Track: Security
Inspiration
We've all experienced the friction of multi-factor authentication — scrambling for a phone, switching between apps, waiting for a verification code. Authentication constantly interrupts your flow. And despite the hassle, these systems still fall short: codes can be intercepted, devices can be stolen, and users are left vulnerable without knowing it.
We started asking: what if authentication worked more like real life?
In the physical world, you don't prove identity by reciting codes — you prove it through presence. Your phone is with you. Your devices recognize you. Your routine is consistent.
That question led us to Keypr: a system that combines dedicated hardware with context-aware authentication. Security that works silently in the background, verifying trusted presence through proximity and hardware ownership — without ever interrupting your routine.
We wanted to build something as natural as carrying your keys.
Security should adapt to people — not the other way around.
What It Does
Keypr is a hardware-based, context-aware authentication system that modernizes multi-factor authentication by pairing a dedicated hardware key with a secure mobile app.
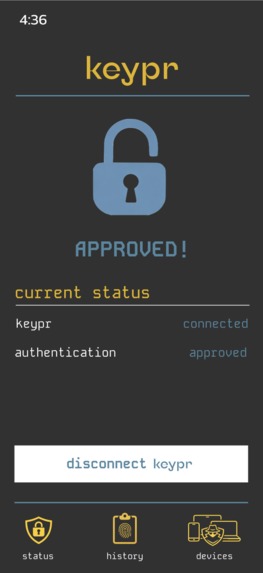
Instead of requiring codes or manual approval steps, Keypr silently verifies identity using proximity and trusted device presence. When an authentication request occurs, the hardware key communicates with the Keypr mobile app, which confirms that both the authorized hardware and phone are present. Access is then approved automatically — without interrupting the user.
Keypr delivers:
- Seamless authentication that never interrupts your workflow
- Strong protection against phishing, relay attacks, and credential theft
- A dedicated hardware key for secure identity verification
- A real-time mobile interface for approvals, denials, and device management
- Affordable, modern hardware-backed security accessible to everyone
How We Built It
Keypr is built around three tightly integrated components:
Hardware Device
A Bluetooth Low Energy (BLE) hardware key that securely represents the user's identity. The device confirms trusted presence through proximity-based communication and acts as a physical anchor of authentication. Its dedicated nature ensures identity cannot be replicated by software alone.
Mobile App
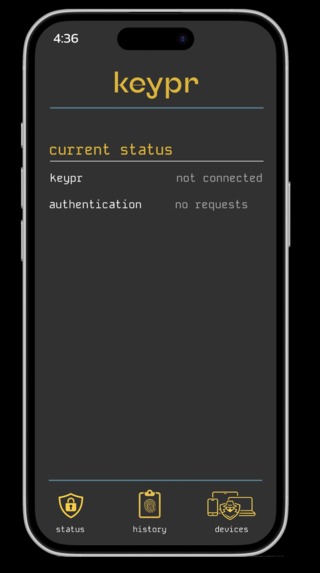
The Keypr mobile app connects to the hardware key via Bluetooth and serves as the secure bridge between the hardware and authentication client. It maintains device trust, manages authentication approvals, and provides real-time visibility into system status.
The app features a real-time dashboard displaying:
- Connection status
- Authentication requests
- Device trust state
- Approval and denial controls
All wrapped in a spy-inspired design system built to reflect silent, invisible security.
Authentication Client
A simulated protected resource that sends authentication requests into the Keypr system. Once an access request is initiated, the system verifies trusted presence through BLE communication between the hardware key and mobile device, and securely returns approval signals to grant access.
Challenges We Ran Into
Building Keypr from scratch in a hackathon environment pushed us into complex technical territory across hardware, mobile development, and security protocols.
Persistent Bluetooth Connections
Maintaining a stable, continuous BLE connection between the hardware key and mobile app proved more difficult than expected. BLE is optimized for short, intermittent communication rather than persistent sessions. We had to carefully manage connection state, detect and recover from dropped connections, and implement seamless reconnection logic — all while keeping the experience invisible to the user.
