You haven't signed in yet, you can have a better experience after signing in
 Code Virtualizer Code Virtualization Confusion System Tool Software
Code Virtualizer Code Virtualization Confusion System Tool Software
Activity Rules
1、Activity time:{{ info.groupon.start_at }} ~ {{ info.groupon.end_at }}。
1、Activity time:cease when sold out。
2、Validity period of the Group Buying:{{ info.groupon.expire_days * 24 }} hours。
3、Number of Group Buying:{{ info.groupon.need_count }}x。
Please Pay Attention
1、Teamwork process: Join/initiate a Group Buying and make a successful payment - Within the validity period, the number of team members meets the activity requirements - Group Buying succeeded!
2、If the number of participants cannot be met within the valid period, the group will fail, and the paid amount will be refunded in the original way.
3、The number of people required and the time of the event may vary among different products. Please pay attention to the rules of the event.
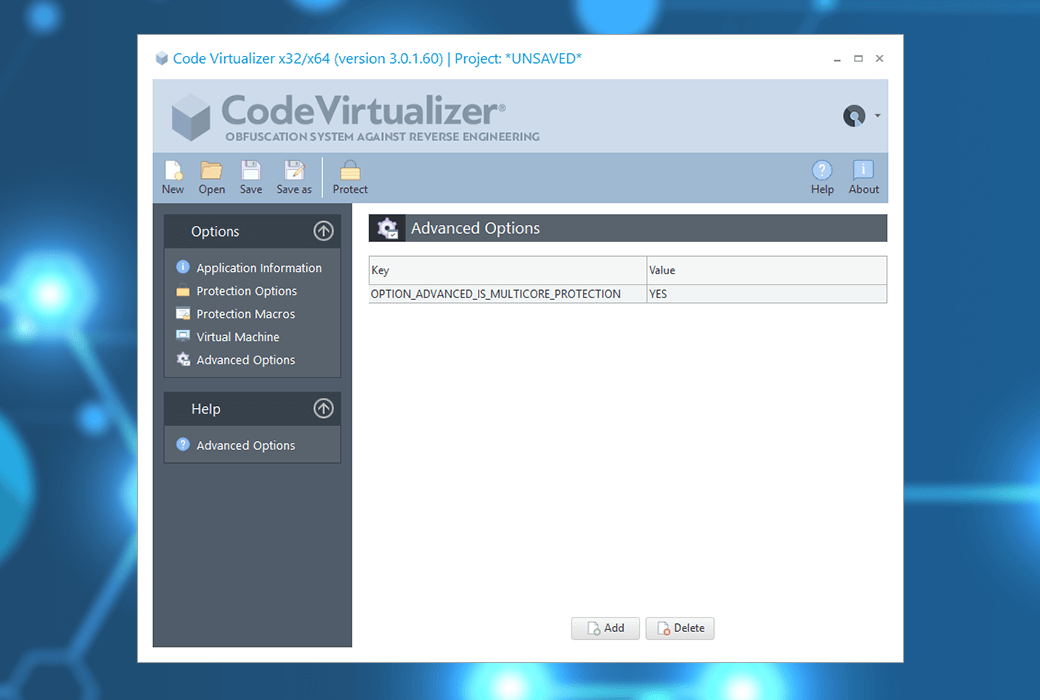
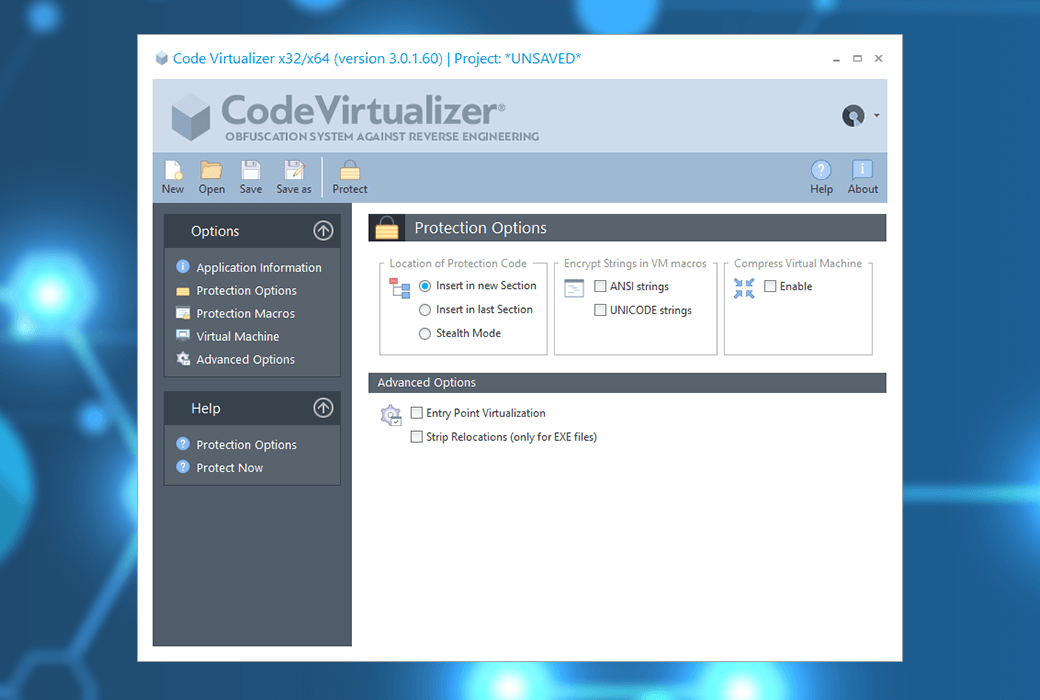
Code Virtualizer is a powerful code obfuscation system suitable for Windows, Linux, and Mac applications and dynamic libraries. It helps developers protect their sensitive code areas from the threat of reverse engineering through powerful obfuscation of code based on code virtualization.
Code Virtualizer will convert your original code (x86/x64 or ARM64 instructions) into virtual opcodes that can only be understood by internal virtual machines. These virtual opcodes and virtual machines themselves are unique to each protected application, thus avoiding generic attacks on Code Virtualizer.
Code Virtualizer can protect your sensitive code areas, covering any x86/x64 or ARM64 native PE, ELF, or Mach-O files (such as executable files/EXEs, system services, DLLs, OCXs, ActiveX controls, shared objects, screen savers, and device drivers).
Basic knowledge about reverse engineering
When an application is created, the compiler compiles the application source code into multiple object files composed of machine language code. Subsequently, these target files will be linked together to create the final executable file.
When an attacker attempts to crack a compiled application, they use a decompilation tool that decompiles machine language code into more understandable code (such as assembly code or high-level programming language), and then they study the decompiled code.
Once the attacker has a thorough understanding of the target application, they can modify the compiled application to alter its behavior. For example, attackers can bypass the routine of checking the trial period in the application, making it run permanently, or even worse, making the application appear as if it has been registered.
