Inspiration
Every day, security vulnerabilities slip into production, hardcoded AWS keys, SQL injection in a new endpoint, an outdated dependency with a known CVE. Most teams catch them too late, after code is merged and deployed. The consequences range from embarrassing to catastrophic: data breaches, leaked credentials, compliance failures.
Manual security reviews don't scale. Developers context-switch between writing features and remembering security best practices. Static analysis tools produce walls of noisy reports that get ignored. And when a secret does leak, the remediation process is manual, error-prone, and slow. We asked ourselves: what if a team of AI agents could act as a dedicated security team, continuously scanning, reviewing, remediating, and even optimizing your CI/CD for sustainability? Not just flagging problems, but actually fixing them automatically.
What it does
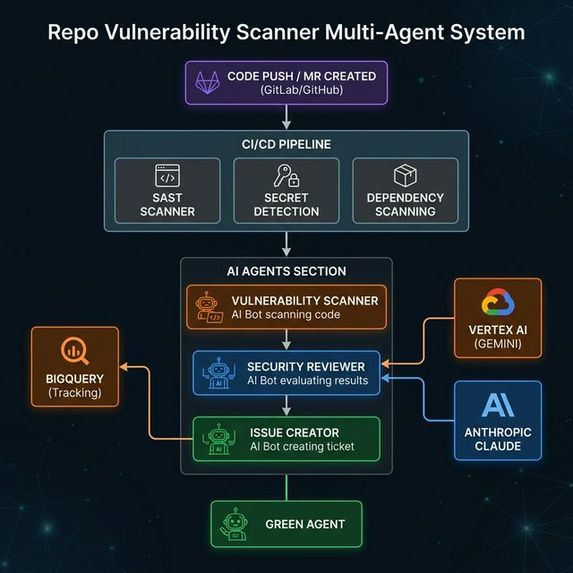
Repo Vulnerability Scanner is a multi-agent security platform for GitLab, built on the Duo Agent Platform. It combines 6 specialized AI agents and 2 orchestration flows to provide continuous, automated security coverage.