FIDO & CTAP Compatibility
Implementing compatibility with FIDO and CTAP standards required navigating dense protocol specifications and low-level communication flows. These standards define strict requirements for identity verification, attestation, and authentication messaging. We had to understand and implement secure handshake flows, structured binary messages, and correct protocol sequencing to ensure our implementation behaved like a true hardware passkey.
Learning Xcode & Swift Under Time Pressure
Neither of us had significant experience with Swift or Xcode prior to this project. We had to quickly learn a new language, development environment, and mobile architecture while simultaneously building a production-quality Bluetooth-integrated application. This required rapid iteration, debugging unfamiliar tools, and learning platform-specific patterns under tight hackathon constraints.
Accomplishments We're Proud Of
We started with an ambitious idea and successfully built a fully functional hardware-backed authentication system.
A Fully Working Physical Passkey
We implemented the complete authentication pipeline end-to-end — from hardware device to mobile app to authentication client. Seeing a physical hardware key securely trigger authentication approval in real time validated both our architecture and execution.
Mobile App Design & Implementation
We designed and built a cohesive mobile experience from scratch. The spy-inspired design language reinforces the concept of silent, invisible security while providing clear system feedback. The result is both functional and polished, demonstrating that strong security can coexist with excellent user experience.
Fully Custom CTAP Implementation
Rather than relying on external libraries, we implemented the CTAP protocol ourselves. This gave us deep insight into authentication protocols and allowed us to tailor the implementation specifically to Keypr's architecture. Building this from the ground up ensured full control over authentication flow, message handling, and security guarantees.
Secure Retrieval and Storage of Bluetooth Device Identity
We successfully implemented logic to programmatically retrieve the unique MAC address of paired Bluetooth devices and store it securely. This forms the foundation of Keypr's trust model, allowing the system to recognize and verify trusted hardware devices reliably across sessions.
What We Learned
Keypr provided hands-on experience across multiple domains including mobile development, embedded hardware, wireless communication, and authentication protocols.
Xcode & Swift Development
We learned how to build a full native iOS application using Swift and Xcode, including Bluetooth integration, state management, and UI architecture. We gained familiarity with Swift's type system, asynchronous programming model, and Apple's development ecosystem.
Hardware Passkeys and FIDO/CTAP Protocols
We developed a deep understanding of modern authentication protocols, including how hardware passkeys securely verify identity. This included learning authentication handshakes, attestation mechanisms, and secure message exchange patterns used in industry-standard authentication systems.
Bluetooth Low Energy (BLE) System Design
We learned how BLE communication works at a low level, including device discovery, services, characteristics, connection lifecycles, and proximity-based verification. We designed a system capable of maintaining reliable communication between hardware and software components.
Hardware-Software Integration Under Real Constraints
One of the most valuable lessons was learning how to design systems that span both hardware and software boundaries. Coordinating firmware behavior, mobile application logic, and authentication protocols required careful system design, debugging, and teamwork.
What's Next for Keypr
Keypr has strong potential beyond a hackathon prototype, and we see a clear path toward production-ready deployment.
Complete and Harden the Authentication Flow
We plan to refine and fully implement all aspects of the authentication lifecycle, including improved session management, error handling, and edge case handling. This will ensure reliability and security under real-world conditions.
Authentication History and Transparency
We want users to have full visibility into their authentication activity. Future versions will include a secure history of authenticated services and sessions, viewable in both the mobile app and hardware device. This provides transparency and helps users understand when and where their identity is being used.
Production-Ready Hardware Design
The current Keypr hardware is a functional prototype. Future iterations will focus on improving physical design, battery efficiency, durability, and manufacturability. Our goal is a compact, reliable, and premium hardware key suitable for everyday use.
Expand Toward Real-World Deployment
We plan to integrate Keypr with real authentication systems, enabling compatibility with websites, applications, and enterprise identity platforms. Our long-term goal is to create an authentication layer that is invisible, secure, and effortless.

Log in or sign up for Devpost to join the conversation.