Code virtualization adversarial reverse engineering
Code virtualization refers to the conversion of binary code from a specific machine into different binary code that another machine can understand. That is to say, the instruction set of a specific machine is converted into a new instruction set that another machine can understand. The following figure shows the conversion process from Intel x86 instruction blocks to a new instruction set for another machine (specifically RISC 32-bit CPU):
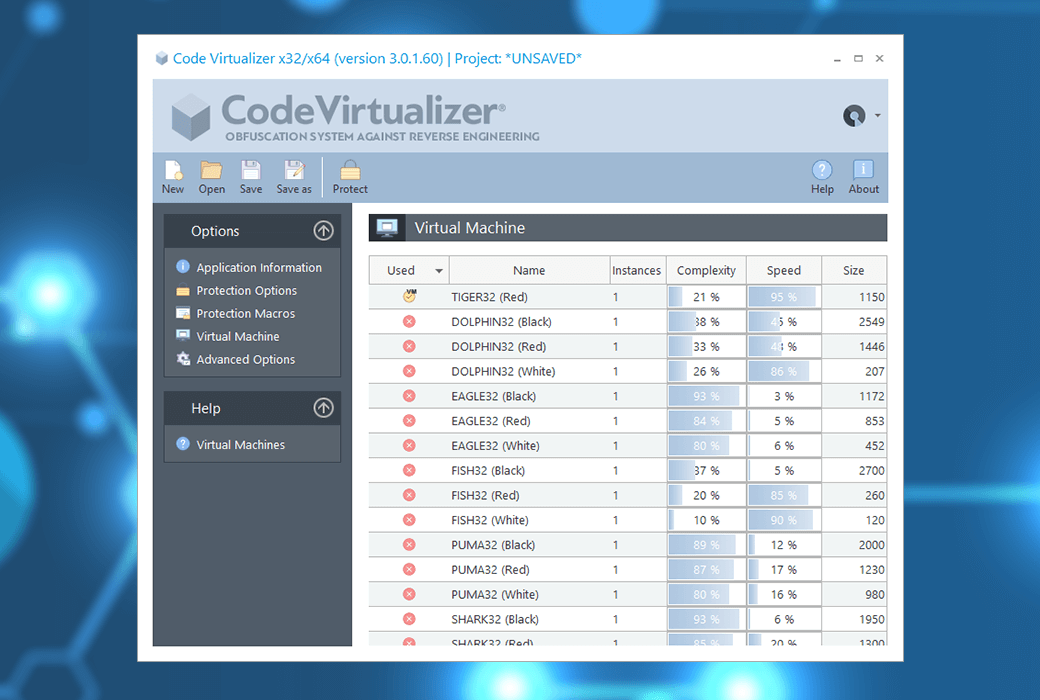
Code Virtualizer can generate multiple types of virtual machines, each with its unique instruction set. This means that specific x86/x64 or ARM64 instruction blocks can be converted into different instruction sets for each virtual machine, preventing attackers from recognizing any generated virtual opcodes after converting from x86/x64 or ARM64 instructions. The following figure shows how to convert x86 instruction blocks into different types of virtual opcodes, which can be simulated by various virtual machines:
When an attacker attempts to decompile a code block protected by Code Virtualizer, they will not find the original x86 instructions. On the contrary, he will discover a completely new instruction set that neither he nor any special decompiler can recognize. This will force attackers to go through an extremely difficult process of identifying the execution mode of each opcode and the working principle of each protected application's specific virtual machine. Code Virtualizer completely confuses the execution of virtual opcodes and the study of each unique virtual machine to prevent others from investigating the execution of virtual opcodes.
