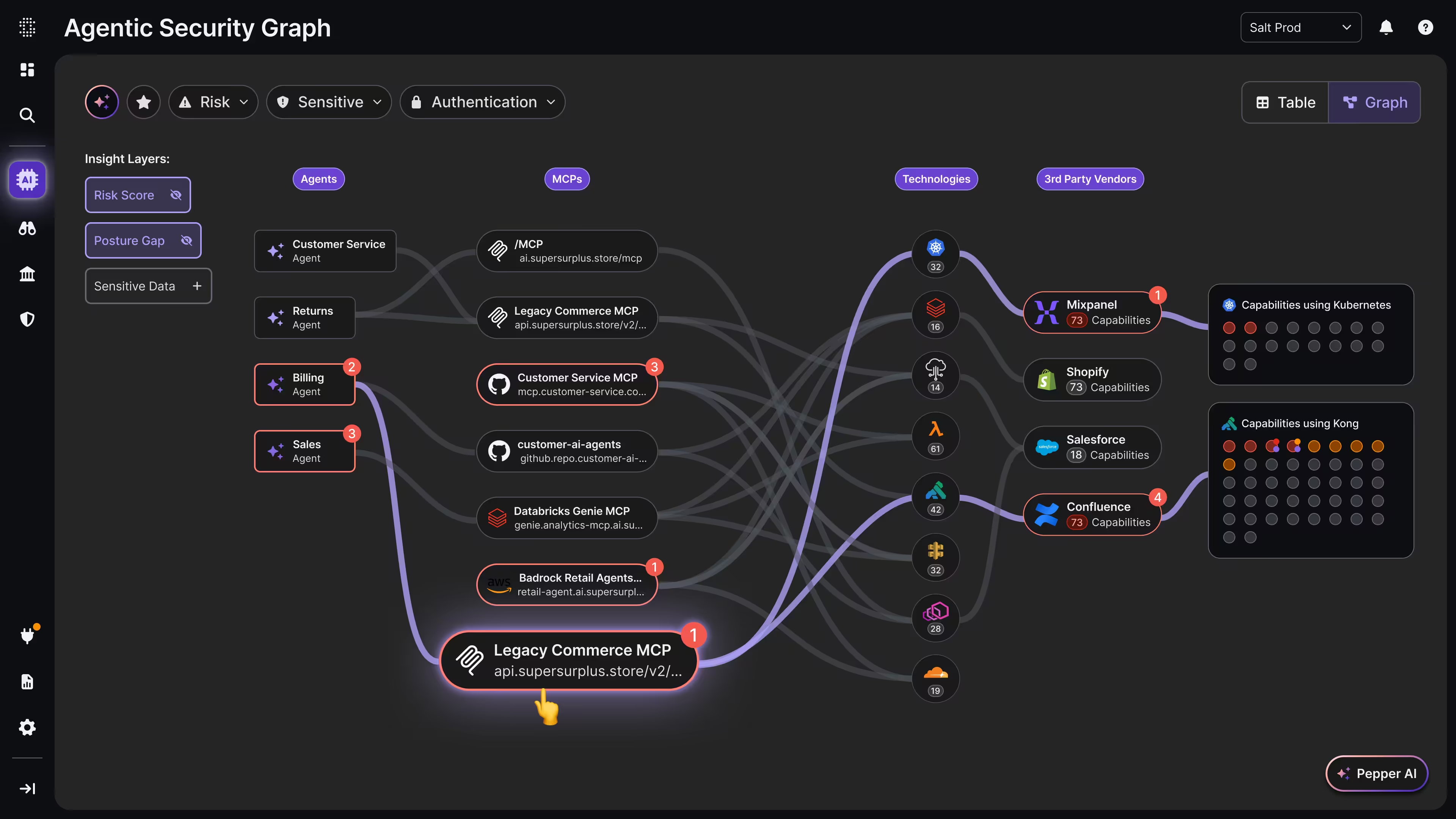
The agentic security graph
Visibility isn't enough. You need context.
Not every agent carries the same risk. Salt's Agentic Security Graph contextualizes risk across your entire environment, separating the agents that can cause real damage from those that cannot.
That is the holistic view no other platform can give you.

The Agentic Stack has three pillars.
All three must be secured.
If any one pillar is compromised, the entire stack is compromised. Most vendors secure one. Salt secures all three.
- LLMs: If the brain is manipulated, every decision downstream is compromised.
- MCP servers: If the hands are unguarded, attackers control what agents can reach and do.
- APIs: If the action layer is unsecured, the blast radius is your entire enterprise.
Salt agentic security Platform
From agent to API.
The full agentic lifecycle, secured.
Most platforms secure a slice of your agentic environment. Salt was built to secure all of it. Eight years of API security research, applied across the full Agentic Security Graph, from the moment an agent is deployed to every action it takes at runtime.

Agentic Discovery
You can't secure what you can't see. Salt automatically discovers every agent, MCP server and API across your environment, including the shadow and zombie APIs nobody knows are there
- AI agents across enterprise environments
- MCP servers and connected tools
- Internal, partner, and public APIs
- Shadow and zombie APIs
Posture Management
Knowing what exists is only the first step. Salt analyzes every component in your Agentic Security Graph for misconfigurations, excessive permissions, and exposed credentials, before an attacker finds them.
- Exposed internal APIs
- Authentication and authorization weaknesses
- Hardcoded tokens and credentials
- Risky MCP configurations
- Excessive permissions granted to agents

Runtime Protection
Agents move at machine speed. So does Salt. Real-time detection of abuse, anomalous behavior, and active attacks across the full graph, including the internal traffic your perimeter tools never see.
- API activity generated by agents
- MCP tool usage
- Data access patterns
- Abnormal or risky behavior
Assess your risk
See your Agentic Security Graph in minutes.
Most organizations are shocked by what Salt finds. See every agent, MCP server and API operating across your environment, including the ones you don't know about.






















