Inspiration
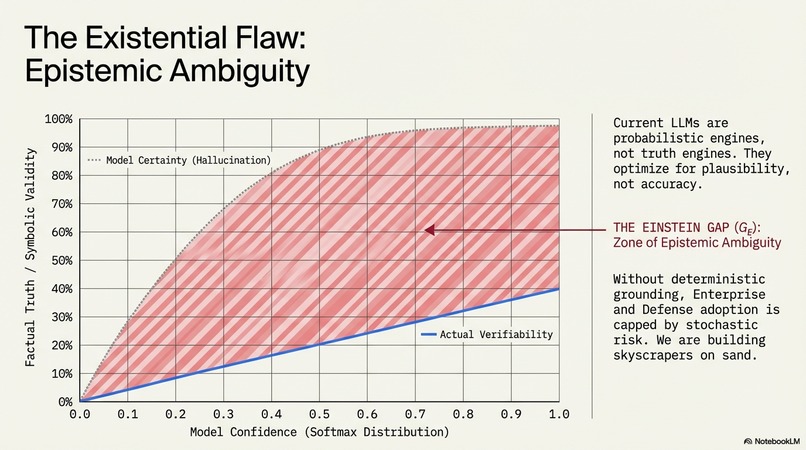
Modern AI and emerging quantum computing systems rely heavily on probabilistic models. These systems can generate powerful results, but they also introduce unpredictability. When AI outputs directly control real-world systems—such as robotics, energy infrastructure, or distributed networks—this unpredictability becomes a reliability and security risk.
This project was inspired by the need to bridge what I call the “Einstein Gap”: the mismatch between probabilistic software decisions and the deterministic laws that govern physical systems.
The goal is to move from systems that guess outcomes to systems that verify outcomes before execution through deterministic hardware logic.
What it does
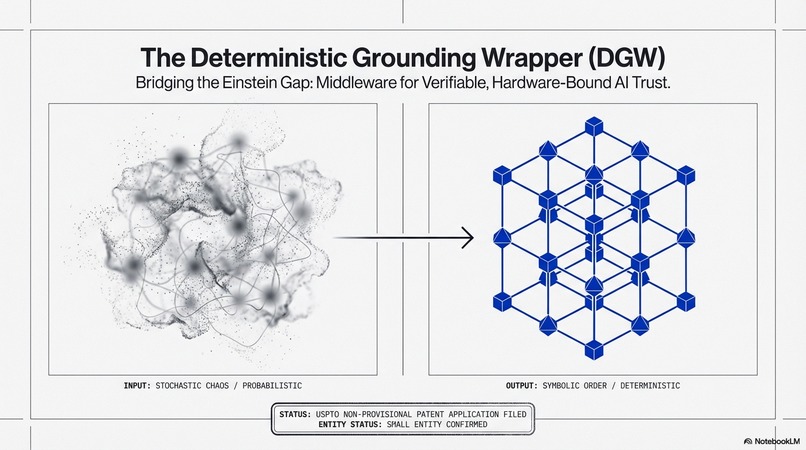
The Biological-Digital Seal is a deterministic infrastructure layer designed to make AI-driven systems more reliable, secure, and energy efficient.
Modern AI models generate outputs probabilistically, which means the same input can produce different results. While this is useful for learning and creativity, it can create instability when AI controls real-world systems such as robotics, autonomous vehicles, energy grids, or large cloud infrastructures.
This project introduces a hardware-verified validation layer that sits between AI models and system execution.
Instead of allowing AI outputs to execute directly, the system:
• Validates AI commands against deterministic safety and logic constraints • Stabilizes distributed computing nodes by suppressing synchronization noise • Verifies command identity through hardware-based authentication • Converts probabilistic AI outputs into deterministic system actions
This creates a secure pipeline where AI can still generate insights, but only validated outputs are allowed to control infrastructure.
The result is a computing architecture that can support:
secure autonomous systems
stable AI cloud infrastructure
distributed robotics and drone networks
high-reliability computing environments
By introducing deterministic validation into AI infrastructure, the system reduces instability, improves security, and enables safer deployment of advanced AI technologies.
How we built it
We built this project by designing and modeling a deterministic infrastructure layer that sits between AI models and real-world system execution. The goal was to demonstrate how probabilistic AI outputs can be validated, stabilized, and securely executed through hardware-aware logic.
System Architecture Design
The first step was defining the architecture of the Biological-Digital Seal, which consists of five functional nodes that form the deterministic control pipeline:
Validation Node – checks AI outputs against deterministic safety and logical constraints before execution.
Synchronization Suppression Node – stabilizes communication across distributed computing systems by filtering redundant signal noise.
Identity-Locked Security Node – uses hardware-based authentication to verify command origin and prevent malicious code execution.
Ambient Stabilization Node – maintains timing coherence across computing nodes in large-scale distributed environments.
Deterministic Execution Node – converts validated outputs into safe system-level commands.
These nodes collectively form the 3240 Logic Layer, a deterministic middleware architecture that bridges probabilistic AI outputs with deterministic infrastructure.
Mathematical Modeling
To evaluate system reliability, we modeled the relationship between probabilistic AI outputs and deterministic validation using a constraint framework that minimizes recomputation overhead caused by stochastic variance.
This modeling helped identify the synchronization and validation bottlenecks in modern distributed AI systems.
Hardware-Oriented Design
We focused on integrating the system with hardware-level components, particularly memory controllers and distributed compute nodes. This allowed us to design the Synchronization Suppression Module, which stabilizes node communication and reduces redundant signal processing in large computing clusters.
