Secure your code, supply chain and runtime instantly
Equip your engineers with the only AppSec tool they need to ship safely.
Continuous SAST, SCA, Secrets, IaC and DAST scans, all in one place.
Compliance-ready AppSec baked into your workflow
Make application security a by-product of your SDLC,
not a flow-stopper for your engineers.

“Codacy makes sure we do code security testing automatically so the devs don't have to worry about it.”
Daan van Leth AI Solutions Consultant at ihomer

Application Security for busy engineering leaders
Add your Git projects with two clicks, see scan results in minutes, and watch your devs and agents ship better, more secure code instantly.
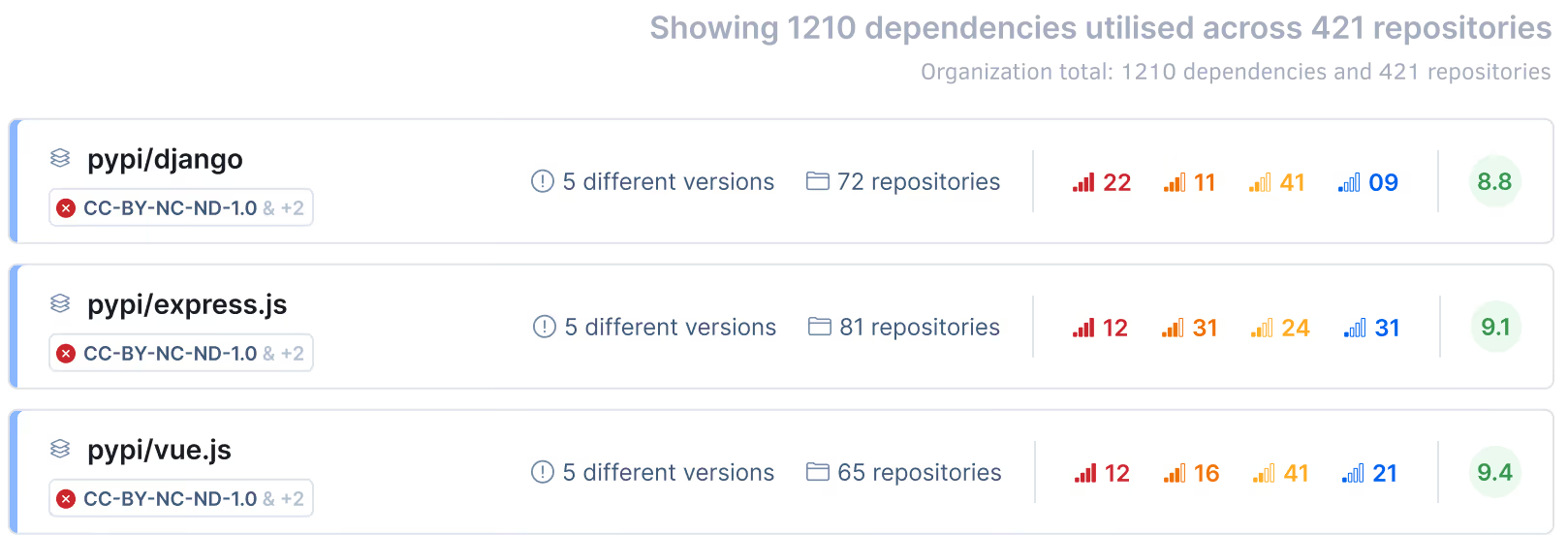