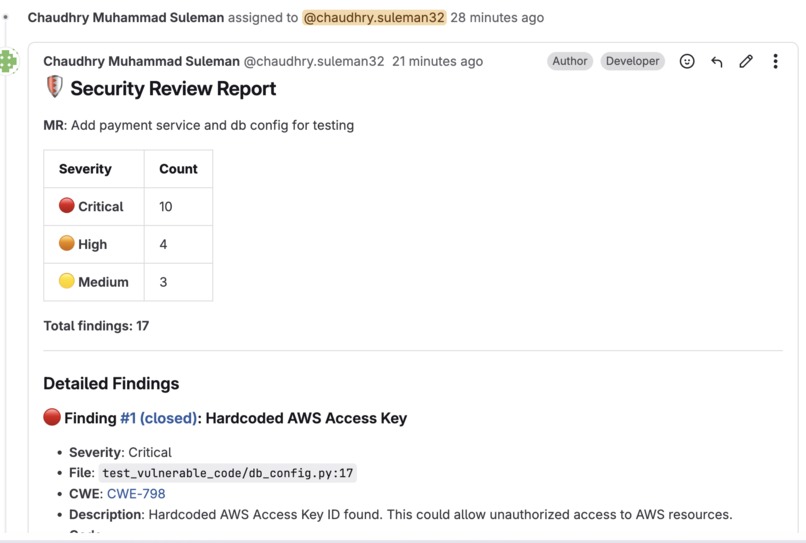
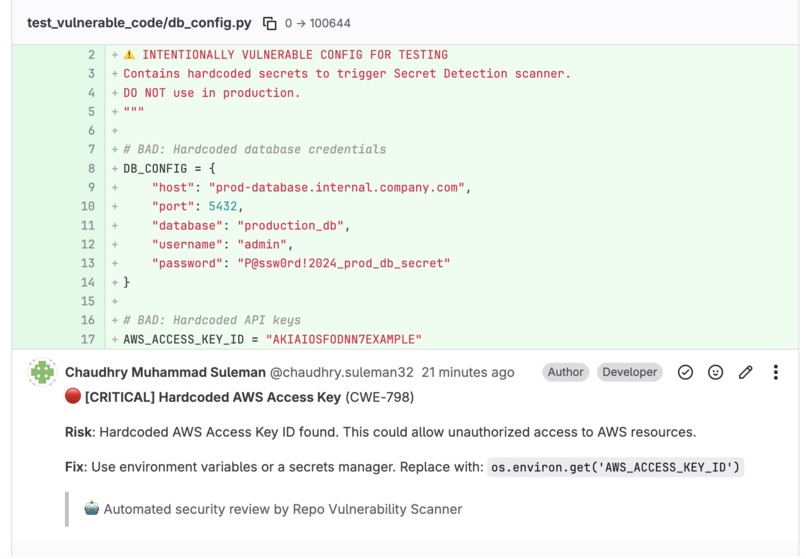
The system performs a systematic 7-step security audit spanning reconnaissance, secret detection, dependency analysis, code vulnerability scans, and configuration audits. It reviews merge request diffs for security anti-patterns and posts inline code comments with severity levels and concrete fix suggestions directly on the vulnerable lines.
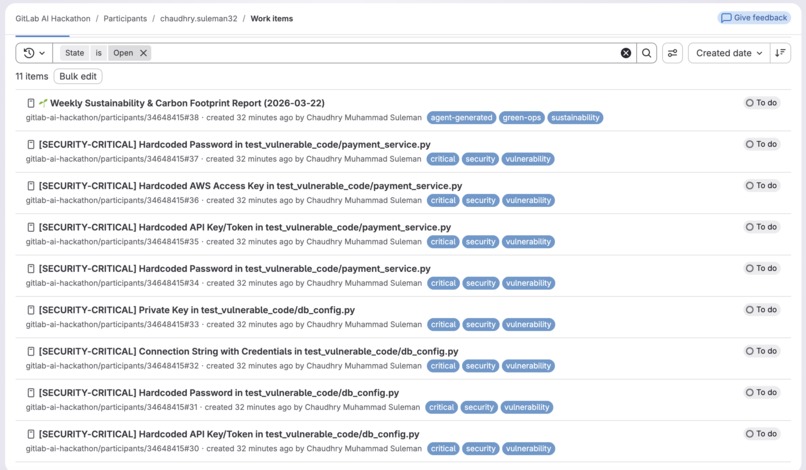
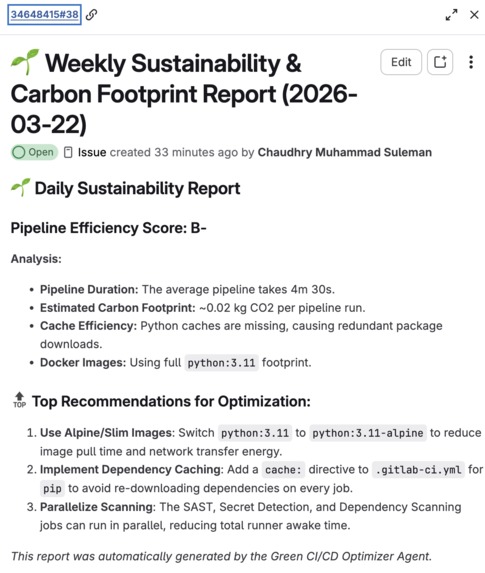
Beyond just detecting issues, when a hardcoded secret is found, the Secret Remediator agent automatically extracts it to an environment variable, updates the CI/CD configuration, adds a masked project variable via the GitLab API, creates a new branch, and opens a fix merge request. The platform also brings sustainability into DevSecOps by estimating pipeline carbon footprints, identifying redundant jobs, and generating sustainability reports with efficiency grades. Additionally, an IDE-first agent allows developers to generate, analyze, debug, and optimize deployment pipelines using plain language without leaving their editor.