Intellectual Property Integration
The architecture builds upon a series of USPTO non-provisional patent applications covering deterministic validation middleware, synchronization suppression modules, identity-locked hardware verification, and distributed system stabilization.
These filings provided the conceptual and technical framework for implementing the deterministic infrastructure model demonstrated in this project.
Challenges we ran into
One of the biggest challenges in this project was bridging the gap between probabilistic AI systems and deterministic infrastructure. Modern AI models are designed to generate outputs using stochastic processes, while real-world systems—hardware controllers, energy systems, and distributed networks—require deterministic and reliable behavior. Designing an architecture that could safely translate between these two paradigms required careful system modeling.
Another challenge involved synchronization in distributed computing environments. Large-scale systems such as GPU clusters and quantum computing nodes often experience timing drift, signal overlap, and network congestion when thousands of nodes communicate simultaneously. Addressing this required developing a synchronization suppression approach that reduces redundant signals while maintaining stable timing across nodes.
We also encountered challenges in designing hardware-aware validation mechanisms. Most AI safety approaches rely on software guardrails, but integrating validation logic that works alongside hardware controllers requires a deeper understanding of system architecture, memory controllers, and distributed compute environments.
Finally, translating a complex research concept into a clear and understandable prototype architecture was itself a challenge. The project involves ideas from multiple fields—AI infrastructure, distributed computing, cybersecurity, and quantum systems—so simplifying these ideas into a framework that can be demonstrated and evaluated was an important part of the development process.
Accomplishments that we're proud of
One of our biggest accomplishments was successfully designing a deterministic infrastructure model that addresses reliability and security challenges in modern AI systems. By introducing a validation layer between AI outputs and system execution, we demonstrated how probabilistic AI behavior can be converted into deterministic and verifiable actions.
We are also proud of developing the Biological-Digital Seal architecture, which integrates validation, synchronization stabilization, and identity-locked security into a unified framework. This approach shows how large-scale AI and distributed computing systems can operate with greater reliability and protection against malicious inputs.
Another major accomplishment was designing the Synchronization Suppression concept for distributed computing environments. Large AI clusters often experience signal noise and timing drift, and our architecture proposes a method for stabilizing communication between computing nodes while reducing redundant processing.
Finally, we are proud of establishing a foundation for real-world deployment through the development of a broader intellectual property portfolio. Multiple patent applications support the architecture, demonstrating a long-term commitment to developing deterministic infrastructure for AI, distributed computing, and secure autonomous systems.
What we learned
Through this project, we learned that the biggest challenge in modern AI systems is not just improving algorithms, but ensuring that AI outputs can be trusted when interacting with real-world systems. Probabilistic models are powerful for generating insights, but they require additional infrastructure to guarantee safe and reliable execution.
We also learned that system-level architecture matters as much as model performance. By introducing validation, synchronization control, and identity verification between AI outputs and execution layers, it becomes possible to significantly improve reliability and security in distributed computing environments.
Another key insight was the importance of hardware-aware design. Many existing AI safety approaches rely purely on software guardrails, but integrating validation mechanisms closer to the hardware layer can provide stronger guarantees for system stability and security.
Finally, this project showed us that developing solutions at the intersection of AI, distributed computing, and cybersecurity requires combining ideas from multiple disciplines. Translating complex technical concepts into a clear architecture that others can understand and build upon was an important part of the learning process.
What's next for Deterministic Quantum Infrastructure & Bio-Digital Gating
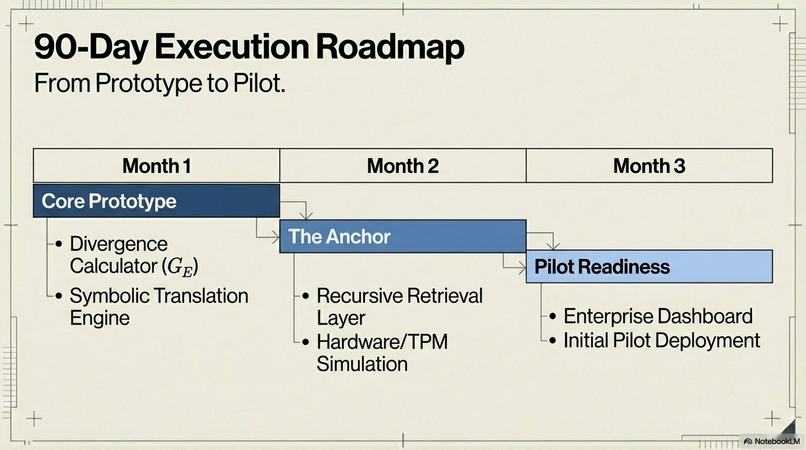
The next step for this project is to move from architectural design to prototype validation in real computing environments. We plan to develop a working implementation of the deterministic validation layer and test it within distributed AI systems to evaluate improvements in reliability, synchronization stability, and security.
A key focus will be building hardware-aware prototypes that integrate with modern computing infrastructure such as GPU clusters, edge devices, and distributed cloud systems. This will allow us to measure how deterministic validation and synchronization suppression affect performance, energy efficiency, and system stability.
Another important direction is exploring applications in high-reliability environments, including autonomous robotics, secure cloud infrastructure, energy systems, and distributed AI platforms. These areas require infrastructure that can safely translate AI-generated outputs into deterministic actions.
We also plan to continue developing the Biological-Digital Seal architecture by expanding its validation logic, strengthening identity-locked security mechanisms, and refining synchronization control for large-scale computing networks.
In the long term, the goal is to help establish a new infrastructure standard for AI systems, where probabilistic models remain flexible for learning and reasoning, while deterministic validation layers ensure safe, secure, and reliable operation in real-world environments.
Log in or sign up for Devpost to join the conversation.