The Application of Code Virtualization in Real Life
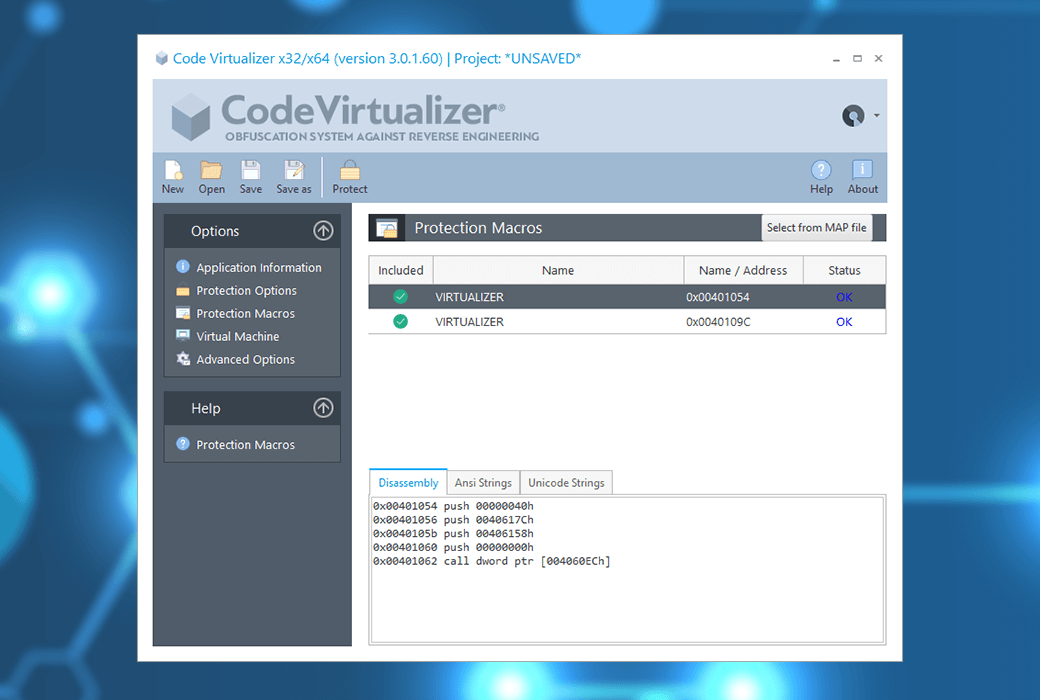
Code Virtualizer can be easily embedded into your applications, libraries, and device drivers. You only need to select the area in the source code that will be protected by the Code Virtualizer. The following example demonstrates how to protect code blocks in a C application:
#include <stdio.h>
#include "VirtualizerSDK.h"
void main()
{
VIRTUALIZER_START//The area to be protected starts from here
printf("Hello World");
VIRTUALIZER-IND//The area to be protected ends
}
The VIRTUALIZER-START and VIRTUALIZER-IND macros are virtual macros that do not interfere with the execution of the original application program. Only when protected, the Code Virtualizer recognizes these code regions and converts them into unique virtual opcodes, which are then simulated by the virtual machine when the protected application is running.
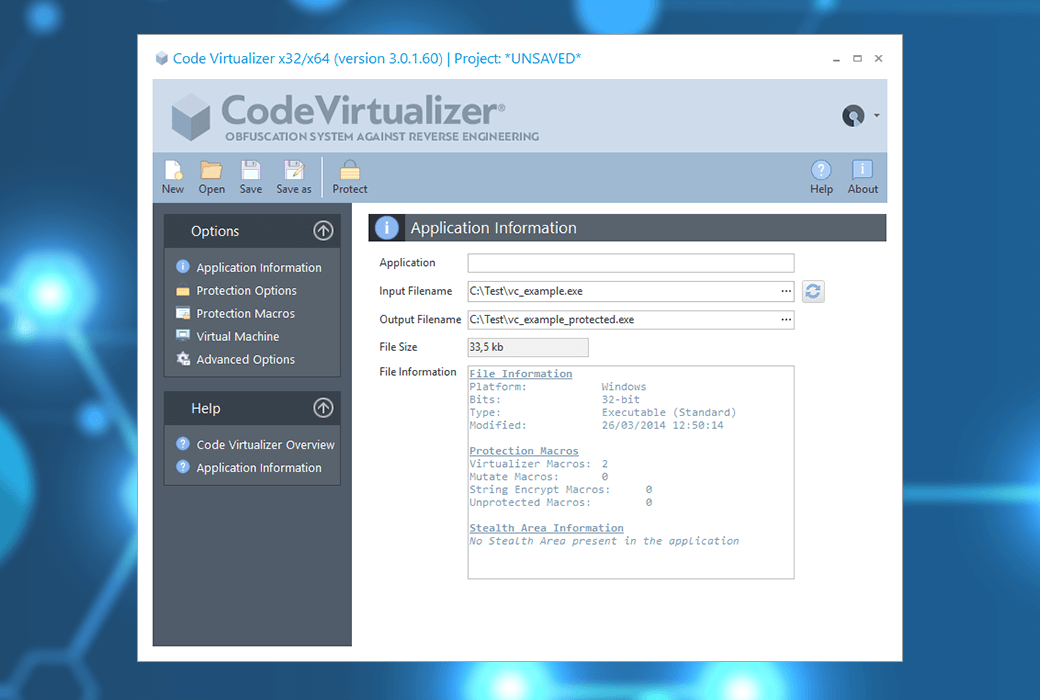
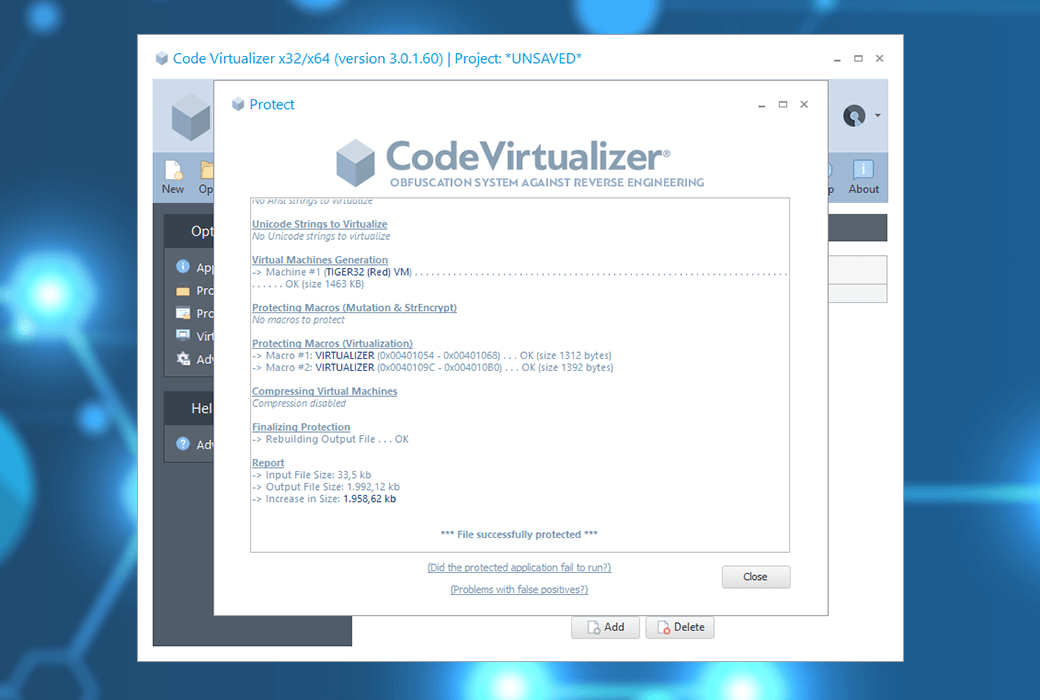
The following figure shows the image of the original compiled application (before being protected) and the changes after being protected by Code Virtualizer:
As shown in the figure, the Code Virtualizer needs to embed the generated virtual machine at the end of the protected application to simulate virtual opcodes during execution.
Code Virtualizer is a powerful technology that can prevent others from checking your sensitive code, such as verifying the serial number entered to register your application's routines. In addition, Code Virtualizer has slightly modified the header of protected applications, which means you can add compressors or other software protection tools on top of Code Virtualizer without any issues.