Daily CVE and malicious package re-scans
Protect new and old code against insecure libraries and malicious packages, with daily CVE database updates.
Review
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Catch hardcoded secrets and credentials pre-commit
Identify exposure risks like leaked credentials, unprotected tokens, and service keys before they enter version control.
Review
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls
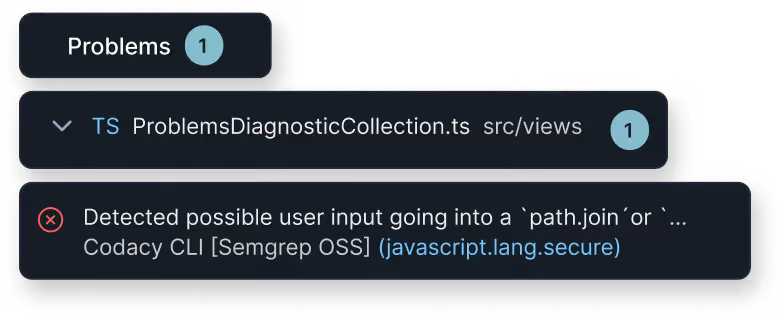
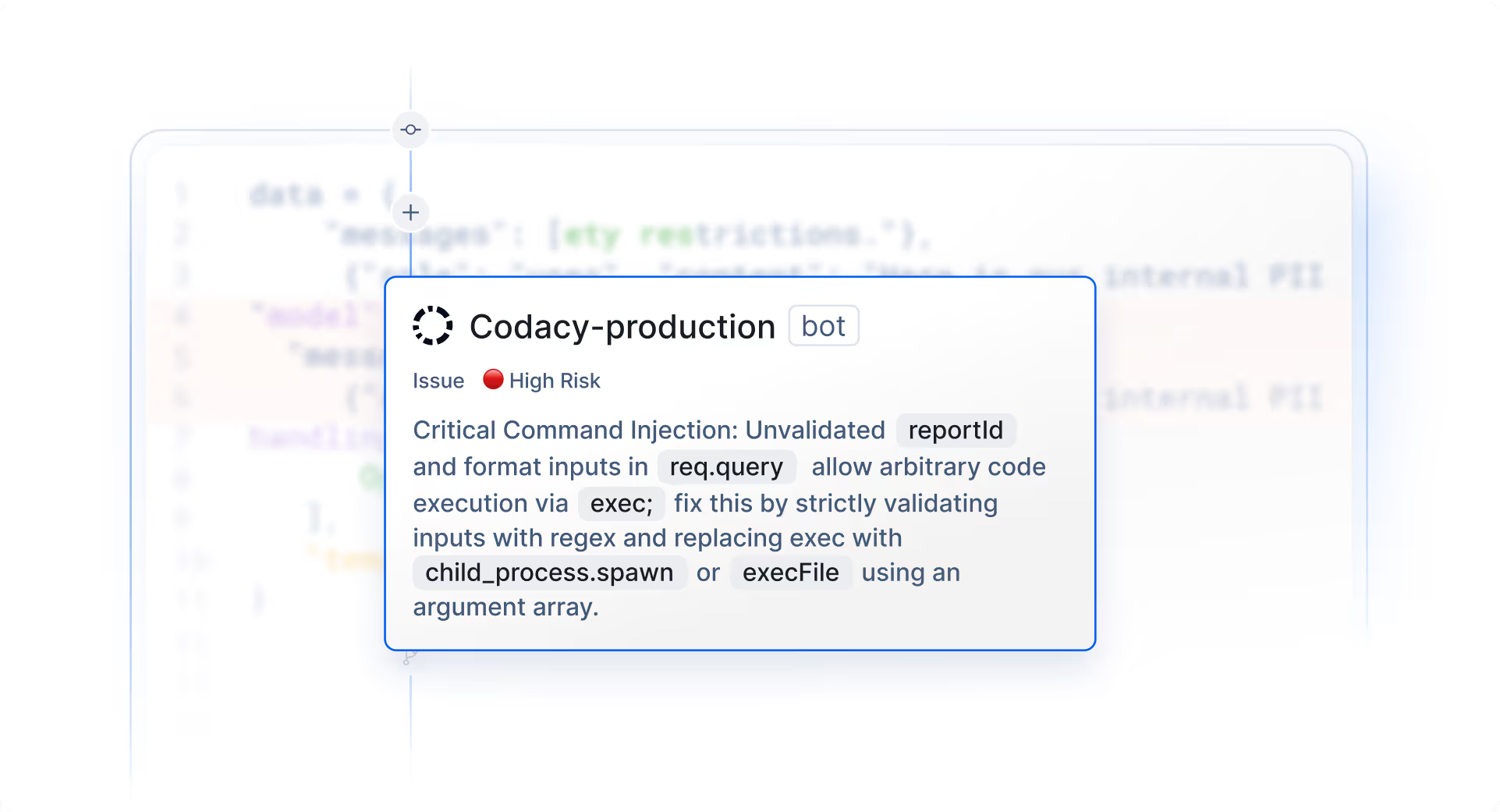
AI Guardrails built into every agent and IDE
Enforce secure coding practices and vulnerability guardrails for all AI-generated code suggestions in real-time.
Review
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls


Centralized AI Coding Policies
Enforce AI Coding Policies to catch risks like unapproved AI models and vulnerable libraries from outdated training data.
Review
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls


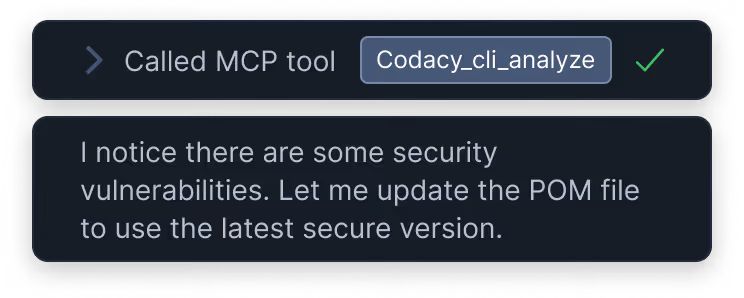
Built for agentic workflows
Turn your security policies into automated guardrails for every AI coding agent used by your devs. Open review-ready Pull Requests on first try.
Get the security context your agent is missing
Codacy Guardrails brings reliable, deterministic code analysis inside your agentic workflow, making your coding agents follow the rules you define, consistently. Give your agent the context it needs to auto-repair new and old code on the fly.
Get secure AI code on every prompt
Codacy Guardrails silently scans every line of AI code against your security policies, whle it's being generated. Let your agent auto-fix its own issues, before you even see the code.
Review
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls


Patch legacy vulnerabilities without leaving the chat panel
Turn Codacy’s scan results into actionable context for your AI agents. Empower them to auto-remediate every identified vulnerability across your legacy codebase with verified precision.
Review
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls


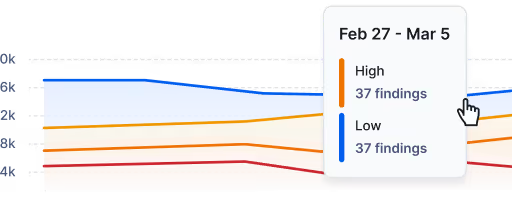
Adjust your policies and get security reports
Set your AI Guardrails to match your organization's security policies and apply them across agents and IDEs. Generate comprehensive security reports across teams and projects.
Review
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls


Loved by engineers
Codacy has changed the way engineering teams ship secure, high-quality applications without sacrificing speed.
Lorem ipsum
Enforce secure GenAI code on every prompt
"Easy to integrate, hard to give up!"
Mustafa O.
Engineering Lead
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Lorem ipsum
Enforce secure GenAI code on every prompt
"Reduces the amount of bloat, bugs, and other issues we experience."
Michael P.
CTO
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Lorem ipsum
Enforce secure GenAI code on every prompt
"Quality and speed, Codacy gives us both. I love these guys."
Mykel A.
Engineering Manager
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Lorem ipsum
Enforce secure GenAI code on every prompt
"Our overall code quality has improved significantly."
Sarang K.
Technical Project Manager
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Lorem ipsum
Enforce secure GenAI code on every prompt
"Crucial to the success of our projects."
Michael G.
Principal Engineer
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Lorem ipsum
Enforce secure GenAI code on every prompt
"A great product. I have recommended all my community friends to use it."
Xiao Y.
CTO
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Lorem ipsum
Enforce secure GenAI code on every prompt
"Reduces time on code reviews."
Madalin V.
Senior Software Engineer
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Lorem ipsum
Enforce secure GenAI code on every prompt
"Helps devs save time in code reviews, so they can focus on other things."
Miroslav B.
Senior Card System Architect
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Lorem ipsum
Enforce secure GenAI code on every prompt
"Raising our quality and security standards, giving quick feedback to our devs to ensure that we don't lose agility."
Vinicius P.
Mid-market
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Lorem ipsum
Enforce secure GenAI code on every prompt
"Helps us meet compliance requirements and improve code quality across our product."
Verified User
Education Management
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Lorem ipsum
Enforce secure GenAI code on every prompt
"It's automatic, with like zero config to be functional."
Romain M.
Lead Developer
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls


Ready to dive in?
Start your free trial today