How we built it
We built entirely on the GitLab Duo Agent Platform, with all agents powered by Anthropic Claude through GitLab Duo for intelligent reasoning and decision-making.
Our architecture consists of 6 custom agents defined in YAML, each with a specialized system prompt and a curated set of tools. These are orchestrated by multi-agent flows that chain the agents together in logical sequences (like scan → validate → report). We integrated this with an automated CI/CD pipeline using GitLab's security scanning templates alongside custom jobs.
To enhance the scanning capabilities, we built a Python-based Model Context Protocol (MCP) server that exposes tools powered by Google Cloud: Vertex AI for deep code analysis, Secret Manager for secret classification, and BigQuery for tracking vulnerability trends.
The scanner works by combining three complementary approaches: regex pattern matching for fast deterministic checks, Anthropic Claude via GitLab Duo for contextual reasoning and false positive reduction, and Google Vertex AI Gemini 2.0 Flash via MCP for deep analysis like tracing data flow across functions and detecting complex business logic flaws.
Challenges we ran into
Reducing false positives was our biggest challenge. Early versions flagged test files, documentation examples, and commented-out code. We solved this by combining fast regex scanning with AI-powered validation, Claude analyzes the context around each finding to determine if it's a real vulnerability or a false alarm.
MCP server resilience required careful engineering. The server needed to work perfectly with GCP credentials and without them. We implemented graceful fallback for every tool, so the scanner always works locally connecting GCP just makes it smarter.
Inline MR comment positioning was surprisingly tricky. GitLab's API for posting comments on specific lines of a diff requires precise line mapping between scan results and the MR diff positions. Getting the old/new line number mapping right across additions, deletions, and modifications took significant debugging.
Automated secret remediation was the most complex feature to build. Creating an agent that can safely update source code, modify CI/CD configurations, interact with the GitLab API to store secrets, commit to a new branch, and open an MR reliably required extensive prompt engineering and robust error handling.
Accomplishments that we're proud of
We achieved true end-to-end automation. From a simple code push, the system performs an AI security review, posts inline comments on vulnerable lines, auto-creates issues, and sends email alerts to the team with zero manual steps required.
We are incredibly proud of our secret auto-remediation capability. We went beyond just finding leaked secrets to actually fixing them by extracting them to environment variables, updating the pipeline config, and opening a fix MR.
Our three-layer intelligence design — combining regex, Claude, and Gemini — catches significantly more vulnerabilities than any single approach while keeping false positives remarkably low. We also successfully introduced sustainability as a first-class concern in CI/CD pipeline optimization, bringing carbon footprint awareness directly into the developer workflow.
What we learned
We learned that the Duo Agent Platform is exceptionally powerful for building specialized developer tools. Defining agents in YAML with curated tool sets keeps them focused and effective. We discovered that the constraint of selecting only the tools an agent strictly needs forces better, more reliable autonomous behavior.
We also learned that the Model Context Protocol (MCP) is a game-changer for securely connecting AI agents to external services. Furthermore, combining multiple AI models (Claude for reasoning and Gemini for deep analysis) produces significantly better results than relying on a single model. Finally, the difference between an agent that reports an issue and one that takes action to fix it is enormous — action-taking agents deliver exponentially more value.
What's next for Repo Vulnerability Scanner
Our immediate next step is integrating Dynamic Application Security Testing (DAST) for runtime vulnerability detection. We also plan to expand our auto-fix merge request capabilities beyond secret remediation to address common code vulnerabilities like SQL injection via parameterized queries and XSS via output encoding.
We will be building a comprehensive real-time security posture dashboard powered by BigQuery historical data to visualize vulnerability trends. Finally, we want to implement team security scoring with gamified metrics to encourage secure coding practices, along with a custom rule engine that lets teams define their own security patterns and compliance rules through simple YAML configuration.
Built With
- anthropic
- gitlab
- google-bigquery
- google-cloud
- mcp
- python
- sast
- secret-scanning
- vertex-ai
- yaml


Log in or sign up for Devpost to join the conversation.