If you are a Windows device driver developer and feel neglected when there is no solution to protect your device drivers, Code Virtualizer provides you with the same technology as applications and DLLs (applicable to 32-bit and 64 bit drivers) to protect your device drivers.
Here is the Code Virtualizer ® Main functions:
- Confusing through multiple virtual machines
- Each protected application has unique protection
- Protect x86/x64/ARM64 applications, libraries, and device drivers
- Advanced Mutation Engine
- Code relocation to protect dynamic libraries and device drivers
- Virtualize/emulate any x86/x64/ARM64 opcode in a unique virtual machine
- Each protected application has a unique virtual opcode
- Fully compatible with any compressor/protector
- Command line protection
- And more!
Official website:https://www.oreans.com/CodeVirtualizer.php
Download Center:https://codevirtualizer.apsgo.cn
Delivery time:manual processing
Operating Platform:Windows
Interface language:Support English interface display.
Update Description:Support 1-year maintenance and updates after purchase.
Trial before purchase:Free trial is available before purchase.
How to receive goods:After purchase, the activation information will be sent to the email address at the time of placing the order, and the corresponding product activation code can be viewed in the personal center, My Orders.
Number of devices:Can install one computer.
Replace computer:Uninstall the original computer and activate the new computer.
Activation guidance:To be added.
Special note:To be added.
reference material:https://www.oreans.com/help/tm/

Any question
{{ app.qa.openQa.Q.title }}